Not sure if you guys have heard about this story, but since I'm more of a traditional land base players and so are others here, let me share you this story, LAS VEGAS (AP) From its lavish opening in 1957 on a Las Vegas Boulevard surrounded by wide-open desert, to its sleepier years amid a boom in megaresorts, the Tropicana Las Vegas has been a familiar landmark home to colorful events in a city known for constant reinvention.
Now its a jewel of Sin Citys past. After 67 years, the Strips third-oldest casino shut its doors for good on Tuesday. Demolition is slated for October to make room for a $1.5 billion Major League Baseball stadium for the relocating Oakland Athletics part of Las Vegas latest rebrand as a hub for sports entertainment. https://apnews.com/article/tropicana-casino-history-las-vegas-strip-3334ab06fdd11ada3b181813d2f04649And this is the final hour,  I'll probably played at least once here in 99-00, if my memories serves me right. (I'm not stateside btw). Anyone in the US has experience going into this casinos and maybe shared their thoughts? |
|
|
|
 I advise everyone to see this video, I'm not related to this person, but I can relate to his stories and the gambling addiction that most of us could have been suffering for years. This is the second video that I have been watching and they say the same things. Not just money they lose, but time and relationship. The other video that I saw that he was not even present with the delivery of his first and second kid, he was done gambling and trying to make money for the hospital bills but it turns out that he losses in both time. Perhaps you have seen other videos as well and maybe share it here. |
|
|
|
According to this report, SEC is not going to appeal about the recent ruling that they, SEC was found to be wrong in rejecting the application of Grayscale to create a spot Bitcoin ETF. The District of Columbia Court of Appeals in Washington in August ruled that the SEC was wrong to reject Grayscales proposed bitcoin ETF, in a case that has been closely watched by the industry which has been trying for a decade to advance such products.
The SECs decision not to appeal likely paves the way for the agency to review Grayscales application. https://www.cnbc.com/2023/10/13/us-sec-does-not-plan-to-appeal-court-decision-on-grayscale-bitcoin-etf-source-says.htmlSo I guess this is a win for Grayscale already and we might see eventually SEC going to approved spot bitcoin exchange traded fund (ETF) in the future. Although they will have to go to the process of reviewing the application again, but perhaps the chances could be good that we will get an approval and it could set a precedent as well as there are several other asset managers, including BlackRock who also filed for similar ETF. And again, the argument that it could be one factor that could initiate the bull run next year, if we will have a approval in 2024. |
