|
jerry0
|
 |
December 28, 2020, 09:39:10 PM |
|
New day brings a new phishing surprise. This time the story is directed and brought to you by our dear Prince Shaon. Prince Shaon didn't put much thought to it so he simple wrote from a gmail account. Ohh, bless him. Our prince suggests we all download his ' additional wallet' so that our accounts don't get hacked. Noble of him indeed. Too bad he signed the email like the Ledger CEO did in the genuine emails that were sent to users. I would have preferred a signature by Prince Shaon instead. Makes me sad looking at it this way   Has anyone here clicked on the link that those scam/spam emails posted and if so, what is it? Is it malware/keylogger or is it something else? Like asking you to type your seed? Could you lose your coins just clicking on those links? Read about chrome extension and how someone got their coins stolen in it... when they used a hardware wallet... but it wasn't ledger or trezor. |
|
|
|
|
|
|
|
|
|
|
|
No Gods or Kings. Only Bitcoin
|
|
|
Advertised sites are not endorsed by the Bitcoin Forum. They may be unsafe, untrustworthy, or illegal in your jurisdiction.
|
HCP
Legendary

 Offline Offline
Activity: 2086
Merit: 4316
<insert witty quote here>

|
 |
December 28, 2020, 09:54:36 PM |
|
Has anyone here clicked on the link that those scam/spam emails posted and if so, what is it? Is it malware/keylogger or is it something else? Like asking you to type your seed? Could you lose your coins just clicking on those links? Read about chrome extension and how someone got their coins stolen in it... when they used a hardware wallet... but it wasn't ledger or trezor.
You can't lose your coins from a Ledger (or other hardware wallets) simply by clicking on a link... That is the entire purpose of hardware wallets. You would need to have the device connected and explicitly authorise a transaction on the device itself to send a transaction, and the private keys/seeds are shielded from external applications. The simple answer is that it doesn't matter what the link goes to (be it a fake version of Ledger Live, keylogger or a website asking for your 24 words), you simply should NOT click on it... it's obviously fake and a poor attempt to try and steal your coins. |
|
|
|
|
jerry0
|
 |
December 28, 2020, 10:12:51 PM |
|
Has anyone here clicked on the link that those scam/spam emails posted and if so, what is it? Is it malware/keylogger or is it something else? Like asking you to type your seed? Could you lose your coins just clicking on those links? Read about chrome extension and how someone got their coins stolen in it... when they used a hardware wallet... but it wasn't ledger or trezor.
You can't lose your coins from a Ledger (or other hardware wallets) simply by clicking on a link... That is the entire purpose of hardware wallets. You would need to have the device connected and explicitly authorise a transaction on the device itself to send a transaction, and the private keys/seeds are shielded from external applications. The simple answer is that it doesn't matter what the link goes to (be it a fake version of Ledger Live, keylogger or a website asking for your 24 words), you simply should NOT click on it... it's obviously fake and a poor attempt to try and steal your coins. I saw this post on someone using a hardware wallet called keepkey and used a malicious chrome extension through google... So what happened here then? This person typed in his keepkey seed? Again i don't know of any hardware wallets besides nano ledger and trezor... but this guy mentioned he used a hardware wallet. https://bitcointalk.org/index.php?topic=5255282.0;allYea obviously you should not click on whatever link is in the email. But i got to assume it has to be malware/keylogger at least right? I can't imagine a hacker putting a link and you only get screwed if you actually type in your seed. I mean... wouldn't they make it malware/keylogger as well so then they can get into your email or say keepass/lastpass and thus they find your seed somewhere there?
Also i assume the safe way to find out if a link has malware/keylogger or any malicious would be use a separate computer that uses linux or chromebook then? Or even if you use a windows computer, make sure its like a throwaway computer or a testing computer so to speak... to see what it is? I recall i saw some youtube video where a guy intentionally click on malware/virus/keylogger links to see what it did to their computer... and they used a virtual machine for that.
So someone installing a virtual machine or using linux/chromebook could possibly test this all out without risk to their main computer? But would there be any danger to their internet though? |
|
|
|
|
|
aesma
|
 |
December 28, 2020, 10:55:11 PM |
|
He says it was a phishing app. So basically what some of these Ledger emails are trying to do : have you install a fake app, then use it as normal. As soon as you authorize a transfer of your coins, the app will take over and have you send to their address, and send everything instead of just the amount you had chosen.
With a Ledger though, you should still be able to see what's happening on the Ledger screen and not authorize it.
|
|
|
|
|
Pmalek (OP)
Legendary

