ricardosuperx (OP)
Member
 
 Offline Offline
Activity: 109
Merit: 13
A positive attitude changes everything *_*

|
 |
May 02, 2020, 11:37:49 PM
Last edit: September 28, 2020, 07:25:43 PM by ricardosuperx Merited by vapourminer (1), Welsh (1), o_e_l_e_o (1) |
|
HELLO PEOPLE!
I would like a good explanation of how public keys are generated.
EQUATION OR FORMULA
y^2 = x^3 + 7
P = k * G
X = c^2 2px
Y = c (px rx) py
Private key: 1
Public key compressed : X = 0279BE667EF9DCBBAC55A06295CE870B07029BFCDB2DCE28D959F2815B16F81798
So it should be ...
Private key: 2
Public key compressed: X =02F37CCCFDF3B97758AB40C52B9D0E160E0537F9B65B9C51B2B3E502B62DF02F30
Why public key compressed of 2 is: X = 02C6047F9441ED7D6D3045406E95C07CD85C778E4B8CEF3CA7ABAC09B95C709EE5?
|
|
|
|
|
|
|
|
|
According to NIST and ECRYPT II, the cryptographic algorithms used in
Bitcoin are expected to be strong until at least 2030. (After that, it
will not be too difficult to transition to different algorithms.)
|
|
|
Advertised sites are not endorsed by the Bitcoin Forum. They may be unsafe, untrustworthy, or illegal in your jurisdiction.
|
|
|
|
|
|
MrFreeDragon
|
 |
May 03, 2020, 12:29:46 AM |
|
It does not work in this way. Keep in mind main thing: private key is a number (just integer), but public key is a point with x and y coordinates. So you in your example public key was not correct for private key 1. For private key 1 the public key is: 0479be667ef9dcbbac55a06295ce870b07029bfcdb2dce28d959f2815b16f81798483ada7726a3c4655da4fbfc0e1108a8fd17b448a68554199c47d08ffb10d4b8where 04 is a prefix for uncompressed key, green part is X-coordinate and blue part is Y-coordinate. The compressed key contains only X coordinate with the prefix 02/03 (02 for Y even, and 03 for Y odd), because Y could be received from the formula y^2 = x^3 + 7, so no need to keep Y. The compressed key so will be: 0279be667ef9dcbbac55a06295ce870b07029bfcdb2dce28d959f2815b16f81798In your example you wrote only X coordinate for public key, it was not correct. Prefix 02 should also be there in order to know both coordinates. Also, you should know that there is a basis point which was determined for elliptic curve selected for bitcoin. Basis point is usually written as G, and has coordinates: Gx = 0x79be667ef9dcbbac55a06295ce870b07029bfcdb2dce28d959f2815b16f81798 Gy = 0x483ada7726a3c4655da4fbfc0e1108a8fd17b448a68554199c47d08ffb10d4b8 Now the public key for every pk is pk*G, so for 1 public key 1*G - actually the G basis point itself. For pk=2 the public key is 2*G = G + G, so you should perform scalar addition for basis point with itself (you should use point doubling). For pk=3 you just add the publik key for pk=2 with basis point G And so on For more details have a look at parrt 4 of this reading: https://pdfslide.net/documents/introduction-to-bitcoin-and-ecdsa.html |
|
|
|
ricardosuperx (OP)
Member
 
 Offline Offline
Activity: 109
Merit: 13
A positive attitude changes everything *_*

|
 |
May 03, 2020, 12:43:48 AM
Last edit: May 03, 2020, 01:14:44 AM by ricardosuperx |
|
I'm doing this:
Private key 2:
G2 * 79be667ef9dcbbac55a06295ce870b07029bfcdb2dce28d959f2815b16f81798
Public key compressed: X = 02F37CCCFDF3B97758AB40C52B9D0E160E0537F9B65B9C51B2B3E502B62DF02F30
I'm really sad ... I'm trying to learn and the moderator deleted my previous post ... Disappointed! Thanks MrFreeDragon for the explanation
|
|
|
|
|
MrFreeDragon
|
-snip-
Thanks for the answer. I will correct my question.
I just wanted to understand the G + G2 point duplication part ... The public key of 2,
X =0279be667ef9dcbbac55a06295ce870b07029bfcdb2dce28d959f2815b16f81798.
But for me:
X = 02f37cccfdf3b97758ab40c52b9d0e160e0537f9b65b9c51b2b3e502b62df02f30
If you want to doule point P in order to receive R = P + P, you should make the following: c = 3*P.x*Px*invert(2*P.y) % modulo R.x = (c*c - 2*P.x) % modulo R.y = (c*(P.x - R.x) - P.y) % modulo modulo = 0xFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFEFFFFFC2F For your case with P = G = Point (Gx, Gy) where: Gx = 0x79be667ef9dcbbac55a06295ce870b07029bfcdb2dce28d959f2815b16f81798 Gy = 0x483ada7726a3c4655da4fbfc0e1108a8fd17b448a68554199c47d08ffb10d4b8 We have the following: invert(2*P.y) = 0xb7e31a064ed74d314de79011c5f0a46ac155602353dc3d340fbeaeec9767a6a6 c = 0xcb35b28428101a303eb9d1235992ac63f58857c2f631ee6936d3aebbeddcd1b1 R.x = (c*c - 2*Gx) % modulo = 0xc6047f9441ed7d6d3045406e95c07cd85c778e4b8cef3ca7abac09b95c709ee5 R.y = 0x1ae168fea63dc339a3c58419466ceaeef7f632653266d0e1236431a950cfe52a So we have R.x and R.y of the public key 2G = G + G (public key for private key = 2), and it is written in compressed format like: 02c6047f9441ed7d6d3045406e95c07cd85c778e4b8cef3ca7abac09b95c709ee5 |
|
|
|
ricardosuperx (OP)
Member
 
 Offline Offline
Activity: 109
Merit: 13
A positive attitude changes everything *_*

|
 |
May 03, 2020, 01:29:58 AM |
|
I thank you very much!
I'm trying here, I would like to do and understand without scripts or programs. I want to learn manually. I am open to further explanation. Thank MrFreeDragon
|
|
|
|
|
|
ricardosuperx (OP)
Member
 
 Offline Offline
Activity: 109
Merit: 13
A positive attitude changes everything *_*

|
 |
May 03, 2020, 02:53:33 PM
Last edit: May 03, 2020, 03:07:49 PM by ricardosuperx |
|
-snip-
Thanks for the answer. I will correct my question.
I just wanted to understand the G + G2 point duplication part ... The public key of 2,
X =0279be667ef9dcbbac55a06295ce870b07029bfcdb2dce28d959f2815b16f81798.
But for me:
X = 02f37cccfdf3b97758ab40c52b9d0e160e0537f9b65b9c51b2b3e502b62df02f30
If you want to doule point P in order to receive R = P + P, you should make the following: c = 3*P.x*Px*invert(2*P.y) % modulo R.x = (c*c - 2*P.x) % modulo R.y = (c*(P.x - R.x) - P.y) % modulo modulo = 0xFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFEFFFFFC2F For your case with P = G = Point (Gx, Gy) where: Gx = 0x79be667ef9dcbbac55a06295ce870b07029bfcdb2dce28d959f2815b16f81798 Gy = 0x483ada7726a3c4655da4fbfc0e1108a8fd17b448a68554199c47d08ffb10d4b8 We have the following: invert(2*P.y) = 0xb7e31a064ed74d314de79011c5f0a46ac155602353dc3d340fbeaeec9767a6a6 c = 0xcb35b28428101a303eb9d1235992ac63f58857c2f631ee6936d3aebbeddcd1b1 R.x = (c*c - 2*Gx) % modulo = 0xc6047f9441ed7d6d3045406e95c07cd85c778e4b8cef3ca7abac09b95c709ee5 R.y = 0x1ae168fea63dc339a3c58419466ceaeef7f632653266d0e1236431a950cfe52a So we have R.x and R.y of the public key 2G = G + G (public key for private key = 2), and it is written in compressed format like: 02c6047f9441ed7d6d3045406e95c07cd85c778e4b8cef3ca7abac09b95c709ee5 I have a question. If the private key is 3 ... do I need to change the formula this way? R = P+P+Pc = 4*P.x*Px*invert( 3*P.y) % modulo R.x = (c*c - 3*P.x) % modulo |
|
|
|
ricardosuperx (OP)
Member
 
 Offline Offline
Activity: 109
Merit: 13
A positive attitude changes everything *_*

|
 |
May 03, 2020, 02:58:48 PM
Last edit: May 03, 2020, 03:20:02 PM by ricardosuperx |
|
I read. Very interesting! Thanks, but I still have questions |
|
|
|
|
MrFreeDragon
|
-snip-
I have a question.
If the private key is 3 ... do I need to change the formula this way?
R = P+P+P
c = 4*P.x*Px*invert(3*P.y) % modulo
R.x = (c*c - 3*P.x) % modulo
No, formula is ALWAYS the same. That was a formula for double the point: c = 3*P.x*Px*invert(2*P.y) % modulo R.x = (c*c - 2*P.x) % modulo R.y = (c*(P.x - R.x) - P.y) % modulo If you want to add 2 points P and Q (2 different non-zero Points) there is another formula for R = P + Q: dx = (Q.x - P.x) % modulo dy = (Q.y - P.y) % modulo c = dy * invert(dx) % modulo R.x = (c*c - P.x - Q.x) % modulo R.y = (c*(P.x - R.x) - P.y) % modulo For addition it does not matter if you make P + Q or Q + P, teh result will be the same. Also, keep in mind that in elliptic curve scalar addition there are only scalar addition and scalar doubling are determined. No, direct multiplication, or no direct substraction, etc. For multiplication, the factor is splited in order to make only doublings and additions. So, for private key = 3 you have: 3=2+1, and the public key will be 3G = 2G + 1G = doubled G + G, so first of all you should double G and receive 2G (1st formula), and then make the addition of 2 points 2G and G (2dn formula) and finally you will have 3G or pubblic key for pk = 3. The same for every number. For example, if you want to find the public key for 13, you should present it in this form: 13 = 8 + 4 + 1 = 2^3 + 2^2 + 1, and now calculate public key for every part (for 2^2 it is doubling G, and then doubling te received result again; for 2^3 it is the dubling G 3 times, anf for 1 it is just G); as soon as you have all 3 public keys you should use addition formula 2 times: add 2^3 and 2^2 and then add the received result with G. Finally you will have the public key for pk = 13 Actully all the scripts do the same work: doubling points and adding them, nothing else. Only doubling and addition. Good luck with manual calcualtions  |
|
|
|
joinfree
Sr. Member
   
 Offline Offline
Activity: 1246
Merit: 260
1A6nybMUHYKS6E6Z3eJFm4KpVDdev8BAJL

|
 |
May 03, 2020, 06:07:21 PM |
|
Wait a minute, so are you guys suggesting that you can actually calculate or deduce the private keys of someone by just looking at the public key? I'm lost maybe a bit of clarification would help. Or I am not getting that the OP is trying to say.
|
Crypto Enthusiast supporting innovative ideas for the Liberalization of the world from the Centralized Institutions.
|
|
|
|
Review Master
|
 |
May 03, 2020, 07:15:33 PM |
|
Wait a minute, so are you guys suggesting that you can actually calculate or deduce the private keys of someone by just looking at the public key? I'm lost maybe a bit of clarification would help. Or I am not getting that the OP is trying to say.
No that's not actually going to happen. Because this is just one integer public key, but in reality there are more integer in your private key. No scripts can deduce the private keys of someone. Even if anyone wants to do this, he/she needs a quantum computer with a minimum of 1000 qubits to expose any private key from any algorithm. In this current time, only IBM has 50 qubits of a quantum computer and Google (cooperating with NASA) has 53 qubits of quantum computer. Thought D-wave have 2000 qubits of quantum computer, but that's used only for optimization not for general purpose. So, it's will take more time to break bitcoin or other crypto-currencies private key. Also by the time passed, there will be a solution for it too.  |
|
|
|
ricardosuperx (OP)
Member
 
 Offline Offline
Activity: 109
Merit: 13
A positive attitude changes everything *_*

|
 |
May 15, 2020, 02:44:51 PM |
|
Wait a minute, so are you guys suggesting that you can actually calculate or deduce the private keys of someone by just looking at the public key? I'm lost maybe a bit of clarification would help. Or I am not getting that the OP is trying to say.
I just want to understand the math behind Bitcoin in a simple way  |
|
|
|
ricardosuperx (OP)
Member
 