|
|
|
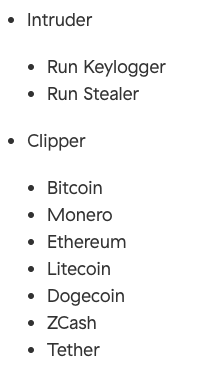
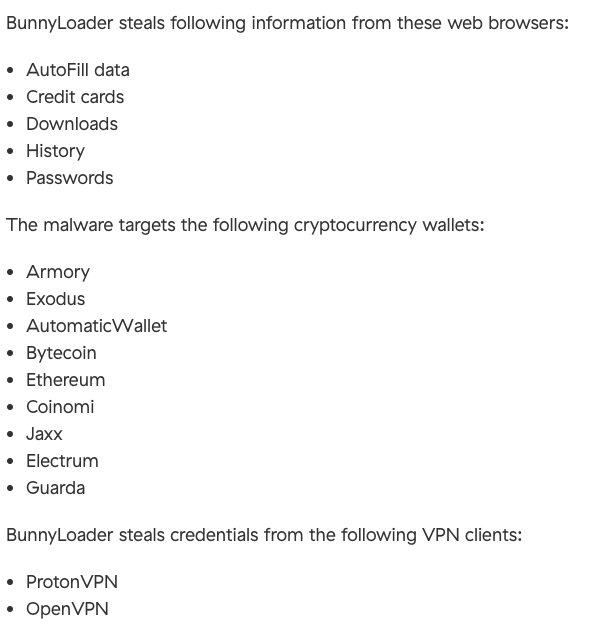
A newly evolved Clipper and a keylogger called BunnyLoader. And we all know that there are a lot of variants of keylogger and clipboard malware that replaces crypto currency wallet with that to a wallet address that this criminal controls. This malware has undergone some transformation already, and it's very clever to see that it will test if your system runs on sandbox and usernames. So the Clipper looks for cryptos: 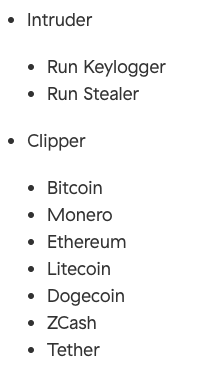 Also looks for this information to steal: 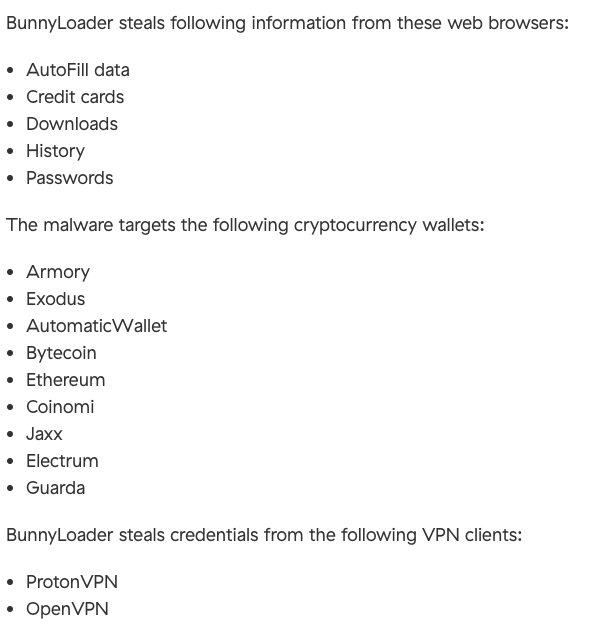 So it's very important for us crypto enthusiast to learn how to protect from this kind of malware. We need to install the latest anti-virus, and not just to download any crack softwares as this is where this criminals exploited their victims. When we thought that we can get free softwares, but we don't know that the criminals have laded it with a lot of malwares and we will only know until it's too late. And for the Clipper capability of this malware, we should check the details of the addresses that we are going to send to, make sure everything is correct so that we will not be a victim here. And obviously, do not click any links like in our email, maybe it doesn't look suspicious at all, but if we don't know the source or even know the source, we should be very very careful. https://www.zscaler.com/blogs/security-research/bunnyloader-newest-malware-service |
|
|
|
A 22-year-old French citizen from Epinal, France, pleaded guilty to conspiracy to commit wire fraud and aggravated identity theft in U.S. District Court in Seattle, announced Acting U.S. Attorney Tessa M. Gorman. Sebastien Raoult, aka Sezyo Kaizen, was arrested last year in Morocco and was extradited to the U.S. in January 2023. Raoult and two co-conspirators were indicted by a grand jury sitting in the Western District of Washington in June 2021.
According to the plea agreement, Raoult and his co-conspirators hacked into protected computers of corporate entities for the theft of confidential information and customer records, including personally identifiable information and financial information. They hacked numerous companies, including companies in Washington State, elsewhere in the United States, and around the world. After Raoult and his co-conspirators hacked companies, a user going by the name ShinyHunters posted hacked data from many of those companies for sale on dark web forums, including RaidForums, EmpireMarket, and Exploit. Between April 2020 and July 2021, ShinyHunters posted sales of hacked data from more than 60 companies. Sometimes ShinyHunters threatened to leak or sell stolen sensitive files if the victim did not pay a ransom.
