DannyHamilton
Legendary

 Offline Offline
Activity: 3388
Merit: 4653

|
But, most pools use ASICS only which perform SHA-256 only- so- (someone correct me if i'm wrong here.)- it would be wrong to compare the "computing"/hash power of a pool to generating addresses.
You are correct. The ASICs used by mining pools are not capable of generating bitcoin addresses. However, lets use our imagination and create a world where some very wealthy person decides to invest all of their wealth into creating special ASICs that are capable of generating Bitcoin addresses. Lets imagine that they are able to generate addresses at the same rate that the current bitcoin network is capable of generating hashes. In other words, lets imagine that they can generate 115,000,000,000,000,000,000 addresses per second. There are 2 160 different bitcoin addresses of the type that start with a 1 (legacy, P2PKH). (2 160 addresses) / (115 X 10 18 addresses per second) = 1.27 X 10 28 seconds. So, it would take about 1,270,000,000,000,000,000,000,000,000,000 seconds to generate all possible addresses (assuming you never generated the same address twice). The estimated time that the universe has existed since the "Big Bang" is about 13.772 Billion Years. (13,772,000,000 years) X (31,557,600 seconds per year) = 434,611,267,200,000,000 seconds since the beginning of the universe. So, the universe has existed for approximately 4.35 X 10 17 seconds. This means that if you used all that imaginary address generating power and started generating addresses at the moment that the Big Bang happened... By now, you would have generated approximately: (4.35X10 17 seconds in the universe) / (1.27 X 10 28 seconds to generate ALL addresses) = 0.00000343% of all possible addresses. To generate all the possible addresses (assuming you never generated the same address twice), it would require you to continue generating addresses for another: (1.27 X 10 28 seconds to generate ALL addresses) / (4.35 X 10 17 seconds in the universe) = 29,195,402,299 entire universes worth of time. |
|
|
|
|
|
|
|
|
|
|
|
According to NIST and ECRYPT II, the cryptographic algorithms used in
Bitcoin are expected to be strong until at least 2030. (After that, it
will not be too difficult to transition to different algorithms.)
|
|
|
Advertised sites are not endorsed by the Bitcoin Forum. They may be unsafe, untrustworthy, or illegal in your jurisdiction.
|
|
|
|
|
HCP
Legendary

 Offline Offline
Activity: 2086
Merit: 4316
<insert witty quote here>

|
 |
November 07, 2019, 11:04:18 PM
Last edit: November 15, 2023, 07:14:35 AM by HCP |
|
Isn't it true that even if we add a passphrase to secure our wallet, it does not add any security locks to the seed...
You need to be careful with the term "passphrase" when used in relation to seeds (assuming you're talking about BIP39 seed mnemonics). In some instances, this is simply a wallet "passphrase" (such as the one used in Electrum) and is used for encrypting data within the wallet file or encrypting the wallet file itself. In other instances, it refers to the BIP39 "passphrase"... which does actually add a "security lock" of sorts to your seed mnemonic. This is commonly referred to as the "25th word" (although it doesn't need to be a single word, but can be a sentence or phrase or random characters). All BIP39 wallets should provide this functionality. By using the "25th word" passphrase, even if your seed mnemonic itself was compromised, the attacker would have no way to replicate your actual private keys without the "25th word" passphrase. ... and if seed is compromised, the wallet software will not ask for the old passphrase but a new passphrase to the person who hacked it, right?
The situation you are referring to, is like the simple "wallet password" functionality in Electrum... all that does is encrypt the data in the wallet file, or encrypts the entire file depending on your settings. That password is ONLY relevant to that specific copy of the wallet file. In this instance, if someone were to get access to your seed mnemonic, they could generate their own copy of your wallet file by restoring from your seed mnemonic, that has NO password (or a password of their own choosing). You should note that Electrum ALSO allows you to seed a "25th word" passphrase in addition to the wallet password... and they don't need to be the same! The terminology used in Electrum is "Extend your seed with custom words"... and accessed by clicking the "Options" button when creating (or restoring) the wallet: 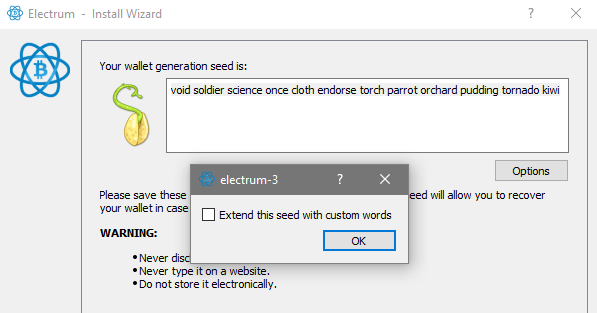 |
|
|
|
HeRetiK
Legendary