 Offline Offline
Activity: 109
Merit: 13
A positive attitude changes everything *_*

|
 |
May 15, 2020, 02:49:07 PM |
|
Wait a minute, so are you guys suggesting that you can actually calculate or deduce the private keys of someone by just looking at the public key? I'm lost maybe a bit of clarification would help. Or I am not getting that the OP is trying to say.
No that's not actually going to happen. Because this is just one integer public key, but in reality there are more integer in your private key. No scripts can deduce the private keys of someone. Even if anyone wants to do this, he/she needs a quantum computer with a minimum of 1000 qubits to expose any private key from any algorithm. In this current time, only IBM has 50 qubits of a quantum computer and Google (cooperating with NASA) has 53 qubits of quantum computer. Thought D-wave have 2000 qubits of quantum computer, but that's used only for optimization not for general purpose. So, it's will take more time to break bitcoin or other crypto-currencies private key. Also by the time passed, there will be a solution for it too.  I agree with you! |
|
|
|
BrewMaster
Legendary

 Offline Offline
Activity: 2114
Merit: 1292
There is trouble abrewing

|
 |
May 15, 2020, 03:30:40 PM Merited by fillippone (2) |
|
I just want to understand the math behind Bitcoin in a simple way  well that math is not very simple to learn it that easily. there is a lot of new concepts involved and the whole algorithm (elliptic curve cryptography) also has certain complexity to it. but i have found that this page here explains things in simpler terms that could get you started on understanding the whole thing, specially while looking at the curve shapes included helps with understanding the characteristics of elliptic curves: https://blog.cloudflare.com/a-relatively-easy-to-understand-primer-on-elliptic-curve-cryptography/ |
There is a FOMO brewing...
|
|
|
|
Review Master
|
 |
May 15, 2020, 05:36:38 PM |
|
I just want to understand the math behind Bitcoin in a simple way  you can check this sources to learn more. I am also a learner and happy to be here. Thanks both of you for sharing this sources. I am also still learning this and happy to get in touch of you guys. Personally, i do bounty to earn something while i am learning this. But my curiosity take me into this forum while i just start leaning python and other programming language.   |
|
|
|
archyone
Newbie

 Offline Offline
Activity: 25
Merit: 1

|
 |
May 27, 2020, 05:39:29 AM |
|
-snip-
Thanks for the answer. I will correct my question.
I just wanted to understand the G + G2 point duplication part ... The public key of 2,
X =0279be667ef9dcbbac55a06295ce870b07029bfcdb2dce28d959f2815b16f81798.
But for me:
X = 02f37cccfdf3b97758ab40c52b9d0e160e0537f9b65b9c51b2b3e502b62df02f30
If you want to doule point P in order to receive R = P + P, you should make the following: c = 3*P.x*Px*invert(2*P.y) % modulo R.x = (c*c - 2*P.x) % modulo R.y = (c*(P.x - R.x) - P.y) % modulo modulo = 0xFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFEFFFFFC2F For your case with P = G = Point (Gx, Gy) where: Gx = 0x79be667ef9dcbbac55a06295ce870b07029bfcdb2dce28d959f2815b16f81798 Gy = 0x483ada7726a3c4655da4fbfc0e1108a8fd17b448a68554199c47d08ffb10d4b8 We have the following: invert(2*P.y) = 0xb7e31a064ed74d314de79011c5f0a46ac155602353dc3d340fbeaeec9767a6a6 c = 0xcb35b28428101a303eb9d1235992ac63f58857c2f631ee6936d3aebbeddcd1b1 R.x = (c*c - 2*Gx) % modulo = 0xc6047f9441ed7d6d3045406e95c07cd85c778e4b8cef3ca7abac09b95c709ee5 R.y = 0x1ae168fea63dc339a3c58419466ceaeef7f632653266d0e1236431a950cfe52a So we have R.x and R.y of the public key 2G = G + G (public key for private key = 2), and it is written in compressed format like: 02c6047f9441ed7d6d3045406e95c07cd85c778e4b8cef3ca7abac09b95c709ee5 Hello, Thanks for your explanation I'm confuse with this part : c = 3*P.x*Px*invert(2*P.y) % modulo How get invert(2*P.y) = 0xb7e31a064ed74d314de79011c5f0a46ac155602353dc3d340fbeaeec9767a6a6 ?? Can someone provide an explanation or simply a python formula, is it the inverse modular ? Thanks in advance |
|
|
|
|
BrewMaster
Legendary

 Offline Offline
Activity: 2114
Merit: 1292
There is trouble abrewing

|
 |
May 27, 2020, 05:51:03 PM |
|
How get invert(2*P.y) =
the full name is Modular Multiplicative Inverse and to compute ModInverse(2*P.y) you have to find a value that when multiplied by your value and divided by the prime gives 1. you can read more about it on wikipedia: https://en.wikipedia.org/wiki/Modular_multiplicative_inverselook at the examples below that. the computation uses the extended Euclidean algorithm. here is a python example: https://stackoverflow.com/a/9758173/10401748 |
There is a FOMO brewing...
|
|
|
|
MrFreeDragon
|
-snip-
I'm confuse with this part : c = 3*P.x*Px*invert(2*P.y) % modulo
How get invert(2*P.y) = 0xb7e31a064ed74d314de79011c5f0a46ac155602353dc3d340fbeaeec9767a6a6 ??
-snip-
As was explained above, the inverse for k by modulo is such value mwhere (m*k) by modulo is equal to 1. The best way for python is to use library gmpy2 and its function gmpy2.invert(k,p) which returns the inverse value to k by modulo = p. This function is the best for python and approx. 50 times faster than any other self made calculations. For ubuntu for example you can easily install it: sudo apt update
sudo apt install python3-gmpy2 If it is not in repository, you can download gmpy2 from here (pls, check the correct python version): https://www.lfd.uci.edu/~gohlke/pythonlibs/#gmpyand install it in this way (example for python ver 3.7): python -m pip install gmpy2-2.0.8-cp37-cp37m-win_amd64.whl If you do not want to use the gmpy2 libriary (however it is the best way), you can also use this self made inversion function: def egcd (a, b):
if a == 0:
return (b, 0, 1)
else:
g, x, y = egcd(b % a, a)
return (g, y - (b // a) * x, x)
def inversion (m, n):
while m < 0:
m += n
g, x, _ = egcd (m, n)
if g == 1:
return x % n
else: print (' no inverse exist')
The function inversion requires 2 parameters: m and n, where n is the modulo and m is the number for which you would like to calculate the inverse. |
|
|
|
archyone
Newbie

 Offline Offline
Activity: 25
Merit: 1

|
Thanks to MrFreedragon and BrewMaster for the explanations. However I still have a question on the generation of public key with a private key other than 1 or 2 or 13 like the examples.
MrFreedragon say :
"The same for every number. For example, if you want to find the public key for 13, you should present it in this form: 13 = 8 + 4 + 1 = 2^3 + 2^2 + 1, and now calculate public key for every part (for 2^2 it is doubling G, and then doubling te received result again; for 2^3 it is the dubling G 3 times, anf for 1 it is just G); as soon as you have all 3 public keys you should use addition formula 2 times: add 2^3 and 2^2 and then add the received result with G. Finally you will have the public key for pk = 13"
My question is : why 13 = 8 + 4 +1 ? is 4 + 4 + 4 + 1 give the same result or must there be a certain rule ?
Not sure and i can't retreive the post but it seem i read something with the private key in it's binary form ?
Sorry for my noob question ^^ but bitcoin is really more complicated than I thought at the start ^^
|
|
|
|
|
BrewMaster
Legendary

 Offline Offline
Activity: 2114
Merit: 1292
There is trouble abrewing

|
 |
June 05, 2020, 05:24:51 PM |
|
My question is : why 13 = 8 + 4 +1 ? is 4 + 4 + 4 + 1 give the same result or must there be a certain rule ?
they are the same. Not sure and i can't retreive the post but it seem i read something with the private key in it's binary form ?
that's the idea. one of the methods to compute public key (which is multiplying the key numeric value by generator point) is that key (shown as d) is going to be split into smaller powers of 2 parts (d0 + 2d1+...) then for each 1 an addition then a doubling occurs and for each 0 only point double is performed. https://en.wikipedia.org/wiki/Elliptic_curve_point_multiplication |
There is a FOMO brewing...
|
|
|
|
MrFreeDragon
|
 |
June 05, 2020, 09:24:19 PM |
|
-snip-
My question is : why 13 = 8 + 4 +1 ? is 4 + 4 + 4 + 1 give the same result or must there be a certain rule ?
Not sure and i can't retreive the post but it seem i read something with the private key in it's binary form ?
-snip-
Your example with 13 will give the same result. You can also calculate 13 as 1 + 1 + 1 + 1 + ... + 1 + 1 (13 times), but here you should perform 12 additions. As for the private key in binary form - I made a tool to play with binary numbers: https://bitcointalk.org/index.php?topic=5187401That tool is very nice for learning purposes. And also good to create real wallets if you use physical coin for your random entropy source. Every binary number could be represented as c255*2^255 + c254*2^254 + c253*2^253 + ... + c3*2^3 + c2^2 + c1*2 + c0, where coefficients c0, c1, c2, ... c254, c255 represent bit values (1 or 0). It is actually your binary number. So in order to calculate public keys for various large binary numbers you can easily make the pre-calculations of 256 public keys for numbers 1, 2, 2^2, 2^3, 2^4, 2^5, ... 2^254, 2^255 and later just make up to 255 additions between pre-calculated public keys. |
|
|
|
archyone
Newbie

 Offline Offline
Activity: 25
Merit: 1

|
 |
August 27, 2020, 07:24:44 PM |
|
Hello everyone, good! thanks to the help of MrFreeDragon and BrewMaster I now have a good basis for adding 2 points on an elliptical curve.
As a reminder :
If you want to double point P in order to receive R = P + P, you should make the following:
c = 3 * P.x * Px * invert (2 * P.y)% modulo
R.x = (c * c - 2 * P.x)% modulo
R.y = (c * (P.x - R.x) - P.y)% modulo
modulo = 0xFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFEFFFFFC2F
and
If you want to add 2 points P and Q (2 different non-zero Points) there is another formula for R = P + Q:
dx = (Q.x - P.x)% modulo
dy = (Q.y - P.y)% modulo
c = dy * invert (dx)% modulo
R.x = (c * c - P.x - Q.x)% modulo
R.y = (c * (P.x - R.x) - P.y)% modulo
I have now no problem with this but as you can imagine, I still have 1 problem ^^, certainly due to my approximate understanding of English I am unable to find a formula for point to point substraction. Is this also possible?
Thanks in advance (again^^)
|
|
|
|
|
BrewMaster
Legendary

 Offline Offline
Activity: 2114
Merit: 1292
There is trouble abrewing

|
I have now no problem with this but as you can imagine, I still have 1 problem ^^, certainly due to my approximate understanding of English I am unable to find a formula for point to point substraction. Is this also possible?
there is no special formula for point subtraction as far as i know. instead the P-Q is simply defined as P+(-Q) (same as addition) and -Q or negative of a point is defined as negating its y coordinate. or in other words -Q(x,y) = Q(x,-y) and since we don't use negative numbers in modular arithmetic -y becomes P-y where P is curve's prime. |
There is a FOMO brewing...
|
|
|
archyone
Newbie

 Offline Offline
Activity: 25
Merit: 1

|
 |
August 28, 2020, 11:26:11 AM |
|
there is no special formula for point subtraction as far as i know. instead the P-Q is simply defined as P+(-Q) (same as addition) and -Q or negative of a point is defined as negating its y coordinate. or in other words -Q(x,y) = Q(x,-y) and since we don't use negative numbers in modular arithmetic -y becomes P-y where P is curve's prime.
oOO !! wonderfully explained, first test -> total success .. I understood the first time when research for several weeks had not led to much. Many thanks to you BrewMaster (again ^^)It is this notation (-y becomes P-y where P is curve's prime) that I have not seen anywhere that I am lacking. |
|
|
|
|
bytcoin
Member
 
 Offline Offline
Activity: 211
Merit: 20
$$$$$$$$$$$$$$$$$$$$$$$$$

|
 |
August 29, 2020, 07:38:17 PM
Last edit: August 29, 2020, 08:45:01 PM by bytcoin |
|
-snip-
I have a question.
If the private key is 3 ... do I need to change the formula this way?
R = P+P+P
c = 4*P.x*Px*invert(3*P.y) % modulo
R.x = (c*c - 3*P.x) % modulo
No, formula is ALWAYS the same. That was a formula for double the point: c = 3*P.x*Px*invert(2*P.y) % modulo R.x = (c*c - 2*P.x) % modulo R.y = (c*(P.x - R.x) - P.y) % modulo If you want to add 2 points P and Q (2 different non-zero Points) there is another formula for R = P + Q: dx = (Q.x - P.x) % modulo dy = (Q.y - P.y) % modulo c = dy * invert(dx) % modulo R.x = (c*c - P.x - Q.x) % modulo R.y = (c*(P.x - R.x) - P.y) % modulo If the formula is always the same, All public keys will also always be the same! "Where am I wrong? (dx, dy, c, R.x, R.y, Q.x Q.y, P.x, P.y)Can someone explain to me what are this? I think Rx and Ry are the coordinates of the public key, right? |
|
|
|
|
BrewMaster
Legendary