The conspiracy to commit wire fraud is punishable by a maximum of 27 years in prison. Aggravated identity theft is punishable by a mandatory minimum two-year prison term to follow any other prison sentence imposed in the case.
https://www.justice.gov/usao-wdwa/pr/french-cybercriminal-pleads-guilty-fraud-and-aggravated-identity-theft-hacking-privateSo in a nutshell, the groups Modus Operandi is, - they hacked on the computers of the corporation, stealing confidential information including customer records. - posted this hacked data from for sale in the dark forums, making money out of it - another way is to threatened to leak the data from the customers and demanding ransom - and worst, they used this companies computing power to crypto mineHopefully, the full hands of the law will go and punished this cyber criminals. But there could be more plea bargain though, like him pointing the other names of the group to the FBI so that they could be apprehended as well. And the bad thing is that they are going to milk the data that they got, selling it to other groups to exploit it and then used the business entities even more by installing crypto miner without the company's knowledge on what is going on until it's too late. |
|
|
|
There is another fake Sinbad Mixer https://sinbad.io/ website:  And when you click that link, you will be redirected to:  Fake website: https://slnbad.io/
mixersinbad.io
You won't notice it until you have to take a close look at the spelling. So everyone should be careful about and just check everything before using the mixer. This criminals are cloning every mixer know since the closure of CM. |
|
|
|
It was just announced that Google Authenticator is now getting a cloud backup. We released Google Authenticator in 2010 as a free and easy way for sites to add something you have two-factor authentication (2FA) that bolsters user security when signing in. While were pushing towards a passwordless future, authentication codes remain an important part of internet security today, so we've continued to make optimizations to the Google Authenticator app.
One major piece of feedback weve heard from users over the years was the complexity in dealing with lost or stolen devices that had Google Authenticator installed. Since one time codes in Authenticator were only stored on a single device, a loss of that device meant that users lost their ability to sign in to any service on which theyd set up 2FA using Authenticator.
https://security.googleblog.com/2023/04/google-authenticator-now-supports.html
For sure there could be some of us who are using Google Authenticator here as another layer of protection for our crypto accounts. But as they have explain it, one drawback is that when you lost or your devices are stolen, it's hard to recover it already. But now, they said that they are going to do a backup on the cloud. However, I for one is not comfortable with it. Obviously, it's our responsibility, but what if the Google clouds are hack as well? it is going to be open for all sorts of vulnerabilities in my opinion. What's you take on this? |
|
|
|
What happened:: Fake UNI 200 Airdrop Website: Archived: https://archive.is/OIuGE Whois Record for UnisWap-Ico.com
Registrant WhoisGuard Protected
Registrant Org WhoisGuard, Inc.
Registrant Country pa
Registrar NAMECHEAP INC NameCheap, Inc.
IANA ID: 1068
URL: http://www.namecheap.com
Whois Server: whois.namecheap.com
(p)
Registrar Status clientTransferProhibited
Dates Created on 2021-01-16
Expires on 2022-01-16
Updated on 0000-12-31
Name Servers HAL.NS.CLOUDFLARE.COM (has 17,840,966 domains)
JANET.NS.CLOUDFLARE.COM (has 17,840,966 domains)
Tech Contact WhoisGuard Protected
WhoisGuard, Inc.
P.O. Box 0823-03411,
Panama, Panama, pa
(p) (f)
IP Address 104.21.81.17 - 2 other sites hosted on this server And what makes this very dangerous is that it will ask you to download. This might contains malware if you download and execute it, (don't take the risk here not worth it). https://uniswap-ico.com/uniswap.exe
|
|
|
|
What Happened: Fake XRP explorer Website:  Archived: https://archive.is/r9bCO Archived: https://archive.is/r9bCORegistrant REDACTED FOR PRIVACY
Registrant Org REDACTED FOR PRIVACY
Registrant Country pa
Registrar NameCheap, Inc.
IANA ID: 1068
URL: https://www.namecheap.com/
Whois Server: whois.namecheap.com
(p)
Registrar Status addPeriod, clientTransferProhibited
Dates 3 days old
Created on 2020-11-26
Expires on 2021-11-26
Updated on 2020-11-26
Name Servers NS1.ZOMRO.NET. (has 29,650 domains)
NS2.ZOMRO.RU. (has 79 domains)
Tech Contact REDACTED FOR PRIVACY
REDACTED FOR PRIVACY,
REDACTED FOR PRIVACY, REDACTED FOR PRIVACY, REDACTED FOR PRIVACY, REDACTED FOR PRIVACY
IP Address 185.235.131.163 - 1 other site is hosted on this server
IP Location Netherlands - Drenthe - Meppel - Bilzard Private Enterprise[/quote]
Criminals are now venturing into creating a fake XRP exploring like the scam site above.