 Offline Offline
Activity: 2926
Merit: 2091
Cashback 15%

|
 |
November 08, 2019, 11:20:09 AM |
|
Then you didn't get what I have intended to say, There are 2256 private keys. There are 2160 legacy addresses calculated from those keys by applying RIPEMD-160 to SHA-256 hash of those keys. It means at the end we have collision as only 2160 legacy addresses will correspond to the whole set of 2256 private keys. Roughly each address can be accessible through the set of 296 keys.
Ah... sorry, now I get what you mean. Yes, that sounds about right. To generate all the possible addresses (assuming you never generated the same address twice), it would require you to continue generating addresses for another:
(1.27 X 1028 seconds to generate ALL addresses) / (4.35 X 1017 seconds in the universe) = 29,195,402,299 entire universes worth of time.
Let's not forget though that assuming Moore's Law applies to this hypothetical technology we'd only have about 70 years until computation time will be reduced to a single universe worth of time. Just sayin' (70 years of computation power doubling every two years => 2^35 = 34,359,738,368 times the computation power you started with. Yes I'm aware that technically that's neither what Moore's Law states nor how any of this works.) |
.
.HUGE. | | | | | | █▀▀▀▀
█
█
█
█
█
█
█
█
█
█
█
█▄▄▄▄ | ▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀
.
CASINO & SPORTSBOOK
▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄ | ▀▀▀▀█
█
█
█
█
█
█
█
█
█
█
█
▄▄▄▄█ | | |
|
|
|
o_e_l_e_o
In memoriam
Legendary

 Offline Offline
Activity: 2268
Merit: 18512

|
 |
November 08, 2019, 12:10:22 PM |
|
That means that each single key may correspond roughly to 2256 / 2160 = 296 addresses, right?
Roughly each address can be accessible through the set of 296 keys. Your first statement is the wrong way round, but your second statement is correct. There are 2 96* private keys per address if they are all distributed evenly. *Actually slightly less, since there are slightly less than 2 256 total private keys, but the difference is minuscule. |
|
|
|
|
Klarks_C
Jr. Member