 Offline Offline
Activity: 2114
Merit: 1292
There is trouble abrewing

|
If the formula is always the same, All public keys will also always be the same! "Where am I wrong?
they aren't the same because this formula is called different number of times depending on the private key. in simple terms imagine if the formula was this: x+1 and you always called it with the same x (like you do with the generator point). if you use it with x=5 and call it 3 times (private key equal to 3) you get 8 and if you call it 6 times (private key equal to 6) you get 11 and so on. |
There is a FOMO brewing...
|
|
|
archyone
Newbie

 Offline Offline
Activity: 25
Merit: 1

|
 |
September 05, 2020, 10:33:20 AM
Last edit: September 05, 2020, 11:24:06 AM by archyone |
|
If the formula is always the same, All public keys will also always be the same! "Where am I wrong?
(dx, dy, c, R.x, R.y, Q.x Q.y, P.x, P.y)Can someone explain to me what are this?
I think Rx and Ry are the coordinates of the public key, right?
[/quote]
ok, I will try to explain as simply as possible because it is true that I myself struggled to understand the system.
So it is a question here of adding 2 points (not the same). In this example we use :
first point: (all values are in décimal for a better comprehension)
X coordinate: 21262057306151627953595685090280431278183829487175876377991189246716355947009 (it is Qx)
Y coordinate: 41749993296225487051377864631615517161996906063147759678534462689479575333124 (it is Qy)
The Private key for this point is 0000000000000000000000000000000000000000000000000000000000000008
second point to add:
X coordinate: 89565891926547004231252920425935692360644145829622209833684329913297188986597 (it is Px)
Y coordinate: 12158399299693830322967808612713398636155367887041628176798871954788371653930 (it is Py)
The Private key for this point is 0000000000000000000000000000000000000000000000000000000000000002
So to add the 1st point to the second we use the formula : (here modulo is 115792089237316195423570985008687907853269984665640564039457584007908834671663 )
dx = (Q.x - P.x) % modulo
dy = (Q.y - P.y) % modulo
c = dy * invert(dx) % modulo
R.x = (c*c - P.x - Q.x) % modulo
R.y = (c*(P.x - R.x) - P.y) % modulo
in our example we have
dx = (21262057306151627953595685090280431278183829487175876377991189246716355947009 - 89565891926547004231252920425935692360644145829622209833684329913297188986597) % modulo
dx = 47488254616920819145913749673032646770809668323194230583764443341328001632075
dy = (41749993296225487051377864631615517161996906063147759678534462689479575333124 - 12158399299693830322967808612713398636155367887041628176798871954788371653930) % modulo
dy = 29591593996531656728410056018902118525841538176106131501735590734691203679194
invert of dx = 70279122268919195963430815486314537773961171454828771794853116552210630553734
c = dy * invert(dx) % modulo
c = 16132032934385503768504319366562120314980927452732756733183380715276156205226
So the new point (8 + 2)
R.x = (c*c - P.x - Q.x) % modulo
R.x --> X coordinate of (8+2) = 72488970228380509287422715226575535698893157273063074627791787432852706183111
R.y = (c*(P.x - R.x) - P.y) % modulo
R.y --> Y coordinate of (8+2) = 62070622898698443831883535403436258712770888294397026493185421712108624767191
If we check these coordinates, we find that it corresponds to the private key: 000000000000000000000000000000000000000000000000000000000000000a (10)
There you go, I hope I was as clear as possible and apologies for my broken English ^^
|
|
|
|
|
ricardosuperx (OP)
Member
 
 Offline Offline
Activity: 109
Merit: 13
A positive attitude changes everything *_*

|
 |
September 13, 2020, 05:22:01 PM
Last edit: September 14, 2020, 12:22:53 PM by ricardosuperx |
|
I learned to double the point, but I cannot calculate the public keys of the private keys in sequence
Duplication of points;
Compressed public key;
In decimal;
Equation:
c = (3px^2 + a) / 2py
rx = c^2 2px
Prime Modulo: 115792089237316195423570985008687907853269984665640564039457584007908834671663
Base Point: (55066263022277343669578718895168534326250603453777594175500187360389116729240, 32670510020758816978083085130507043184471273380659243275938904335757337482424)
Order: 115792089237316195423570985008687907852837564279074904382605163141518161494337
Private key: 0000000000000000000000000000000000000000000000000000000000000002
c= 3px^2 + a) / 2py
c=(3*55066263022277343669578718895168534326250603453777594175500187360389116729240^2)/2*32670510020758816978083085130507043184471273380659243275938904335757337482424
c=(3*60300556597753154781239923047219078515410877540607532238537983597388018023497)/2*32670510020758816978083085130507043184471273380659243275938904335757337482424
c=65109580555943268920148784132969327692962647956182032676156366784255219398828/2*32670510020758816978083085130507043184471273380659243275938904335757337482424
c=65109580555943268920148784132969327692962647956182032676156366784255219398828/65341020041517633956166170261014086368942546761318486551877808671514674964848
c=91914383230618135761690975197207778399550061809281766160147273830617914855857
rx=(91914383230618135761690975197207778399550061809281766160147273830617914855857^2)-2*55066263022277343669578718895168534326250603453777594175500187360389116729240
rx=83906328733785496146839373207584853159875368071536834145227120626166587773414-2*55066263022277343669578718895168534326250603453777594175500187360389116729240
rx=83906328733785496146839373207584853159875368071536834145227120626166587773414-110132526044554687339157437790337068652501206907555188351000374720778233458480
rx=89565891926547004231252920425935692360644145829622209833684329913297188986597
rx Compressed in hex = 02c6047f9441ed7d6d3045406e95c07cd85c778e4b8cef3ca7abac09b95c709ee5
Now i would like to understand how to do for private key 3
Can someone do a tutorial like I did IN DECIMAL OF PRIVATE KEY 3
|
|
|
|
ricardosuperx (OP)
Member
 
 Offline Offline
Activity: 109
Merit: 13
A positive attitude changes everything *_*

|
 |
September 13, 2020, 05:59:16 PM
Last edit: September 13, 2020, 06:44:46 PM by ricardosuperx |
|
If the formula is always the same, All public keys will also always be the same! "Where am I wrong?
(dx, dy, c, R.x, R.y, Q.x Q.y, P.x, P.y)Can someone explain to me what are this?
I think Rx and Ry are the coordinates of the public key, right?
ok, I will try to explain as simply as possible because it is true that I myself struggled to understand the system. So it is a question here of adding 2 points (not the same). In this example we use : first point: (all values are in décimal for a better comprehension) X coordinate: 21262057306151627953595685090280431278183829487175876377991189246716355947009 (it is Qx) Y coordinate: 41749993296225487051377864631615517161996906063147759678534462689479575333124 (it is Qy) The Private key for this point is 0000000000000000000000000000000000000000000000000000000000000008 second point to add: X coordinate: 89565891926547004231252920425935692360644145829622209833684329913297188986597 (it is Px) Y coordinate: 12158399299693830322967808612713398636155367887041628176798871954788371653930 (it is Py) The Private key for this point is 0000000000000000000000000000000000000000000000000000000000000002 So to add the 1st point to the second we use the formula : (here modulo is 115792089237316195423570985008687907853269984665640564039457584007908834671663 ) dx = (Q.x - P.x) % modulo dy = (Q.y - P.y) % modulo c = dy * invert(dx) % modulo R.x = (c*c - P.x - Q.x) % modulo R.y = (c*(P.x - R.x) - P.y) % modulo in our example we have dx = (21262057306151627953595685090280431278183829487175876377991189246716355947009 - 89565891926547004231252920425935692360644145829622209833684329913297188986597) % modulo dx = 47488254616920819145913749673032646770809668323194230583764443341328001632075 dy = (41749993296225487051377864631615517161996906063147759678534462689479575333124 - 12158399299693830322967808612713398636155367887041628176798871954788371653930) % modulo dy = 29591593996531656728410056018902118525841538176106131501735590734691203679194 invert of dx = 70279122268919195963430815486314537773961171454828771794853116552210630553734 c = dy * invert(dx) % modulo c = 16132032934385503768504319366562120314980927452732756733183380715276156205226 So the new point (8 + 2) R.x = (c*c - P.x - Q.x) % modulo R.x --> X coordinate of (8+2) = 72488970228380509287422715226575535698893157273063074627791787432852706183111 R.y = (c*(P.x - R.x) - P.y) % modulo R.y --> Y coordinate of (8+2) = 62070622898698443831883535403436258712770888294397026493185421712108624767191 If we check these coordinates, we find that it corresponds to the private key: 000000000000000000000000000000000000000000000000000000000000000a (10) There you go, I hope I was as clear as possible and apologies for my broken English ^^ [/quote] That's what I wanted! Could you make private key 3? |
|
|
|
archyone
Newbie

 Offline Offline
Activity: 25
Merit: 1

|
 |
September 13, 2020, 09:21:23 PM |
|
That's what I wanted! Could you make private key 3?
We must not forget that there are two formulas The one you used to find the point corresponding to the private key: 2 (or rather 0000000000000000000000000000000000000000000000000000000000000002 to be more precise) it is Duplication of points. You did it in your example with the base point--> 1 + 1 =2 ( but that could be another point) To go now with 3 we need to do --> 2 + 1 = 3 (we have now 2 différents points and we can't doubling them) For that you need to use the second formula: modulo = 115792089237316195423570985008687907853269984665640564039457584007908834671663 Px = 89565891926547004231252920425935692360644145829622209833684329913297188986597 (x coordinate point 2) Py = 12158399299693830322967808612713398636155367887041628176798871954788371653930 (y coordinate point 2) Qx = 55066263022277343669578718895168534326250603453777594175500187360389116729240 (x coordinate point 1) not because it is the base point, just because it is the point n°1Qy = 32670510020758816978083085130507043184471273380659243275938904335757337482424 (y coordinate point 1) dx = (Qx - Px) % modulo --> 34499628904269660561674201530767158034393542375844615658184142552908072257357 dy = (Qy - Py) % modulo --> 95279978516251208768455708490894263304954079172022948940317551626939868843169 c = dy * invert(dx) % modulo --> 23578750110654438173404407907450265080473019639451825850605815020978465167024 Rx = (c*c - Px - Qx) % modulo --> 112711660439710606056748659173929673102114977341539408544630613555209775888121 ( x coordinate of point (2+1 =3)Ry = (c*(Px - Rx) - Py) % modulo --> 25583027980570883691656905877401976406448868254816295069919888960541586679410 ( y coordinate of point (2+1 =3)Can't explain better |
|
|
|
|
BASE16
Member
 