Again, the looks are very similar, but the real and true site is: https://bithomp.com/explorer/
|
|
|
|
What happened: Fake Coinbase giveaway Website: https://coinbase2x.online/  Archived: https://archive.is/tU3EA Archived: https://archive.is/tU3EARegistrar Namecheap
IANA ID: 1068
URL: https://namecheap.com
Whois Server: whois.namecheap.com
(p)
Registrar Status addPeriod, clientTransferProhibited, serverTransferProhibited
Dates Created on 2020-11-17
Expires on 2021-11-17
Updated on 2020-11-17
Name Servers DNS1.NAMECHEAPHOSTING.COM (has 964,527 domains)
DNS2.NAMECHEAPHOSTING.COM (has 964,527 domains)
Tech Contact
IP Address 198.54.115.96 - 339 other sites hosted on this server So if you happened to see this website or if someone message you to join, please don't, this is as clear as a scam.
|
|
|
|
What happened: Fake Sushiswapclassic website Website: https://sushiswapclasslc.org/  Archived: https://archive.is/Dqwbc Archived: https://archive.is/DqwbcRegistrant Org WhoisGuard, Inc.
Registrant Country pa
Registrar NameCheap, Inc.
IANA ID: 1068
URL: http://www.namecheap.com
Whois Server: whois.namecheap.com
(p)
Registrar Status serverTransferProhibited
Dates 7 days old
Created on 2020-10-14
Expires on 2021-10-14
Updated on 2020-10-14 Just look closely at the spelling of the fake website, it's hard to identify it in the beginning and you might fall for this trick, be careful.
|
|
|
|
What happened: Fake BTC giveaway by Chamath Palihapitiya Website: Archived: https://archive.is/JNVjH This is a fake BTC giveway, supposedly by Chamath Palihapitiya, CEO of Social Capital BTC address: 1Cham1hgP6wD4SqyzP1cYhPYLDQoAvMY2W Registrant Country pa
Registrar NameCheap, Inc
IANA ID: 1068
URL: www.namecheap.com
Whois Server: whois.namecheap.com
(p)
Registrar Status clientTransferProhibited, serverTransferProhibited
Dates 14 days old
Created on 2020-09-28
Expires on 2021-09-28
Updated on 2020-09-28
|
|
|
|
What happened: Fake Uniswap 10,000,000 Airdrop Website:  Archive: https://archive.is/Ok6FwETH address: Archive: https://archive.is/Ok6FwETH address: 0x1f5b1aee0775fb44a3c2b8185d91afb8f0f613ad And the hype continues about this UNI swap and scammers are very happy with it as they take advantage of these gullible newbies who are blindly trust them. So be careful and warn everyone around you not to fall for this. Registrant Pavel Zuev
Registrant Org Private Person
Registrant Country ru
Registrar Registrar of domain names REG.RU LLC REGISTRAR OF DOMAIN NAMES REG.RU LLC
IANA ID: 1606
URL: https://www.reg.com,https://www.reg.ru,http://www.reg.ru
Whois Server: whois.reg.com
(p)
Registrar Status clientTransferProhibited
Dates 1 days old
Created on 2020-10-03
Expires on 2021-10-03
Updated on 2020-10-03
|
|
|
|
What happened: A fake Uniswap apps on Google Store Website: https://play.google.com/store/apps/details?id=com.uniswap.app  Archive: https://archive.is/JG9pNNote: Archive: https://archive.is/JG9pNNote: Someone has already fallen for it,  https://twitter.com/TRNG_69/status/1311529654721949696 https://twitter.com/TRNG_69/status/1311529654721949696It shows that it has been downloaded 63 times already, so we might hear more crypto enthusiast coming out and claiming that they have been fallen victim from this malicious apps. So be careful when using Google Playstore, and don't blindly downloading any apps without verifying it.