 Offline Offline
Activity: 352
Merit: 2

|
 |
November 08, 2019, 01:42:18 PM |
|
(give or take a couple orders of magnitude) I'd say give a few dozen orders of magnitude.  Assuming the human race has spread across multiple planets in the next 10 billion years, lets give a generous population estimate of 1 trillion individuals. Even if every single one of those 1 trillion people generates 100 new bitcoin private keys every day (why anyone would need that many I don't know) for 10 billion years, we are still only talking about (1 trillion * 100 * 10 billion * 365) = 3.65*10 26 keys. For OP, even in my hypothetical scenario above, we would still only have generated approximately 0.0000000000000000000000000000000000000000000000003% of all possible private keys. If we continued to use bitcoin for a trillion trillion trillion years, then we might have to start worrying about collisions, but given that all the stars in the universe will die in only 100 trillion years, we will probably have more pressing issues to deal with. But there are chances you may get your seeds or phrases randomly guessed by someone and a person who is intentionally doing it, gets lucky some day. Only if you are silly enough to pick your own seed phrase or use a brainwallet. If you use a proper randomly generated seed phrase, the chances of someone guessing it are essentially the same as the chances of someone generating the same seed as you, as has been outlined above, i.e. never going to happen. Ok, Now using the computation power used by a mining pool, what's the time needed to generate all the possible addresses ?? infinite, well not really. Depending on the source you use, you can calculate the time it would take to generate all possible adresses. Some more info can be found here-> https://bitcoin.stackexchange.com/questions/2847/how-long-would-it-take-a-large-computer-to-crack-a-private-keyBut, most pools use ASICS only which perform SHA-256 only- so- (someone correct me if i'm wrong here.)- it would be wrong to compare the "computing"/hash power of a pool to generating addresses. Thank you, but, about this, when it takes 3 hours to compute for " 1Bitcoi" prefix, 3 hours is sufficient to generate billions addresses if you see what I mean 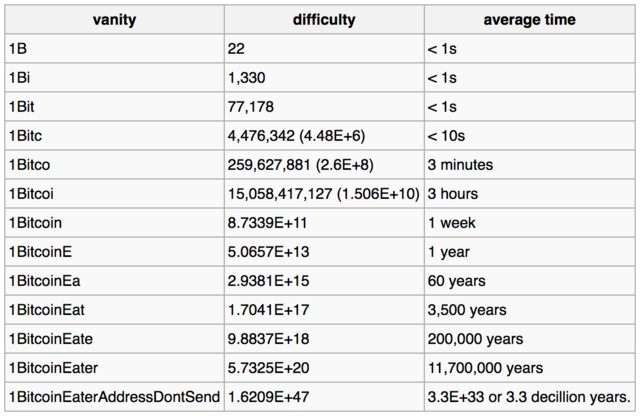 |
|
|
|
|
AdolfinWolf
Legendary

 Offline Offline
Activity: 1946
Merit: 1427

|
 |
November 08, 2019, 01:46:14 PM
Last edit: November 08, 2019, 02:18:42 PM by AdolfinWolf |
|
Thank you, but, about this, when it takes 3 hours to compute for 1Bitcoi prefix, 3 hours is sufficient to generate billions addresses if you see what I mean 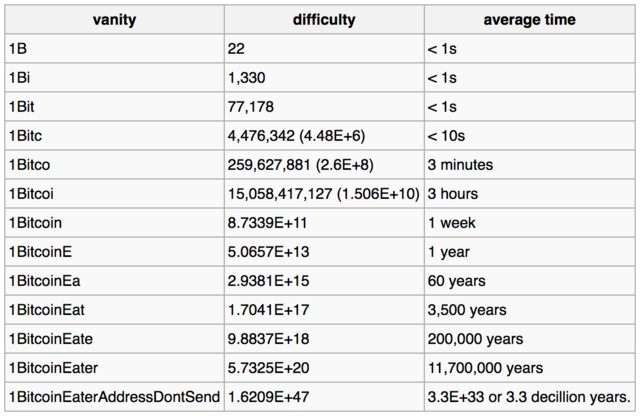 Well yes, but a billion adresses still is absolutely nothing. See Danny Hamiltons answer to put things in perspective. 2^30 (≈≈a billion) vs 2^160 (all the adresses in existence, well- let's just assume that for simplicity) - the difference is unimaginable. But, most pools use ASICS only which perform SHA-256 only- so- (someone correct me if i'm wrong here.)- it would be wrong to compare the "computing"/hash power of a pool to generating addresses.
You are correct. The ASICs used by mining pools are not capable of generating bitcoin addresses. However, lets use our imagination and create a world where some very wealthy person decides to invest all of their wealth into creating special ASICs that are capable of generating Bitcoin addresses. Lets imagine that they are able to generate addresses at the same rate that the current bitcoin network is capable of generating hashes. In other words, lets imagine that they can generate 115,000,000,000,000,000,000 addresses per second. There are 2 160 different bitcoin addresses of the type that start with a 1 (legacy, P2PKH). (2 160 addresses) / (115 X 10 18 addresses per second) = 1.27 X 10 28 seconds. So, it would take about 1,270,000,000,000,000,000,000,000,000,000 seconds to generate all possible addresses (assuming you never generated the same address twice). Replace 115*10^18 by 2^30 ( ≈a billion p second ), and you can perhaps put things into perspective a bit better. |
|
|
|
Dabs
Legendary