 Offline Offline
Activity: 180
Merit: 38

|
 |
September 13, 2020, 11:14:07 PM
Last edit: September 20, 2020, 08:05:15 AM by BASE16 Merited by vapourminer (1) |
|
You are mixing BASE16 with BASE10 there  Your private key = 0x0000000000000000000000000000000000000000000000000000000000000002 It's called BITcoin not BYTEcoin !! or even INTcoin hahaha  Since this is a tutorial you can not really leave out the part of the binary private key so here goes.  You start with a 256 Bits BASE2 Binary Private Key. (Aka. the BIT coin flips) A bit is either 1 or 0 no in between.
1011010000000101011011011111011001101001000111111000110111000111001011100101011000110000001011011101101011010011010001011101011001011111111010101101001111101010110110010010100110010110000010011010100000100110111000100011010001001110101101100011101010100100
Then you can use the following table which is about point doubling:
256 '1' - represents 1*G or 1 * the generator point
255 '2' - represents 1*G + 1*G or 2 * the generator point
254 '4' - represents 2*G + 2*G or 4 * the generator point
253 '8' - represents 4*G + 4*G or 8 * the generator point and the point doubling goes on 256 times...
252 '16'
251 '32'
250 '64'
249 '128'
248 '256'
247 '512'
246 '1024'
245 '2048'
244 '4096'
243 '8192'
242 '16384'
241 '32768'
240 '65536'
239 '131072'
238 '262144'
237 '524288'
236 '1048576'
235 '2097152'
234 '4194304'
233 '8388608'
232 '16777216'
231 '33554432'
230 '67108864'
229 '134217728'
228 '268435456'
227 '536870912'
226 '1073741824'
225 '2147483648'
224 '4294967296'
223 '8589934592'
222 '17179869184'
221 '34359738368'
220 '68719476736'
219 '137438953472'
218 '274877906944'
217 '549755813888'
216 '1099511627776'
215 '2199023255552'
214 '4398046511104'
213 '8796093022208'
212 '17592186044416'
211 '35184372088832'
210 '70368744177664'
209 '140737488355328'
208 '281474976710656'
207 '562949953421312'
206 '1125899906842624'
205 '2251799813685248'
204 '4503599627370496'
203 '9007199254740992'
202 '18014398509481984'
201 '36028797018963968'
200 '72057594037927936'
199 '144115188075855872'
198 '288230376151711744'
197 '576460752303423488'
196 '1152921504606846976'
195 '2305843009213693952'
194 '4611686018427387904'
193 '9223372036854775808'
192 '18446744073709551616'
191 '36893488147419103232'
190 '73786976294838206464'
189 '147573952589676412928'
188 '295147905179352825856'
187 '590295810358705651712'
186 '1180591620717411303424'
185 '2361183241434822606848'
184 '4722366482869645213696'
183 '9444732965739290427392'
182 '18889465931478580854784'
181 '37778931862957161709568'
180 '75557863725914323419136'
179 '151115727451828646838272'
178 '302231454903657293676544'
177 '604462909807314587353088'
176 '1208925819614629174706176'
175 '2417851639229258349412352'
174 '4835703278458516698824704'
173 '9671406556917033397649408'
172 '19342813113834066795298816'
171 '38685626227668133590597632'
170 '77371252455336267181195264'
169 '154742504910672534362390528'
168 '309485009821345068724781056'
167 '618970019642690137449562112'
166 '1237940039285380274899124224'
165 '2475880078570760549798248448'
164 '4951760157141521099596496896'
163 '9903520314283042199192993792'
162 '19807040628566084398385987584'
161 '39614081257132168796771975168'
160 '79228162514264337593543950336'
159 '158456325028528675187087900672'
158 '316912650057057350374175801344'
157 '633825300114114700748351602688'
156 '1267650600228229401496703205376'
155 '2535301200456458802993406410752'
154 '5070602400912917605986812821504'
153 '10141204801825835211973625643008'
152 '20282409603651670423947251286016'
151 '40564819207303340847894502572032'
150 '81129638414606681695789005144064'
149 '162259276829213363391578010288128'
148 '324518553658426726783156020576256'
147 '649037107316853453566312041152512'
146 '1298074214633706907132624082305024'
145 '2596148429267413814265248164610048'
144 '5192296858534827628530496329220096'
143 '10384593717069655257060992658440192'
142 '20769187434139310514121985316880384'
141 '41538374868278621028243970633760768'
140 '83076749736557242056487941267521536'
139 '166153499473114484112975882535043072'
138 '332306998946228968225951765070086144'
137 '664613997892457936451903530140172288'
136 '1329227995784915872903807060280344576'
135 '2658455991569831745807614120560689152'
134 '5316911983139663491615228241121378304'
133 '10633823966279326983230456482242756608'
132 '21267647932558653966460912964485513216'
131 '42535295865117307932921825928971026432'
130 '85070591730234615865843651857942052864'
129 '170141183460469231731687303715884105728'
128 '340282366920938463463374607431768211456'
127 '680564733841876926926749214863536422912'
126 '1361129467683753853853498429727072845824'
125 '2722258935367507707706996859454145691648'
124 '5444517870735015415413993718908291383296'
123 '10889035741470030830827987437816582766592'
122 '21778071482940061661655974875633165533184'
121 '43556142965880123323311949751266331066368'
120 '87112285931760246646623899502532662132736'
119 '174224571863520493293247799005065324265472'
118 '348449143727040986586495598010130648530944'
117 '696898287454081973172991196020261297061888'
116 '1393796574908163946345982392040522594123776'
115 '2787593149816327892691964784081045188247552'
114 '5575186299632655785383929568162090376495104'
113 '11150372599265311570767859136324180752990208'
112 '22300745198530623141535718272648361505980416'
111 '44601490397061246283071436545296723011960832'
110 '89202980794122492566142873090593446023921664'
109 '178405961588244985132285746181186892047843328'
108 '356811923176489970264571492362373784095686656'
107 '713623846352979940529142984724747568191373312'
106 '1427247692705959881058285969449495136382746624'
105 '2854495385411919762116571938898990272765493248'
104 '5708990770823839524233143877797980545530986496'
103 '11417981541647679048466287755595961091061972992'
102 '22835963083295358096932575511191922182123945984'
101 '45671926166590716193865151022383844364247891968'
100 '91343852333181432387730302044767688728495783936'
99 '182687704666362864775460604089535377456991567872'
98 '365375409332725729550921208179070754913983135744'
97 '730750818665451459101842416358141509827966271488'
96 '1461501637330902918203684832716283019655932542976'
95 '2923003274661805836407369665432566039311865085952'
94 '5846006549323611672814739330865132078623730171904'
93 '11692013098647223345629478661730264157247460343808'
92 '23384026197294446691258957323460528314494920687616'
91 '46768052394588893382517914646921056628989841375232'
90 '93536104789177786765035829293842113257979682750464'
89 '187072209578355573530071658587684226515959365500928'
88 '374144419156711147060143317175368453031918731001856'
87 '748288838313422294120286634350736906063837462003712'
86 '1496577676626844588240573268701473812127674924007424'
85 '2993155353253689176481146537402947624255349848014848'
84 '5986310706507378352962293074805895248510699696029696'
83 '11972621413014756705924586149611790497021399392059392'
82 '23945242826029513411849172299223580994042798784118784'
81 '47890485652059026823698344598447161988085597568237568'
80 '95780971304118053647396689196894323976171195136475136'
79 '191561942608236107294793378393788647952342390272950272'
78 '383123885216472214589586756787577295904684780545900544'
77 '766247770432944429179173513575154591809369561091801088'
76 '1532495540865888858358347027150309183618739122183602176'
75 '3064991081731777716716694054300618367237478244367204352'
74 '6129982163463555433433388108601236734474956488734408704'
73 '12259964326927110866866776217202473468949912977468817408'
72 '24519928653854221733733552434404946937899825954937634816'
71 '49039857307708443467467104868809893875799651909875269632'
70 '98079714615416886934934209737619787751599303819750539264'
69 '196159429230833773869868419475239575503198607639501078528'
68 '392318858461667547739736838950479151006397215279002157056'
67 '784637716923335095479473677900958302012794430558004314112'
66 '1569275433846670190958947355801916604025588861116008628224'
65 '3138550867693340381917894711603833208051177722232017256448'
64 '6277101735386680763835789423207666416102355444464034512896'
63 '12554203470773361527671578846415332832204710888928069025792'
62 '25108406941546723055343157692830665664409421777856138051584'
61 '50216813883093446110686315385661331328818843555712276103168'
60 '100433627766186892221372630771322662657637687111424552206336'
59 '200867255532373784442745261542645325315275374222849104412672'
58 '401734511064747568885490523085290650630550748445698208825344'
57 '803469022129495137770981046170581301261101496891396417650688'
56 '1606938044258990275541962092341162602522202993782792835301376'
55 '3213876088517980551083924184682325205044405987565585670602752'
54 '6427752177035961102167848369364650410088811975131171341205504'
53 '12855504354071922204335696738729300820177623950262342682411008'
52 '25711008708143844408671393477458601640355247900524685364822016'
51 '51422017416287688817342786954917203280710495801049370729644032'
50 '102844034832575377634685573909834406561420991602098741459288064'
49 '205688069665150755269371147819668813122841983204197482918576128'
48 '411376139330301510538742295639337626245683966408394965837152256'
47 '822752278660603021077484591278675252491367932816789931674304512'
46 '1645504557321206042154969182557350504982735865633579863348609024'
45 '3291009114642412084309938365114701009965471731267159726697218048'
44 '6582018229284824168619876730229402019930943462534319453394436096'
43 '13164036458569648337239753460458804039861886925068638906788872192'
42 '26328072917139296674479506920917608079723773850137277813577744384'
41 '52656145834278593348959013841835216159447547700274555627155488768'
40 '105312291668557186697918027683670432318895095400549111254310977536'
39 '210624583337114373395836055367340864637790190801098222508621955072'
38 '421249166674228746791672110734681729275580381602196445017243910144'
37 '842498333348457493583344221469363458551160763204392890034487820288'
36 '1684996666696914987166688442938726917102321526408785780068975640576'
35 '3369993333393829974333376885877453834204643052817571560137951281152'
34 '6739986666787659948666753771754907668409286105635143120275902562304'
33 '13479973333575319897333507543509815336818572211270286240551805124608'
32 '26959946667150639794667015087019630673637144422540572481103610249216'
31 '53919893334301279589334030174039261347274288845081144962207220498432'
30 '107839786668602559178668060348078522694548577690162289924414440996864'
29 '215679573337205118357336120696157045389097155380324579848828881993728'
28 '431359146674410236714672241392314090778194310760649159697657763987456'
27 '862718293348820473429344482784628181556388621521298319395315527974912'
26 '1725436586697640946858688965569256363112777243042596638790631055949824'
25 '3450873173395281893717377931138512726225554486085193277581262111899648'
24 '6901746346790563787434755862277025452451108972170386555162524223799296'
23 '13803492693581127574869511724554050904902217944340773110325048447598592'
22 '27606985387162255149739023449108101809804435888681546220650096895197184'
21 '55213970774324510299478046898216203619608871777363092441300193790394368'
20 '110427941548649020598956093796432407239217743554726184882600387580788736'
19 '220855883097298041197912187592864814478435487109452369765200775161577472'
18 '441711766194596082395824375185729628956870974218904739530401550323154944'
17 '883423532389192164791648750371459257913741948437809479060803100646309888'
16 '1766847064778384329583297500742918515827483896875618958121606201292619776'
15 '3533694129556768659166595001485837031654967793751237916243212402585239552'
14 '7067388259113537318333190002971674063309935587502475832486424805170479104'
13 '14134776518227074636666380005943348126619871175004951664972849610340958208'
12 '28269553036454149273332760011886696253239742350009903329945699220681916416'
11 '56539106072908298546665520023773392506479484700019806659891398441363832832'
10 '113078212145816597093331040047546785012958969400039613319782796882727665664'
9 '226156424291633194186662080095093570025917938800079226639565593765455331328'
8 '452312848583266388373324160190187140051835877600158453279131187530910662656'
7 '904625697166532776746648320380374280103671755200316906558262375061821325312'
6 '1809251394333065553493296640760748560207343510400633813116524750123642650624'
5 '3618502788666131106986593281521497120414687020801267626233049500247285301248'
4 '7237005577332262213973186563042994240829374041602535252466099000494570602496'
3 '14474011154664524427946373126085988481658748083205070504932198000989141204992'
2 '28948022309329048855892746252171976963317496166410141009864396001978282409984'
1 '57896044618658097711785492504343953926634992332820282019728792003956564819968'