|
|
|
|
First step: Create a 4chan account (easy)  Second step: Buy a .finance domain (easy) Third step: Make ERC20 token on mainnet (easy) Fourth step: Do some coding and upload it to your newly registered domain. No worries even if it is not working. (easy)  Fifth step: Go back to your 4chan and shill (easy) ETH address: https://etherscan.io/token/0x411f0a2e2da53754ff5618512fa1c8b2b5695967 Website: http://www.coconut.finance/ 4Chan: https://boards.4channel.org/biz/thread/22745851/coconut-airdrop I hope you do get my message here. |
|
|
|
What Happened: Fake Atomic wallet Website:  What makes it worst is that it is being displayed through Google ads  And as per domaintools, the website is just 3 days old. So everyone needs to be careful, check everything, specially spelling, because it is really hard to differentiate it from the real website: https://atomicwallet.io/Registrant Org WhoisGuard, Inc. Registrant Country pa Registrar NameCheap, Inc IANA ID: 1068 URL: www.namecheap.comWhois Server: whois.namecheap.com (p) Registrar Status addPeriod, clientTransferProhibited, serverTransferProhibited Dates 3 days old Created on 2020-09-03 Expires on 2021-09-03 Updated on 2020-09-06
|
|
|
|
Coinmarketcap now has a display for DeFi Tokens by Market Capitalization. ( https://coinmarketcap.com/defi/) It's just how they define tokens to be DeFi though, And do you think it's a complete list or something is missing? I think this is great though, specially for those who are not familiar with this new hype is crypto market, so good job CZ (although sometimes I think he is becoming too powerful!). |
|
|
|
Take notice for Bitcoin Gold holders investors and traders and specially miners. You need to upgrade to the latest version if you haven't done so as there are a attack for the third time. This is critical so I suggest all parties concern should be aware of this critical issues. There is an emergency update: Emergency update 0.17.2 CRITICAL MESSAGE FROM BTG TEAM TO ALL POOLS, EXCHANGES, WALLETS, SERVICES, AND COMMUNITY RUNNING NODES Please immediately upgrade your BTG Core full nodes to version 0.17.2, published July 2, 2020. UPDATE: if you did not upgrade prior to July 10 at 14:00 UTC, you will also want to perform the command: invalidateblock 00000000635620f22ba8694aea532d51619f8cd060f4e42e85db3cb3a5d1c29c HOW TO UPGRADE: 1. You can use the pre-compiled binaries on Github, https://github.com/BTCGPU/BTCGPU/releases/tag/v0.17.2, or use the DOWNLOADS link you see above. Simply shut down your node, install the latest version, and start back up. 2. Manually upgrade from the latest code on the BTCGPU Github v0.17.2 tag (on 0.17 / master branch); full release notes here. If you are still at v0.15.2 and havent upgraded to 0.17, we have a backport version v0.15.3 tag (on 0.15 branch) including the same changes so you can keep your current configuration files. (Note: there were potentially breaking changes in the configuration file between v0.15 and v0.17*) You can run this command in the console or bgold-cli to ensure you are immediately on the honest chain: invalidateblock 00000000635620f22ba8694aea532d51619f8cd060f4e42e85db3cb3a5d1c29c Note: a strong majority of the honest mining pools have already upgraded their code a week ago, and continue to mine on the honest chain. The BTG Explorer at https://explorer.bitcoingold.org/ is on the honest chain. You can compare your most recent blockhash with the explorer to ensure you are on the honest chain. To ask your node for the latest blockhash, give it the command: getbestblockhash And compare it to the latest block on the BTG Explorer at https://explorer.bitcoingold.org/ ====== EMERGENCY INFORMATION ====== We have just seen an extremely long attack chain of over 1300 blocks on July 10, 2020, against the BTG network which have been mined since July 1, 2020. We detected this illicit activity early on and sent alerts to pools and exchanges to protect them; many closed their wallets over a week ago. We also supplied them with BTG version 0.17.2, which included a checkpoint at block 640650, hash 000000059ec8884fa4fbbdbe46c09cfb4ecba281dfa2351a05084e817c1200ae from July 2 at 2am UTC, mined by MiningPoolHub, a known honest block. With this block checkpointed, the attackers chain could