 Offline Offline
Activity: 3416
Merit: 1912
The Concierge of Crypto

|
 |
November 08, 2019, 03:53:28 PM |
|
I did say, a lot of people really do not understand time beyond a thousand years, much less millions or billions or the age of the universe. It's easy to say that there are so many grains of sand on the planet, but people can't even think to count how many there are in a single beach. It's simply too abstract, and yet they try to understand it; you have to look at it from a different perspective and we really can't teach that to some people, they just won't get it. It's almost like, you have to intentionally not get it, to get it. Are there more grains of sands on earth or are there more stars in the universe? Obviously, grains and stars can't be counted, not literally. But you can guestimate. I was asked this or pondered this when I was 6 or 8 years old or something like that. Current estimates puts sand grains = 7.5 x 10^18 = seven quintillion, five hundred quadrillion grains of sand. Stars = 70 thousand million, million, million million stars in the observable universe (a 2003 estimate) so we got multiple stars for every grain of sand. It just makes sense, since our planet is a small one, it's fixed, its finite, whereas the stars, we haven't been able to go much beyond our own planet (ok, the moon, mars, maybe the solar system)... However, if you get 10 drops of water, the number of H2O molecules is about the number of stars we know of. Now start talking about private keys or BTC addresses, and it's all electronic with no physical manifestation, and ... think of it as molecules or atoms in water drops. Really really tiny small thingies that exist (or don't exist) in the blockchain. Humans simply can not handle "the biggitude." We are surrounded by vastness. To the question, I think astronomer Carl Sagan once stated that "there are more stars in our Universe than there are grains of sand on all the beaches on Earth". https://www.worldatlas.com/articles/are-there-more-grains-of-sand-or-stars-in-the-earth.htmlHave fun. Oh, to answer the original question, are all BTC addresses really unique? For all practical intents and purposes, they are. Technically, they are limited but to such large numbers that most people simply can not understand there is no chance it happens. Don't sound like that guy "soooo, there is a chance?" ... |
|
|
|
HCP
Legendary

 Offline Offline
Activity: 2086
Merit: 4316
<insert witty quote here>

|
 |
November 08, 2019, 04:43:26 PM |
|
Don't sound like that guy "soooo, there is a chance?" ...
But there is!  Seriously tho... the way to sum this up is by defining the the difference between "Possible" and "Probable". Yes, it is technically possible that there could be a collision... as the chance is non-zero after all! However given the enormity of the set space etc, the odds are so incredibly incredibly INCREDIBLY tiny that it just is NOT probable. In fact, it is so improbable, that for all intents and purposes it is regarded as "impossible". |
|
|
|
|
naska21
|
 |
November 08, 2019, 07:22:48 PM |
|
That means that each single key may correspond roughly to 2256 / 2160 = 296 addresses, right?
Roughly each address can be accessible through the set of 296 keys. Your first statement is the wrong way round, but your second statement is correct. There are 2 96* private keys per address if they are all distributed evenly. *Actually slightly less, since there are slightly less than 2 256 total private keys, but the difference is minuscule. My bad, mine first assertion is totally reversing black and white, perhaps I have been deeply drunk when I wrote that.  What I actually meant is expressed by the second one. And agree, all that is correct only at even distribution. |
|
|
|
|
Dabs
Legendary