The first number in the list is the bit number, and the second number is the multiplier, the number of times you will add the generator point to itself later on. It's important to know that we start with bit 256, this is the last bit of the binary private key so you have to read the private key backwards and start with the last bit first. Adding all the numbers is simple: If the bit value is true or a '1' then you will write down the multiplier value and if it is false or a '0' you will write down nothing and move to the next bit. You do this for all the bits and when you are done, you simply add all these multiplier values together, and this will give you the number of times you have to add the generator point to itself to get to the public key point.
1011010000000101011011011111011001101001000111111000110111000111001011100101011000110000001011011101101011010011010001011101011001011111111010101101001111101010110110010010100110010110000010011010100000100110111000100011010001001110101101100011101010100100
Let's calculate the private key in the example above and remember we start with the last bit first:
bit 256 = 0 -
bit 255 = 0 -
bit 254 = 1 - 4
bit 253 = 0 -
bit 252 = 0 -
bit 251 = 1 - 32
bit 250 = 0 -
bit 249 = 1 - 128
bit 248 = 0 -
bit 247 = 1 - 512
bit 246 = 0 -
bit 245 = 1 - 2048
bit 244 = 1 - 4096
bit 243 = 1 - 8192
bit 242 = 0 -
bit 241 = 0 -
bit 240 = 0 -
bit 239 = 1 - 131072
bit 238 = 1 - 262144
bit 237 = 0 -
bit 236 = 1 - 1048576
bit 235 = 1 - 2097152
bit 234 = 0 -
bit 233 = 1 - 8388608
bit 232 = 0 -
bit 231 = 1 - 33554432
bit 230 = 1 - 67108864
bit 229 = 1 - 134217728
bit 228 = 0 -
bit 227 = 0 -
bit 226 = 1 - 1073741824
bit 225 = 0 -
bit 224 = 0 -
bit 223 = 0 -
bit 222 = 1 - 17179869184
bit 221 = 0 -
bit 220 = 1 - 68719476736
bit 219 = 1 - 137438953472
bit 218 = 0 -
bit 217 = 0 -
bit 216 = 0 -
bit 215 = 1 - 2199023255552
bit 214 = 0 -
bit 213 = 0 -
bit 212 = 0 -
bit 211 = 1 - 35184372088832
bit 210 = 1 - 70368744177664
bit 209 = 1 - 140737488355328
bit 208 = 0 -
bit 207 = 1 - 562949953421312
bit 206 = 1 - 1125899906842624
bit 205 = 0 -
bit 204 = 0 -
bit 203 = 1 - 9007199254740992
bit 202 = 0 -
bit 201 = 0 -
bit 200 = 0 -
bit 199 = 0 -
bit 198 = 0 -
bit 197 = 1 - 576460752303423488
bit 196 = 0 -
bit 195 = 1 - 2305843009213693952
bit 194 = 0 -
bit 193 = 1 - 9223372036854775808
bit 192 = 1 - 18446744073709551616
bit 191 = 0 -
bit 190 = 0 -
bit 189 = 1 - 147573952589676412928
bit 188 = 0 -
bit 187 = 0 -
bit 186 = 0 -
bit 185 = 0 -
bit 184 = 0 -
bit 183 = 1 - 9444732965739290427392
bit 182 = 1 - 18889465931478580854784
bit 181 = 0 -
bit 180 = 1 - 75557863725914323419136
bit 179 = 0 -
bit 178 = 0 -
bit 177 = 1 - 604462909807314587353088
bit 176 = 1 - 1208925819614629174706176
bit 175 = 0 -
bit 174 = 0 -
bit 173 = 1 - 9671406556917033397649408
bit 172 = 0 -
bit 171 = 1 - 38685626227668133590597632
bit 170 = 0 -
bit 169 = 0 -
bit 168 = 1 - 309485009821345068724781056
bit 167 = 0 -
bit 166 = 0 -
bit 165 = 1 - 2475880078570760549798248448
bit 164 = 1 - 4951760157141521099596496896
bit 163 = 0 -
bit 162 = 1 - 19807040628566084398385987584
bit 161 = 1 - 39614081257132168796771975168
bit 160 = 0 -
bit 159 = 1 - 158456325028528675187087900672
bit 158 = 0 -
bit 157 = 1 - 633825300114114700748351602688
bit 156 = 0 -
bit 155 = 1 - 2535301200456458802993406410752
bit 154 = 1 - 5070602400912917605986812821504
bit 153 = 1 - 10141204801825835211973625643008
bit 152 = 1 - 20282409603651670423947251286016
bit 151 = 1 - 40564819207303340847894502572032
bit 150 = 0 -
bit 149 = 0 -
bit 148 = 1 - 324518553658426726783156020576256
bit 147 = 0 -
bit 146 = 1 - 1298074214633706907132624082305024
bit 145 = 1 - 2596148429267413814265248164610048
bit 144 = 0 -
bit 143 = 1 - 10384593717069655257060992658440192
bit 142 = 0 -
bit 141 = 1 - 41538374868278621028243970633760768
bit 140 = 0 -
bit 139 = 1 - 166153499473114484112975882535043072
bit 138 = 1 - 332306998946228968225951765070086144
bit 137 = 1 - 664613997892457936451903530140172288
bit 136 = 1 - 1329227995784915872903807060280344576
bit 135 = 1 - 2658455991569831745807614120560689152
bit 134 = 1 - 5316911983139663491615228241121378304
bit 133 = 1 - 10633823966279326983230456482242756608
bit 132 = 1 - 21267647932558653966460912964485513216
bit 131 = 0 -
bit 130 = 1 - 85070591730234615865843651857942052864
bit 129 = 0 -
bit 128 = 0 -
bit 127 = 1 - 680564733841876926926749214863536422912
bit 126 = 1 - 1361129467683753853853498429727072845824
bit 125 = 0 -
bit 124 = 1 - 5444517870735015415413993718908291383296
bit 123 = 0 -
bit 122 = 1 - 21778071482940061661655974875633165533184
bit 121 = 1 - 43556142965880123323311949751266331066368
bit 120 = 1 - 87112285931760246646623899502532662132736
bit 119 = 0 -
bit 118 = 1 - 348449143727040986586495598010130648530944
bit 117 = 0 -
bit 116 = 0 -
bit 115 = 0 -
bit 114 = 1 - 5575186299632655785383929568162090376495104
bit 113 = 0 -
bit 112 = 1 - 22300745198530623141535718272648361505980416
bit 111 = 1 - 44601490397061246283071436545296723011960832
bit 110 = 0 -
bit 109 = 0 -
bit 108 = 1 - 356811923176489970264571492362373784095686656
bit 107 = 0 -
bit 106 = 1 - 1427247692705959881058285969449495136382746624
bit 105 = 1 - 2854495385411919762116571938898990272765493248
bit 104 = 0 -
bit 103 = 1 - 11417981541647679048466287755595961091061972992
bit 102 = 0 -
bit 101 = 1 - 45671926166590716193865151022383844364247891968
bit 100 = 1 - 91343852333181432387730302044767688728495783936
bit 99 = 0 -
bit 98 = 1 - 365375409332725729550921208179070754913983135744
bit 97 = 1 - 730750818665451459101842416358141509827966271488
bit 96 = 1 - 1461501637330902918203684832716283019655932542976
bit 95 = 0 -
bit 94 = 1 - 5846006549323611672814739330865132078623730171904
bit 93 = 1 - 11692013098647223345629478661730264157247460343808
bit 92 = 0 -
bit 91 = 1 - 46768052394588893382517914646921056628989841375232
bit 90 = 0 -
bit 89 = 0 -
bit 88 = 0 -
bit 87 = 0 -
bit 86 = 0 -
bit 85 = 0 -
bit 84 = 1 - 5986310706507378352962293074805895248510699696029696
bit 83 = 1 - 11972621413014756705924586149611790497021399392059392
bit 82 = 0 -
bit 81 = 0 -
bit 80 = 0 -
bit 79 = 1 - 191561942608236107294793378393788647952342390272950272
bit 78 = 1 - 383123885216472214589586756787577295904684780545900544
bit 77 = 0 -
bit 76 = 1 - 1532495540865888858358347027150309183618739122183602176
bit 75 = 0 -
bit 74 = 1 - 6129982163463555433433388108601236734474956488734408704
bit 73 = 0 -
bit 72 = 0 -
bit 71 = 1 - 49039857307708443467467104868809893875799651909875269632
bit 70 = 1 - 98079714615416886934934209737619787751599303819750539264
bit 69 = 1 - 196159429230833773869868419475239575503198607639501078528
bit 68 = 0 -
bit 67 = 1 - 784637716923335095479473677900958302012794430558004314112
bit 66 = 0 -
bit 65 = 0 -
bit 64 = 1 - 6277101735386680763835789423207666416102355444464034512896
bit 63 = 1 - 12554203470773361527671578846415332832204710888928069025792
bit 62 = 1 - 25108406941546723055343157692830665664409421777856138051584
bit 61 = 0 -
bit 60 = 0 -
bit 59 = 0 -
bit 58 = 1 - 401734511064747568885490523085290650630550748445698208825344
bit 57 = 1 - 803469022129495137770981046170581301261101496891396417650688
bit 56 = 1 - 1606938044258990275541962092341162602522202993782792835301376
bit 55 = 0 -
bit 54 = 1 - 6427752177035961102167848369364650410088811975131171341205504
bit 53 = 1 - 12855504354071922204335696738729300820177623950262342682411008
bit 52 = 0 -
bit 51 = 0 -
bit 50 = 0 -
bit 49 = 1 - 205688069665150755269371147819668813122841983204197482918576128
bit 48 = 1 - 411376139330301510538742295639337626245683966408394965837152256
bit 47 = 1 - 822752278660603021077484591278675252491367932816789931674304512
bit 46 = 1 - 1645504557321206042154969182557350504982735865633579863348609024
bit 45 = 1 - 3291009114642412084309938365114701009965471731267159726697218048
bit 44 = 1 - 6582018229284824168619876730229402019930943462534319453394436096
bit 43 = 0 -
bit 42 = 0 -
bit 41 = 0 -
bit 40 = 1 - 105312291668557186697918027683670432318895095400549111254310977536
bit 39 = 0 -
bit 38 = 0 -
bit 37 = 1 - 842498333348457493583344221469363458551160763204392890034487820288
bit 36 = 0 -
bit 35 = 1 - 3369993333393829974333376885877453834204643052817571560137951281152
bit 34 = 1 - 6739986666787659948666753771754907668409286105635143120275902562304
bit 33 = 0 -
bit 32 = 0 -
bit 31 = 1 - 53919893334301279589334030174039261347274288845081144962207220498432
bit 30 = 1 - 107839786668602559178668060348078522694548577690162289924414440996864
bit 29 = 0 -
bit 28 = 1 - 431359146674410236714672241392314090778194310760649159697657763987456
bit 27 = 1 - 862718293348820473429344482784628181556388621521298319395315527974912
bit 26 = 1 - 1725436586697640946858688965569256363112777243042596638790631055949824
bit 25 = 1 - 3450873173395281893717377931138512726225554486085193277581262111899648
bit 24 = 1 - 6901746346790563787434755862277025452451108972170386555162524223799296
bit 23 = 0 -
bit 22 = 1 - 27606985387162255149739023449108101809804435888681546220650096895197184
bit 21 = 1 - 55213970774324510299478046898216203619608871777363092441300193790394368
bit 20 = 0 -
bit 19 = 1 - 220855883097298041197912187592864814478435487109452369765200775161577472
bit 18 = 1 - 441711766194596082395824375185729628956870974218904739530401550323154944
bit 17 = 0 -
bit 16 = 1 - 1766847064778384329583297500742918515827483896875618958121606201292619776
bit 15 = 0 -
bit 14 = 1 - 7067388259113537318333190002971674063309935587502475832486424805170479104
bit 13 = 0 -
bit 12 = 0 -
bit 11 = 0 -
bit 10 = 0 -
bit 9 = 0 -
bit 8 = 0 -
bit 7 = 0 -
bit 6 = 1 - 1809251394333065553493296640760748560207343510400633813116524750123642650624
bit 5 = 0 -
bit 4 = 1 - 7237005577332262213973186563042994240829374041602535252466099000494570602496
bit 3 = 1 - 14474011154664524427946373126085988481658748083205070504932198000989141204992
bit 2 = 0 -
bit 1 = 1 - 57896044618658097711785492504343953926634992332820282019728792003956564819968
We now add up all these numbers, and this gives us a total of privateKeyBase10 = 81425905913881293233417886915456929825803636934140198496261481046664027716260 in BASE10 Or a total of privateKeyBase16 = b4056df6691f8dc72e56302ddad345d65fead3ead9299609a826e2344eb63aa4 in BASE16, which is the hexadecimal private key. 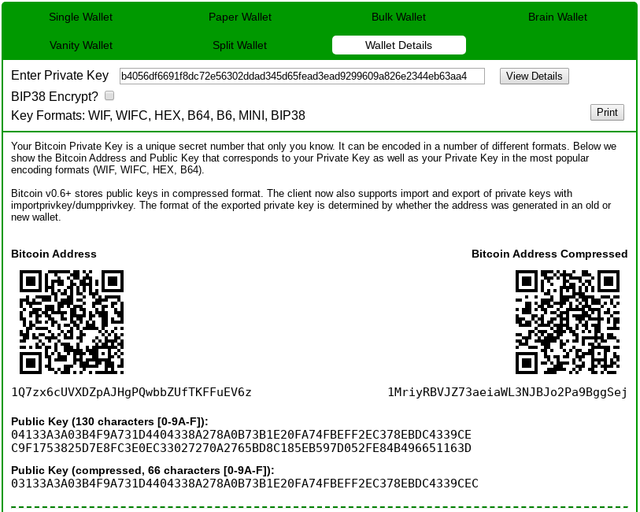 This is the private key number in a format that few people are familiar with but it can also be represented in various WIF Formats depending on the compression parameter: WIF: 5KBZytdkzttdedEB7xLom6YnHRCVTNQPUrJiTDJKS7VJUbiX6Di // uncompressed WIF: L3Fea6uFCY2tm4u9fhGRPdVGsToibPUEDvdBxhHSMqdv8odQMTAZ // compressed As most of us know the full uncompressed public key will start with prefix '04' and have both the X and Y coordinates. The compressed public key only holds the X coordinate, and it can be odd, or even. Public keys of the even type start with a prefix '2' while public keys of the odd type start with a prefix '03' You can discover, or calculate the key type of the compressed public key by looking at the least significant bit of the Y coordinate of the public key. It's important to note that this is not regular multiplication but epileptic curve multiplication. More about the algorithm here: https://paulmillr.com/posts/noble-secp256k1-fast-ecc/ |
|
|
|
|
|
MrFreeDragon
|
 |
September 13, 2020, 11:51:30 PM |
|
-snip-
Now i would like to understand how to do for private key 3
Can someone do a tutorial like I did IN DECIMAL OF PRIVATE KEY 3
Formula for point doubling is: def mul2(Pmul2, p = modulo):
R = Point(0,0)
c = 3*Pmul2.x*Pmul2.x*gmpy2.invert(2*Pmul2.y, p) % p
R.x = (c*c-2*Pmul2.x) % p
R.y = (c*(Pmul2.x - R.x)-Pmul2.y) % p
return RFormula for points addition is (used for different points only): def add(Padd, Q, p = modulo):
R = Point()
dx = (Q.x - Padd.x) % p
dy = (Q.y - Padd.y) % p
c = dy * gmpy2.invert(dx, p) % p
R.x = (c*c - Padd.x - Q.x) % p
R.y = (c*(Padd.x - R.x) - Padd.y) % p
return Rgmpy2.invert here is the inverse calculation. Now you can easily calculate public key for private number 2 - just double the basis point G. In order to calculate the private key for private number 3 you can apply addition for two points - point receive in first stage (doubling of G) and G (because 3 = 1*2 + 1, where 1 is the basis point G): >>> PG.x, PG.y
(55066263022277343669578718895168534326250603453777594175500187360389116729240, 32670510020758816978083085130507043184471273380659243275938904335757337482424)
>>> P2=mul2(PG)
>>> int(P2.x), int(P2.y)
(89565891926547004231252920425935692360644145829622209833684329913297188986597, 12158399299693830322967808612713398636155367887041628176798871954788371653930)
>>> P3=add(P2,PG)
>>> int(P3.x), int(P3.y)
(112711660439710606056748659173929673102114977341539408544630613555209775888121, 25583027980570883691656905877401976406448868254816295069919888960541586679410) |
|
|
|
ricardosuperx (OP)
Member
 