not take over, but this information was not public, and the attacker continued to mine. The attacker mined their secret chain for nearly 10 days, renting power from NiceHash to do so. Today, on July 10, the attacker released over 1300 blocks. Because those attacking blocks are anchored at a block mined on July 1st (before the checkpoint), the honest pools and exchanges who are running the updated code automatically rejected the attackers chain. Its time for everyone else to upgrade their nodes to make sure they stay on the honest chain and to push your node onto the honest chain by using the simple command: invalidateblock 00000000635620f22ba8694aea532d51619f8cd060f4e42e85db3cb3a5d1c29c If you use the Bitcoin Gold GUI, you can enter this command in the Debug Console. If you use the command line daemon, simply give this command to bgold-cli: bgold-cli invalidateblock 00000000635620f22ba8694aea532d51619f8cd060f4e42e85db3cb3a5d1c29c This tells your node that the attackers version of the block at height 640650 invalid, and your node will immediately switch back to the honest version of the chain (perhaps after a short recalculation delay.) The majority of honest pool hashpower continues to mine on the honest chain. |
|
|
|
According to this, ( https://www.vice.com/en_us/article/5dz35q/cryptocurrency-exchange-wash-trading-coinsquare) Coinsquare CEO himself, Cole Diamond ordered his employees to make fake trades to give the impression that their trading exchanges has indeed lots of liquidity and performing and doing good. There is supposedly a leaked emails, Slack messages. According to the material, Coinsquare was "wash trading," which means it was automatically buying and selling currency between accounts it controlled. The news provides evidence of a practice that is often suspected in the cryptocurrency world but rarely proven, and can draw attention from regulators.
"Turn it back on," one seemingly angry March 2019 Slack message from Coinsquare CEO Cole Diamond to other employees of the company read, referring to the code that managed internal trades after an employee switched it off, fearing retaliation from regulators. We all know that this has been practice by low-tier exchanges, but we don't have proof yet. Tried to search this supposedly emails and messages to really see first hand, but so far can't find any. And if this is true then its pretty damning evidence against Coinsquare and we will see how OSC (Ontario Securities Commission) will do, what are the punishments etc. |
|
|
|
Yesterday, for unknown reason, suddenly I feel the urge to gamble again. When the lock down was implemented here, land based casinos are close. I'm more of a physical casino player, however, I was not affected by the closure because I thought that this will just last for a week or two. But yesterday was a different feeling though, their was like a feeling that I need to go to casino and play. Maybe it was just the effect of the boredom during this lock down. There are some mental stimulus, like my sister-in-law inadvertently says that he doesn't have any identification with her but his casino ids. LOL. Anyways, here is what I did to fight this inner demon within me. 1. Do some exercise, good thing about this lock down is that me and my kid age, 14 are doing some calisthenics and body weight exercises. So we did some reps and sets to keep my mind busy. 2. Netflix is your friend during this lock down.  . Watch movies that interest me. 3. I visualize myself totally stopping my gambling even after the lockdown. Yes, this is very tough on me, but I spend hours in my room doing some sort of mental visualization. 4. Talk to families, anything under the sun, bond with them, it is very relaxing. 5. Youtube. Search for inspirational video on how to quit gambling. I don't know if you felt this feeling in this lock down. But for me it is real and I have to fight it back. Do you guys have the same experience? How did you overcome it? Share your experience so that other gamblers will know how to respond. Of course there are a lot of crypto based online game, yes I play online as well, but the land base casino is very different at least in my case. |
|
|
|
|
















 . Watch movies that interest me.
. Watch movies that interest me.