 Offline Offline
Activity: 3416
Merit: 1912
The Concierge of Crypto

|
 |
November 08, 2019, 08:30:11 PM |
|
Once the odds of anything exceed a few billion I usually say it is impossible, in casual conversations, depending on the topic we are talking about. Winning the lottery is still possible and probable, but so is the chance of getting struck by lightning. Recovering data from a spinning platter HDD that has been zero wiped ONCE by DBAN, = impossible. Bitcoin same address from a million different wallet users = impossible. Cracking any randomly generated password longer than 16~20 characters through brute force = impossible. (this depends, but ... bleh.) Mine the next bitcoin block solo using your CPU = impossible. Mine the next bitcoin block solo with the latest GPU = impossible. Mine any other altcoin with CPU/GPU = oh, still possible, probably need to go on pool though. Yah... soooo, there is a chance ... right; keep dreaming .  |
|
|
|
o_e_l_e_o
In memoriam
Legendary

 Offline Offline
Activity: 2268
Merit: 18512

|
 |
November 09, 2019, 09:55:25 AM |
|
but so is the chance of getting struck by lightning. This is the bottom line. If you are worried about the odds of someone randomly generating your address and stealing all your coins, then you should be paralyzed with fear about the odds of other far more terrible things things happening to you. We've already established there are 2 160 addresses. Assuming a 16 digit credit card number, with a 3 digit security code and an expiry month at some point in the next 5 years (60 potential months), then there are only 6*10 20 possible combinations. So the chance of someone randomly entering your credit card details correctly is somewhere around 2.4 billion billion billion times more likely than them randomly generating a private key linked to your address. About 1 in 10,000 people have a brain aneurysm that they didn't know about rupture every year, and around 15% of those people die within a couple of minutes. So you have about a 1 in 67,000 chance of immediate, sudden, and unpredictable death at any time just from a brain aneurysm. 1 in 67,000 is about 22 million trillion trillion trillion times more likely than 1 in 2 160. |
|
|
|
|
Stedsm
Legendary

 Offline Offline
Activity: 3052
Merit: 1273

|
 |
November 14, 2019, 03:27:33 PM |
|
Well, my thinking says that those who'd use the same address again and again might have the unnatural fear of getting their address/es compromised at some point, but if we keep changing the receiving addresses every single time, is there any need for this discussion that remains? Are the combinations going to be limited to those billions of addresses already generated even if the whole world accepts BTC and starts using new receiving address for each of their transaction?
Correct me if I'm wrong, but we don't use more than single address not because we want to prove it that it's ours, but because a used address doesn't get charged higher fees compared to a newly generated one?
|
| .SHUFFLE.COM.. | ███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████ | ███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████ | .
...Next Generation Crypto Casino... |
|
|
|
o_e_l_e_o
In memoriam
Legendary

 Offline Offline
Activity: 2268
Merit: 18512

|
 |
November 14, 2019, 04:07:25 PM |
|
I really don't follow your comment. Well, my thinking says that those who'd use the same address again and again might have the unnatural fear of getting their address/es compromised at some point, but if we keep changing the receiving addresses every single time, is there any need for this discussion that remains? Not reusing addresses is good for privacy, but it doesn't do anything for your security or protect against your keys being compromised. Are the combinations going to be limited to those billions of addresses already generated even if the whole world accepts BTC and starts using new receiving address for each of their transaction? Even if everyone in the world generates thousands of new addresses each day, we won't even get through a tiny fraction of a single percent of all new addresses before the death of the universe. Correct me if I'm wrong, but we don't use more than single address not because we want to prove it that it's ours, but because a used address doesn't get charged higher fees compared to a newly generated one?
The only difference in fee between addresses is if you are using legacy, nested SegWit, or native SegWit. There is no difference in fee whether it's the first transaction from a new address or the ten thousandth transaction from a 10 year old address. |
|
|
|
|
|
|
Dabs
Legendary