 Offline Offline
Activity: 109
Merit: 13
A positive attitude changes everything *_*

|
 |
September 14, 2020, 12:54:27 PM
Last edit: September 14, 2020, 02:51:58 PM by ricardosuperx |
|
That's what I wanted! Could you make private key 3?
We must not forget that there are two formulas The one you used to find the point corresponding to the private key: 2 (or rather 0000000000000000000000000000000000000000000000000000000000000002 to be more precise) it is Duplication of points. You did it in your example with the base point--> 1 + 1 =2 ( but that could be another point) To go now with 3 we need to do --> 2 + 1 = 3 (we have now 2 différents points and we can't doubling them) For that you need to use the second formula: modulo = 115792089237316195423570985008687907853269984665640564039457584007908834671663 Px = 89565891926547004231252920425935692360644145829622209833684329913297188986597 (x coordinate point 2) Py = 12158399299693830322967808612713398636155367887041628176798871954788371653930 (y coordinate point 2) Qx = 55066263022277343669578718895168534326250603453777594175500187360389116729240 (x coordinate point 1) not because it is the base point, just because it is the point n°1Qy = 32670510020758816978083085130507043184471273380659243275938904335757337482424 (y coordinate point 1) dx = (Qx - Px) % modulo --> 34499628904269660561674201530767158034393542375844615658184142552908072257357 dy = (Qy - Py) % modulo --> 95279978516251208768455708490894263304954079172022948940317551626939868843169 c = dy * invert(dx) % modulo --> 23578750110654438173404407907450265080473019639451825850605815020978465167024 Rx = (c*c - Px - Qx) % modulo --> 112711660439710606056748659173929673102114977341539408544630613555209775888121 ( x coordinate of point (2+1 =3)Ry = (c*(Px - Rx) - Py) % modulo --> 25583027980570883691656905877401976406448868254816295069919888960541586679410 ( y coordinate of point (2+1 =3)Can't explain better Order: 115792089237316195423570985008687907852837564279074904382605163141518161494337 Base Point: (55066263022277343669578718895168534326250603453777594175500187360389116729240, 32670510020758816978083085130507043184471273380659243275938904335757337482424) Modulo: 115792089237316195423570985008687907853269984665640564039457584007908834671663 Private key: 0000000000000000000000000000000000000000000000000000000000000003 Point addition:(2G+1G =3G) Compressed public key; In decimal; Equation: c = (qy py) / (qx px) rx = c^2 px qx px = 89565891926547004231252920425935692360644145829622209833684329913297188986597 py = 12158399299693830322967808612713398636155367887041628176798871954788371653930 qx = 55066263022277343669578718895168534326250603453777594175500187360389116729240 qy = 32670510020758816978083085130507043184471273380659243275938904335757337482424 c = 32670510020758816978083085130507043184471273380659243275938904335757337482424- 12158399299693830322967808612713398636155367887041628176798871954788371653930= 20512110721064986655115276517793644548315905493617615099140032380968965828494 c = 55066263022277343669578718895168534326250603453777594175500187360389116729240- 89565891926547004231252920425935692360644145829622209833684329913297188986597= 81292460333046534861896783477920749818876442289795948381273441455000762414306 c = 20512110721064986655115276517793644548315905493617615099140032380968965828494/ 81292460333046534861896783477920749818876442289795948381273441455000762414306= 23578750110654438173404407907450265080473019639451825850605815020978465167024 c = 23578750110654438173404407907450265080473019639451825850605815020978465167024 rx = 23578750110654438173404407907450265080473019639451825850605815020978465167024^2 - 89565891926547004231252920425935692360644145829622209833684329913297188986597- 55066263022277343669578718895168534326250603453777594175500187360389116729240 rx = 25759636913902563110438328477658084082469757293658084474899962813078412260632- 34499628904269660561674201530767158034393542375844615658184142552908072257357 rx = 107052097246949097972335111955578833901346199583454032856173404268079174674938 rx hex = 0xecad56ff86123a68f47514b195ab6837ba69c1fbdf0beb6339e6f3caead069fa Now I will try to calculate the private key 0000000000000000000000000000000000000000000000000000000000000005 |
|
|
|
BASE16
Member
 
 Offline Offline
Activity: 180
Merit: 38

|
 |
September 14, 2020, 01:18:48 PM
Last edit: September 14, 2020, 01:30:07 PM by BASE16 |
|
Private key 3 is 3 * G
Add the Generator 3 times.
0x02F9308A019258C31049344F85F89D5229B531C845836F99B08601F113BCE036F9
Point 1 {x: 55066263022277343669578718895168534326250603453777594175500187360389116729240n,
y: 32670510020758816978083085130507043184471273380659243275938904335757337482424n}
X: 0x79be667ef9dcbbac55a06295ce870b07029bfcdb2dce28d959f2815b16f81798
Y: 0x483ada7726a3c4655da4fbfc0e1108a8fd17b448a68554199c47d08ffb10d4b8
Point 2 {x: 89565891926547004231252920425935692360644145829622209833684329913297188986597n,
y: 12158399299693830322967808612713398636155367887041628176798871954788371653930n}
X: 0xc6047f9441ed7d6d3045406e95c07cd85c778e4b8cef3ca7abac09b95c709ee5
Y: 0x1ae168fea63dc339a3c58419466ceaeef7f632653266d0e1236431a950cfe52a
Point 3 {x: 112711660439710606056748659173929673102114977341539408544630613555209775888121n,
y: 25583027980570883691656905877401976406448868254816295069919888960541586679410n}
X: 0xf9308a019258c31049344f85f89d5229b531c845836f99b08601f113bce036f9
Y: 0x388f7b0f632de8140fe337e62a37f3566500a99934c2231b6cb9fd7584b8e672
|
|
|
|
|
ricardosuperx (OP)
Member
 
 Offline Offline
Activity: 109
Merit: 13
A positive attitude changes everything *_*

|
 |
September 14, 2020, 01:56:03 PM
Last edit: September 14, 2020, 02:53:51 PM by ricardosuperx |
|
Private key 3 is 3 * G
Add the Generator 3 times.
0x02F9308A019258C31049344F85F89D5229B531C845836F99B08601F113BCE036F9
Point 1 {x: 55066263022277343669578718895168534326250603453777594175500187360389116729240n,
y: 32670510020758816978083085130507043184471273380659243275938904335757337482424n}
X: 0x79be667ef9dcbbac55a06295ce870b07029bfcdb2dce28d959f2815b16f81798
Y: 0x483ada7726a3c4655da4fbfc0e1108a8fd17b448a68554199c47d08ffb10d4b8
Point 2 {x: 89565891926547004231252920425935692360644145829622209833684329913297188986597n,
y: 12158399299693830322967808612713398636155367887041628176798871954788371653930n}
X: 0xc6047f9441ed7d6d3045406e95c07cd85c778e4b8cef3ca7abac09b95c709ee5
Y: 0x1ae168fea63dc339a3c58419466ceaeef7f632653266d0e1236431a950cfe52a
Point 3 {x: 112711660439710606056748659173929673102114977341539408544630613555209775888121n,
y: 25583027980570883691656905877401976406448868254816295069919888960541586679410n}
X: 0xf9308a019258c31049344f85f89d5229b531c845836f99b08601f113bce036f9
Y: 0x388f7b0f632de8140fe337e62a37f3566500a99934c2231b6cb9fd7584b8e672
Corrected, thanks! X: 0xf9308a019258c31049344f85f89d5229b531c845836f99b08601f113bce036f9 Y: 0x388f7b0f632de8140fe337e62a37f3566500a99934c2231b6cb9fd7584b8e672 EDITED:THIS IS THE KEY PUBLIC OF THE PRIVATE KEY 0000000000000000000000000000000000000000000000000000000000000003 |
|
|
|
BASE16
Member
 
 Offline Offline
Activity: 180
Merit: 38

|
 |
September 14, 2020, 02:19:04 PM |
|
Private key 3 is 3 * G
Add the Generator 3 times.
0x02F9308A019258C31049344F85F89D5229B531C845836F99B08601F113BCE036F9
Point 1 {x: 55066263022277343669578718895168534326250603453777594175500187360389116729240n,
y: 32670510020758816978083085130507043184471273380659243275938904335757337482424n}
X: 0x79be667ef9dcbbac55a06295ce870b07029bfcdb2dce28d959f2815b16f81798
Y: 0x483ada7726a3c4655da4fbfc0e1108a8fd17b448a68554199c47d08ffb10d4b8
Point 2 {x: 89565891926547004231252920425935692360644145829622209833684329913297188986597n,
y: 12158399299693830322967808612713398636155367887041628176798871954788371653930n}
X: 0xc6047f9441ed7d6d3045406e95c07cd85c778e4b8cef3ca7abac09b95c709ee5
Y: 0x1ae168fea63dc339a3c58419466ceaeef7f632653266d0e1236431a950cfe52a
Point 3 {x: 112711660439710606056748659173929673102114977341539408544630613555209775888121n,
y: 25583027980570883691656905877401976406448868254816295069919888960541586679410n}
X: 0xf9308a019258c31049344f85f89d5229b531c845836f99b08601f113bce036f9
Y: 0x388f7b0f632de8140fe337e62a37f3566500a99934c2231b6cb9fd7584b8e672
Corrected, thanks! Now What do I do with: X: 0xf9308a019258c31049344f85f89d5229b531c845836f99b08601f113bce036f9 Y: 0x388f7b0f632de8140fe337e62a37f3566500a99934c2231b6cb9fd7584b8e672 ? What do you want to do with it ? You can turn it into uncompressed public key: publicKey = '04' + X + Y publicKey = 04f9308a019258c31049344f85f89d5229b531c845836f99b08601f113bce036f9388f7b0f632de 8140fe337e62a37f3566500a99934c2231b6cb9fd7584b8e672 Or turn it into a even compressed public key: publicKey = '02' + X publicKey = 02f9308a019258c31049344f85f89d5229b531c845836f99b08601f113bce036f9 Or turn it into a odd compressed public key: publicKey = '03' + X publicKey = 03f9308a019258c31049344f85f89d5229b531c845836f99b08601f113bce036f9 One of the last two is invalid. You have to look at the least significant bit of Y to see if its odd or even. Y = 0x388F7B0F632DE8140FE337E62A37F3566500A99934C2231B6CB9FD7584B8E672 Y = 0b11100010001111011110110000111101100011001011011110100000010100000011111110001 1001101111110011000101010001101111111001101010110011001010000000010101001100110 0100110100110000100010001100011011011011001011100111111101011101011000010010111 0001110011001110010 The last bit is even so it's '02' You can also convert it to WIF: 5HpHagT65TZzG1PH3CSu63k8DbpvD8s5ip4nEB3kEsreB1FQ8BZ uncompressed KwDiBf89QgGbjEhKnhXJuH7LrciVrZi3qYjgd9M7rFU74sHUHy8S compressed And you can calculate various addresses but that is far past private to pubkey  |
|
|
|
|
ricardosuperx (OP)
Member
 
 Offline Offline
Activity: 109
Merit: 13
A positive attitude changes everything *_*

|
 |
September 14, 2020, 02:43:58 PM
Last edit: September 14, 2020, 02:57:31 PM by ricardosuperx |
|
Private key 3 is 3 * G
Add the Generator 3 times.
0x02F9308A019258C31049344F85F89D5229B531C845836F99B08601F113BCE036F9
Point 1 {x: 55066263022277343669578718895168534326250603453777594175500187360389116729240n,
y: 32670510020758816978083085130507043184471273380659243275938904335757337482424n}
X: 0x79be667ef9dcbbac55a06295ce870b07029bfcdb2dce28d959f2815b16f81798
Y: 0x483ada7726a3c4655da4fbfc0e1108a8fd17b448a68554199c47d08ffb10d4b8
Point 2 {x: 89565891926547004231252920425935692360644145829622209833684329913297188986597n,
y: 12158399299693830322967808612713398636155367887041628176798871954788371653930n}
X: 0xc6047f9441ed7d6d3045406e95c07cd85c778e4b8cef3ca7abac09b95c709ee5
Y: 0x1ae168fea63dc339a3c58419466ceaeef7f632653266d0e1236431a950cfe52a
Point 3 {x: 112711660439710606056748659173929673102114977341539408544630613555209775888121n,
y: 25583027980570883691656905877401976406448868254816295069919888960541586679410n}
X: 0xf9308a019258c31049344f85f89d5229b531c845836f99b08601f113bce036f9
Y: 0x388f7b0f632de8140fe337e62a37f3566500a99934c2231b6cb9fd7584b8e672
Corrected, thanks! Now What do I do with: X: 0xf9308a019258c31049344f85f89d5229b531c845836f99b08601f113bce036f9 Y: 0x388f7b0f632de8140fe337e62a37f3566500a99934c2231b6cb9fd7584b8e672 ? What do you want to do with it ? You can turn it into uncompressed public key: publicKey = '04' + X + Y publicKey = 04f9308a019258c31049344f85f89d5229b531c845836f99b08601f113bce036f9388f7b0f632de 8140fe337e62a37f3566500a99934c2231b6cb9fd7584b8e672 Or turn it into a even compressed public key: publicKey = '02' + X publicKey = 02f9308a019258c31049344f85f89d5229b531c845836f99b08601f113bce036f9 Or turn it into a odd compressed public key: publicKey = '03' + X publicKey = 03f9308a019258c31049344f85f89d5229b531c845836f99b08601f113bce036f9 One of the last two is invalid. You have to look at the least significant bit of Y to see if its odd or even. Y = 0x388F7B0F632DE8140FE337E62A37F3566500A99934C2231B6CB9FD7584B8E672 Y = 0b11100010001111011110110000111101100011001011011110100000010100000011111110001 1001101111110011000101010001101111111001101010110011001010000000010101001100110 0100110100110000100010001100011011011011001011100111111101011101011000010010111 0001110011001110010 The last bit is even so it's '02' You can also convert it to WIF: 5HpHagT65TZzG1PH3CSu63k8DbpvD8s5ip4nEB3kEsreB1FQ8BZ uncompressed KwDiBf89QgGbjEhKnhXJuH7LrciVrZi3qYjgd9M7rFU74sHUHy8S compressed And you can calculate various addresses but that is far past private to pubkey  SORRY! I convert in decimal: 02f9308a019258c31049344f85f89d5229b531c845836f99b08601f113bce036f9, instead of: 0xf9308a019258c31049344f85f89d5229b531c845836f99b08601f113bce036f9  Now I will try to calculate the private key 0000000000000000000000000000000000000000000000000000000000000005 |
|
|
|
BASE16
Member
 
 Offline Offline
Activity: 180
Merit: 38

|
 |
September 14, 2020, 02:56:53 PM |
|
SORRY! I convert in decimal: 02f9308a019258c31049344f85f89d5229b531c845836f99b08601f113bce036f9, instead of: 0xf9308a019258c31049344f85f89d5229b531c845836f99b08601f113bce036f9  It's both the same in BASE16. The first one is public key with prefix ready for processing while the second has 0x prefix to tell that it's hexadecimal but you can tell that easily by looking at the symbols. You can easily convert them if you want. Just use whatever works best for you  I still don't know what you are trying to do exactly. |
|
|
|
|
ricardosuperx (OP)
Member
 
 Offline Offline
Activity: 109
Merit: 13
A positive attitude changes everything *_*

|
 |
September 14, 2020, 03:08:32 PM |
|
SORRY! I convert in decimal: 02f9308a019258c31049344f85f89d5229b531c845836f99b08601f113bce036f9, instead of: 0xf9308a019258c31049344f85f89d5229b531c845836f99b08601f113bce036f9  It's both the same in BASE16. The first one is public key with prefix ready for processing while the second has 0x prefix to tell that it's hexadecimal but you can tell that easily by looking at the symbols. You can easily convert them if you want. Just use whatever works best for you  I still don't know what you are trying to do exactly. I'm just trying to learn the math behind bitcoin! I was always curious to understand how public keys are created and how Bitcoin works etc ... I was able to understand how to double points and now I understand addition points I'm feeling like a SATOSHI NAKAMOTO LOL  |
|
|
|
bytcoin
Member
 
 Offline Offline
Activity: 211
Merit: 20
$$$$$$$$$$$$$$$$$$$$$$$$$

|
 |
September 15, 2020, 05:44:39 PM |
|
If the formula is always the same, All public keys will also always be the same! "Where am I wrong?
(dx, dy, c, R.x, R.y, Q.x Q.y, P.x, P.y)Can someone explain to me what are this?
I think Rx and Ry are the coordinates of the public key, right?
ok, I will try to explain as simply as possible because it is true that I myself struggled to understand the system. So it is a question here of adding 2 points (not the same). In this example we use : first point: (all values are in décimal for a better comprehension) X coordinate: 21262057306151627953595685090280431278183829487175876377991189246716355947009 (it is Qx) Y coordinate: 41749993296225487051377864631615517161996906063147759678534462689479575333124 (it is Qy) The Private key for this point is 0000000000000000000000000000000000000000000000000000000000000008 second point to add: X coordinate: 89565891926547004231252920425935692360644145829622209833684329913297188986597 (it is Px) Y coordinate: 12158399299693830322967808612713398636155367887041628176798871954788371653930 (it is Py) The Private key for this point is 0000000000000000000000000000000000000000000000000000000000000002 So to add the 1st point to the second we use the formula : (here modulo is 115792089237316195423570985008687907853269984665640564039457584007908834671663 ) dx = (Q.x - P.x) % modulo dy = (Q.y - P.y) % modulo c = dy * invert(dx) % modulo R.x = (c*c - P.x - Q.x) % modulo R.y = (c*(P.x - R.x) - P.y) % modulo in our example we have dx = (21262057306151627953595685090280431278183829487175876377991189246716355947009 - 89565891926547004231252920425935692360644145829622209833684329913297188986597) % modulo dx = 47488254616920819145913749673032646770809668323194230583764443341328001632075 dy = (41749993296225487051377864631615517161996906063147759678534462689479575333124 - 12158399299693830322967808612713398636155367887041628176798871954788371653930) % modulo dy = 29591593996531656728410056018902118525841538176106131501735590734691203679194 invert of dx = 70279122268919195963430815486314537773961171454828771794853116552210630553734 c = dy * invert(dx) % modulo c = 16132032934385503768504319366562120314980927452732756733183380715276156205226 So the new point (8 + 2) R.x = (c*c - P.x - Q.x) % modulo R.x --> X coordinate of (8+2) = 72488970228380509287422715226575535698893157273063074627791787432852706183111 R.y = (c*(P.x - R.x) - P.y) % modulo R.y --> Y coordinate of (8+2) = 62070622898698443831883535403436258712770888294397026493185421712108624767191 If we check these coordinates, we find that it corresponds to the private key: 000000000000000000000000000000000000000000000000000000000000000a (10) There you go, I hope I was as clear as possible and apologies for my broken English ^^ [/quote] Good explanation ... I understood perfectly |
|
|
|
|
bytcoin
Member
 
 Offline Offline
Activity: 211
Merit: 20
$$$$$$$$$$$$$$$$$$$$$$$$$

|
 |
September 15, 2020, 05:47:36 PM |
|
That's what I wanted! Could you make private key 3?
We must not forget that there are two formulas The one you used to find the point corresponding to the private key: 2 (or rather 0000000000000000000000000000000000000000000000000000000000000002 to be more precise) it is Duplication of points. You did it in your example with the base point--> 1 + 1 =2 ( but that could be another point) To go now with 3 we need to do --> 2 + 1 = 3 (we have now 2 différents points and we can't doubling them) For that you need to use the second formula: modulo = 115792089237316195423570985008687907853269984665640564039457584007908834671663 Px = 89565891926547004231252920425935692360644145829622209833684329913297188986597 (x coordinate point 2) Py = 12158399299693830322967808612713398636155367887041628176798871954788371653930 (y coordinate point 2) Qx = 55066263022277343669578718895168534326250603453777594175500187360389116729240 (x coordinate point 1) not because it is the base point, just because it is the point n°1Qy = 32670510020758816978083085130507043184471273380659243275938904335757337482424 (y coordinate point 1) dx = (Qx - Px) % modulo --> 34499628904269660561674201530767158034393542375844615658184142552908072257357 dy = (Qy - Py) % modulo --> 95279978516251208768455708490894263304954079172022948940317551626939868843169 c = dy * invert(dx) % modulo --> 23578750110654438173404407907450265080473019639451825850605815020978465167024 Rx = (c*c - Px - Qx) % modulo --> 112711660439710606056748659173929673102114977341539408544630613555209775888121 ( x coordinate of point (2+1 =3)Ry = (c*(Px - Rx) - Py) % modulo --> 25583027980570883691656905877401976406448868254816295069919888960541586679410 ( y coordinate of point (2+1 =3)Can't explain better Order: 115792089237316195423570985008687907852837564279074904382605163141518161494337 Base Point: (55066263022277343669578718895168534326250603453777594175500187360389116729240, 32670510020758816978083085130507043184471273380659243275938904335757337482424) Modulo: 115792089237316195423570985008687907853269984665640564039457584007908834671663 Private key: 0000000000000000000000000000000000000000000000000000000000000003 Point addition:(2G+1G =3G) Compressed public key; In decimal; Equation: c = (qy py) / (qx px) rx = c^2 px qx px = 89565891926547004231252920425935692360644145829622209833684329913297188986597 py = 12158399299693830322967808612713398636155367887041628176798871954788371653930 qx = 55066263022277343669578718895168534326250603453777594175500187360389116729240 qy = 32670510020758816978083085130507043184471273380659243275938904335757337482424 c = 32670510020758816978083085130507043184471273380659243275938904335757337482424- 12158399299693830322967808612713398636155367887041628176798871954788371653930= 20512110721064986655115276517793644548315905493617615099140032380968965828494 c = 55066263022277343669578718895168534326250603453777594175500187360389116729240- 89565891926547004231252920425935692360644145829622209833684329913297188986597= 81292460333046534861896783477920749818876442289795948381273441455000762414306 c = 20512110721064986655115276517793644548315905493617615099140032380968965828494/ 81292460333046534861896783477920749818876442289795948381273441455000762414306= 23578750110654438173404407907450265080473019639451825850605815020978465167024 c = 23578750110654438173404407907450265080473019639451825850605815020978465167024 rx = 23578750110654438173404407907450265080473019639451825850605815020978465167024^2 - 89565891926547004231252920425935692360644145829622209833684329913297188986597- 55066263022277343669578718895168534326250603453777594175500187360389116729240 rx = 25759636913902563110438328477658084082469757293658084474899962813078412260632- 34499628904269660561674201530767158034393542375844615658184142552908072257357 rx = 107052097246949097972335111955578833901346199583454032856173404268079174674938 rx hex = 0xecad56ff86123a68f47514b195ab6837ba69c1fbdf0beb6339e6f3caead069fa Now I will try to calculate the private key 0000000000000000000000000000000000000000000000000000000000000005 @ricardosuperx, rx should be DEC 112711660439710606056748659173929673102114977341539408544630613555209775888121 HEX 0xf9308a019258c31049344f85f89d5229b531c845836f99b08601f113bce036f9 |
|
|
|
|
ricardosuperx (OP)
Member
 
 Offline Offline
Activity: 109
Merit: 13
A positive attitude changes everything *_*

|
 |
September 15, 2020, 09:54:14 PM |
|
|
|
|
|
|
MrFreeDragon
|
 |
September 15, 2020, 10:32:16 PM |
|
Why do not you examine the messages above? There are two different formulas: one for duplication and another for addition. To be honest your messages are very hard to read. It could be more helpful for you if you can ask the specific question you do not understand or have issues with. |
|
|
|
ricardosuperx (OP)
Member
 