 Offline Offline
Activity: 3416
Merit: 1912
The Concierge of Crypto

|
 |
November 14, 2019, 08:03:42 PM |
|
I was about to suggest something similar, but refrained from doing so; it would still cost me shipping and handling. Keep in mind the "practical" definition of impossible as we've discussed in this thread.
Private data recovery companies don't have a better chance than flipping a coin to get the next bit correct.
FBI could not decrypt encrypted TrueCrypt hard drives before. I don't think they have anything better today to recover single pass wiped magnetic drives, especially if they were previously encrypted.
|
|
|
|
Stedsm
Legendary

 Offline Offline
Activity: 3052
Merit: 1273

|
 |
November 15, 2019, 03:40:38 PM |
|
I really don't follow your comment. I'm sorry if I wasn't able to convince you here. Not reusing addresses is good for privacy, but it doesn't do anything for your security or protect against your keys being compromised. Exactly why not? I'm asking this because if even 10s of 1000s of ASICs won't be able to generate even a single address' private key that is already over the network, then considering that we don't reuse an address we have used before in a wallet and choose a different address to receive/send coins, won't it be a different private key that is attached to that new address? Even if the older one gets compromised, how will the new address be hacked and the coins be removed from the same unless the wallet itself gets compromised? What if I use different wallets to use each new address from a different wallet itself at a time? Correct me if I'm wrong, but we don't use more than single address not because we want to prove it that it's ours, but because a used address doesn't get charged higher fees compared to a newly generated one?
The only difference in fee between addresses is if you are using legacy, nested SegWit, or native SegWit. There is no difference in fee whether it's the first transaction from a new address or the ten thousandth transaction from a 10 year old address. So you mean to say that if I use a new native SegWit over an old native SegWit which already had so many inputs, I'll be charged the same on both the addresses when I try to send a transaction to an address that I keep same in both? |
| .SHUFFLE.COM.. | ███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████ | ███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████
███████████████████████ | .
...Next Generation Crypto Casino... |
|
|
|
o_e_l_e_o
In memoriam
Legendary

 Offline Offline
Activity: 2268
Merit: 18512

|
 |
November 15, 2019, 05:25:41 PM |
|
Exactly why not? I'm asking this because if even 10s of 1000s of ASICs won't be able to generate even a single address' private key that is already over the network Having a public address "all over the network" does not make it any easier to generate the associated private key. then considering that we don't reuse an address we have used before in a wallet and choose a different address to receive/send coins, won't it be a different private key that is attached to that new address? Correct. Each new address you generate has its own private key. Even if the older one gets compromised, how will the new address be hacked and the coins be removed from the same unless the wallet itself gets compromised? It won't. If one private key is compromised, only the single address it corresponds to will also be compromised. My point is that generating a new address every time doesn't increase security as an attacker who is brute forcing private keys is equally as likely to brute force the key to a brand new address as an old address which has been used many times. Note that the chance of this happening is so close to 0 as to be considered impossible. Not reusing addresses is good for privacy, but it makes little difference to security.* So you mean to say that if I use a new native SegWit over an old native SegWit which already had so many inputs, I'll be charged the same on both the addresses when I try to send a transaction to an address that I keep same in both?
Yes. Provide you have the same number and type of inputs and outputs in each transaction, there is no difference in fee based on address age or previous transaction history.
*The caveat to this would be if ECDSA is broken in a way that allows an attacker to generate a private key from a public key, in which case address reuse would indeed be a security risk, but this is likely decades away, if ever. |
|
|
|
|
Dabs
Legendary

 Offline Offline
Activity: 3416
Merit: 1912
The Concierge of Crypto

|
 |
November 18, 2019, 04:20:59 PM |
|
Spending coins to brand new unused and unspent addresses kinda protects those coins, because the public key has not been published in a spend transaction. The public key is hashed twice and the only thing we have is the address itself.
The address and the public key are not the same. You can't get the public key just from the address.
Reusing addresses, where said address has spent any coin at least once means the public key of that particular address is already known.
|
|
|
|
|