 Offline Offline
Activity: 109
Merit: 13
A positive attitude changes everything *_*

|
 |
September 15, 2020, 10:40:56 PM
Last edit: September 15, 2020, 11:34:52 PM by ricardosuperx |
|
Why do not you examine the messages above? There are two different formulas: one for duplication and another for addition. To be honest your messages are very hard to read. It could be more helpful for you if you can ask the specific question you do not understand or have issues with. SORRY! My English is bad and I'm not good at math or programming. Duplicate point I already understood That will be my last question. What did I do wrong? Point addition:(2G+1G =3G) Why was my result not: 112711660439710606056748659173929673102114977341539408544630613555209775888121? Order: 115792089237316195423570985008687907852837564279074904382605163141518161494337 Modulo: 115792089237316195423570985008687907853269984665640564039457584007908834671663 Private key: 0000000000000000000000000000000000000000000000000000000000000003 Point addition:(2G+1G =3G) Compressed public key; In decimal; Equation: c = (qy py) / (qx px) rx = c^2 px qx px = 89565891926547004231252920425935692360644145829622209833684329913297188986597 py = 12158399299693830322967808612713398636155367887041628176798871954788371653930 qx = 55066263022277343669578718895168534326250603453777594175500187360389116729240 qy = 32670510020758816978083085130507043184471273380659243275938904335757337482424 c = 32670510020758816978083085130507043184471273380659243275938904335757337482424- 12158399299693830322967808612713398636155367887041628176798871954788371653930= 20512110721064986655115276517793644548315905493617615099140032380968965828494 c = 55066263022277343669578718895168534326250603453777594175500187360389116729240- 89565891926547004231252920425935692360644145829622209833684329913297188986597= 81292460333046534861896783477920749818876442289795948381273441455000762414306 c = 20512110721064986655115276517793644548315905493617615099140032380968965828494/ 81292460333046534861896783477920749818876442289795948381273441455000762414306= 23578750110654438173404407907450265080473019639451825850605815020978465167024 c = 23578750110654438173404407907450265080473019639451825850605815020978465167024 rx = 23578750110654438173404407907450265080473019639451825850605815020978465167024^2 - 89565891926547004231252920425935692360644145829622209833684329913297188986597- 55066263022277343669578718895168534326250603453777594175500187360389116729240 rx = 25759636913902563110438328477658084082469757293658084474899962813078412260632- 34499628904269660561674201530767158034393542375844615658184142552908072257357 rx = 107052097246949097972335111955578833901346199583454032856173404268079174674938 Correct resultt:112711660439710606056748659173929673102114977341539408544630613555209775888121 |
|
|
|
archyone
Newbie

 Offline Offline
Activity: 25
Merit: 1

|
 |
September 16, 2020, 05:30:48 AM |
|
c = (qy py) / (qx px)
rx = c^2 px qx
Wrong formula
Use this one -->
dx = (Qx - Px) % modulo
dy = (Qy - Py) % modulo
c = dy * invert(dx) % modulo
Rx = (c*c - Px - Qx) % modulo
Ry = (c*(Px - Rx) - Py) % modulo
|
|
|
|
|
|
MrFreeDragon
|
 |
September 16, 2020, 11:57:34 AM |
|
c = (qy py) / (qx px)
rx = c^2 px qx
Wrong formula
Use this one -->
dx = (Qx - Px) % modulo
dy = (Qy - Py) % modulo
c = dy * invert(dx) % modulo
Rx = (c*c - Px - Qx) % modulo
Ry = (c*(Px - Rx) - Py) % modulo
Formula is correct. Actually invert(dx) is (qx px), so c = dy * invert(dx) is the same as c = (qy py) / (qx px) |
|
|
|
|
MrFreeDragon
|
 |
September 16, 2020, 12:41:22 PM |
|
-snip-
rx = 23578750110654438173404407907450265080473019639451825850605815020978465167024^2 -
89565891926547004231252920425935692360644145829622209833684329913297188986597-
55066263022277343669578718895168534326250603453777594175500187360389116729240
rx = 25759636913902563110438328477658084082469757293658084474899962813078412260632-
34499628904269660561674201530767158034393542375844615658184142552908072257357
rx = 107052097246949097972335111955578833901346199583454032856173404268079174674938
Correct resultt:112711660439710606056748659173929673102114977341539408544630613555209775888121
Your calculations of dx, dy and c are correct. However while calculating the rx you made a simple arithmetical mistake - you should deduct step by step, but not make the last deduction first and later deduct the result from the first part. I marked by red the wrong part of your calculation - you changed the sign of px: instead of rx = c^2 px qx you calculated rx = c^2 + px qx (wrong!!) Your calculation should be the following: rx = 23578750110654438173404407907450265080473019639451825850605815020978465167024^2 - 89565891926547004231252920425935692360644145829622209833684329913297188986597- 55066263022277343669578718895168534326250603453777594175500187360389116729240 rx = 25759636913902563110438328477658084082469757293658084474899962813078412260632 - 89565891926547004231252920425935692360644145829622209833684329913297188986597- 55066263022277343669578718895168534326250603453777594175500187360389116729240 rx = 51985834224671754302756393060410299575095596129676438680673216907690057945698- 55066263022277343669578718895168534326250603453777594175500187360389116729240 rx = 112711660439710606056748659173929673102114977341539408544630613555209775888121PS. You can also calculate in your way, however instead of deducting you should should apply the addition to last 2 decimals deducted from the c*c. This is the possible way as well: rx = c^2 px qx = rx = c^2 (px + qx)Keep in mind that as you combined the last 2 decimals, you should add them first and later deduct from the 1st part}. In general, you mistake is simple math arithmetical. Just be careful with the calculation. |
|
|
|
ricardosuperx (OP)
Member
 
 Offline Offline
Activity: 109
Merit: 13
A positive attitude changes everything *_*

|
 |
September 16, 2020, 07:18:57 PM |
|
I would like to thank everyone who helped me understand. Sorry for being boring.
I'm really happy to finally understand how to duplicate points and also calculate addition points
The Bitcoin community is amazing!
In my opinion, the Bitcoin community has helped Bitcoin to be a success
|
|
|
|
|
bigvito19
|
 |
September 17, 2020, 01:31:10 PM |
|
Does anyone know the correct math and is there a script to do the math for you or do you have to do the math manually?
|
|
|
|
|
|
MrFreeDragon
|
 |
September 17, 2020, 07:30:30 PM |
|
Does anyone know the correct math and is there a script to do the math for you or do you have to do the math manually?
Please find the python script to do the elliptic curve math. It is recommended to use gmpy2 library (it is 50 times faster). However if you do not have installed gmpy2 library, just change the formula for c in functions mul2 and add (you should uncomment the formula for c with self-written modinv function and comment the formula for c with gmpy2 library). How to use this scrpipt: PG is the basis point G (actully the point for private key number 1) mul2 function makes the duplication of the point (i.e. mul2(PG) returns the Point for private key 2 add function performs the addition of 2 different points (i.e. add(mul2(PG),PG) returns the Point for private key 3 in the way 1*2+1 = 3) mulk function multiplies the Point by k number (i.e. you can use it in order to receive the Public point for any private key, for example, for private key 1000 you can calculate the public point in this way: mulk(1000,PG) - multiplies basis point G by 1000). import gmpy2
modulo = 0xFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFEFFFFFC2F
order = 0xFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFEBAAEDCE6AF48A03BBFD25E8CD0364141
Gx = 0x79BE667EF9DCBBAC55A06295CE870B07029BFCDB2DCE28D959F2815B16F81798
Gy = 0X483ADA7726A3C4655DA4FBFC0E1108A8FD17B448A68554199C47D08FFB10D4B8
class Point:
def __init__(self, x=0, y=0):
self.x = x
self.y = y
PG = Point(Gx,Gy)
Z = Point(0,0) # zero-point, infinite in real x,y - plane
# return (g, x, y) a*x + b*y = gcd(x, y)
def egcd(a, b):
if a == 0:
return (b, 0, 1)
else:
g, x, y = egcd(b % a, a)
return (g, y - (b // a) * x, x)
def modinv(m, n = modulo):
while m < 0:
m += n
g, x, _ = egcd(m, n)
if g == 1:
return x % n
else: print (' no inverse exist')
def mul2(Pmul2, p = modulo):
R = Point(0,0)
#c = 3*Pmul2.x*Pmul2.x*modinv(2*Pmul2.y, p) % p
c = 3*Pmul2.x*Pmul2.x*gmpy2.invert(2*Pmul2.y, p) % p
R.x = (c*c-2*Pmul2.x) % p
R.y = (c*(Pmul2.x - R.x)-Pmul2.y) % p
return R
def add(Padd, Q, p = modulo):
if Padd.x == Padd.y == 0: return Q
if Q.x == Q.y == 0: return Padd
if Padd == Q: return mul2(Q)
R = Point()
dx = (Q.x - Padd.x) % p
dy = (Q.y - Padd.y) % p
c = dy * gmpy2.invert(dx, p) % p
#c = dy * modinv(dx, p) % p
R.x = (c*c - Padd.x - Q.x) % p
R.y = (c*(Padd.x - R.x) - Padd.y) % p
return R # 6 sub, 3 mul, 1 inv
def mulk(k, Pmulk, p = modulo):
if k == 0: return Z
if k == 1: return Pmulk
if (k % 2 == 0): return mulk(k//2, mul2(Pmulk, p), p)
return add(Pmulk, mulk((k-1)//2, mul2(Pmulk, p), p), p)
|
|
|
|
BASE16
Member
 
 Offline Offline
Activity: 180
Merit: 38

|
 |
September 18, 2020, 10:34:38 AM
Last edit: September 18, 2020, 02:32:52 PM by BASE16 |
|
# Super simple Elliptic Curve Presentation. No imported libraries, wrappers, nothing.
# For educational purposes only. Remember to use Python 2.7.6 or lower. You'll need to make changes for Python 3.
# Below are the public specs for Bitcoin's curve - the secp256k1
Pcurve = 2**256 - 2**32 - 2**9 - 2**8 - 2**7 - 2**6 - 2**4 -1 # The proven prime
N=0xFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFEBAAEDCE6AF48A03BBFD25E8CD0364141 # Number of points in the field
Acurve = 0; Bcurve = 7 # These two defines the elliptic curve. y^2 = x^3 + Acurve * x + Bcurve
Gx = 55066263022277343669578718895168534326250603453777594175500187360389116729240
Gy = 32670510020758816978083085130507043184471273380659243275938904335757337482424
GPoint = (Gx,Gy) # This is our generator point. Trillions of dif ones possible
#Individual Transaction/Personal Information
privKey = 0xA0DC65FFCA799873CBEA0AC274015B9526505DAAAED385155425F7337704883E #replace with any private key
def modinv(a,n=Pcurve): #Extended Euclidean Algorithm/'division' in elliptic curves
lm, hm = 1,0
low, high = a%n,n
while low > 1:
ratio = high/low
nm, new = hm-lm*ratio, high-low*ratio
lm, low, hm, high = nm, new, lm, low
return lm % n
def ECadd(a,b): # Not true addition, invented for EC. Could have been called anything.
LamAdd = ((b[1]-a[1]) * modinv(b[0]-a[0],Pcurve)) % Pcurve
x = (LamAdd*LamAdd-a[0]-b[0]) % Pcurve
y = (LamAdd*(a[0]-x)-a[1]) % Pcurve
return (x,y)
def ECdouble(a): # This is called point doubling, also invented for EC.
Lam = ((3*a[0]*a[0]+Acurve) * modinv((2*a[1]),Pcurve)) % Pcurve
x = (Lam*Lam-2*a[0]) % Pcurve
y = (Lam*(a[0]-x)-a[1]) % Pcurve
return (x,y)
def EccMultiply(GenPoint,ScalarHex): #Double & add. Not true multiplication
if ScalarHex == 0 or ScalarHex >= N: raise Exception("Invalid Scalar/Private Key")
ScalarBin = str(bin(ScalarHex))[2:]
Q=GenPoint
for i in range (1, len(ScalarBin)): # This is invented EC multiplication.
Q=ECdouble(Q); # print "DUB", Q[0]; print
if ScalarBin[i] == "1":
Q=ECadd(Q,GenPoint); # print "ADD", Q[0]; print
return (Q)
print; print "******* Public Key Generation *********";
print
PublicKey = EccMultiply(GPoint,privKey)
print "the private key:";
print privKey; print
print "the uncompressed public key (not address):";
print PublicKey; print
print "the uncompressed public key (HEX):";
print "04" + "%064x" % PublicKey[0] + "%064x" % PublicKey[1];
print;
print "the official Public Key - compressed:";
if PublicKey[1] % 2 == 1: # If the Y value for the Public Key is odd.
print "03"+str(hex(PublicKey[0])[2:-1]).zfill(64)
else: # Or else, if the Y value is even.
print "02"+str(hex(PublicKey[0])[2:-1]).zfill(64)
For some unknown reason the forum software seems to alter the code inside the code tag so here is the original code on github: https://raw.githubusercontent.com/wobine/blackboard101/master/EllipticCurvesPart4-PrivateKeyToPublicKey.py |
|
|
|
|
|