 Offline Offline
Activity: 2758
Merit: 7132

|
 |
December 28, 2020, 11:02:54 PM |
|
So what happened here then? This person typed in his keepkey seed? He downloaded a fake Chrome extension that asked him to enter his recovery phrase (for whatever reason). He did, the words were sent to the scammers who ultimately emptied his accounts. This is not a hack of a hardware wallet. This was an avoidable human error and a person who fell for a phishing attempt. Your seed phrase should never be stored or entered anywhere online. If you remember that simple rule, you will save yourself plenty of trouble. Yea obviously you should not click on whatever link is in the email. But i got to assume it has to be malware/keylogger at least right? No, the hackers are interested in your recovery phrase. Infecting you with a keylogger wont help them gain access to the crypto assets stored on your hardware device. They want you to enter your seed in their malicious app.
Why are you so concerned about what it is? It is not a genuine app, and it could potentially do you some harm in one way or the other. If you find a needle on the ground, you don't stick it into your arm to see what it is. Just pass by it or throw it away. |
.
.BLACKJACK ♠ FUN. | | | ███▄██████
██████████████▀
████████████
█████████████████
████████████████▄▄
░█████████████▀░▀▀
██████████████████
░██████████████
█████████████████▄
░██████████████▀
████████████
███████████████░██
██████████ | | CRYPTO CASINO &
SPORTS BETTING | | │ | | │ | ▄▄███████▄▄
▄███████████████▄
███████████████████
█████████████████████
███████████████████████
█████████████████████████
█████████████████████████
█████████████████████████
███████████████████████
█████████████████████
███████████████████
▀███████████████▀
███████████████████ | | .
|
|
|
|
HCP
Legendary

 Offline Offline
Activity: 2086
Merit: 4316
<insert witty quote here>

|
 |
December 28, 2020, 11:09:38 PM |
|
I saw this post on someone using a hardware wallet called keepkey and used a malicious chrome extension through google...
So what happened here then? This person typed in his keepkey seed? Again i don't know of any hardware wallets besides nano ledger and trezor... but this guy mentioned he used a hardware wallet.
Exactly, if you read the various details of that story (and any other involving loss from hardware wallets), it's generally because the seed has been compromised by either: - some fake piece of software that asks the user to enter their seed on the PC... boom! coins gone. or - user stored their seed in a screenshot, email, instant messenger, text document, other digital format etc. and it got compromised. Yea obviously you should not click on whatever link is in the email. But i got to assume it has to be malware/keylogger at least right? I can't imagine a hacker putting a link and you only get screwed if you actually type in your seed. I mean... wouldn't they make it malware/keylogger as well so then they can get into your email or say keepass/lastpass and thus they find your seed somewhere there?
Which do you think is easier and quicker to make (and more likely to success)?  A website that says "hey this is Ledger website, please confirm your 24 word ledger seed here:" and harvests 24 word seeds... or create an installer for malware that goes targeting keepass/lastpass databases on the off chance the victim actually has those installed, and they actually stored their seed there (against all common sense and recommendations of NOT storing your seed digitally)?  Also i assume the safe way to find out if a link has malware/keylogger or any malicious would be use a separate computer that uses linux or chromebook then? Or even if you use a windows computer, make sure its like a throwaway computer or a testing computer so to speak... to see what it is? I recall i saw some youtube video where a guy intentionally click on malware/virus/keylogger links to see what it did to their computer... and they used a virtual machine for that.
So someone installing a virtual machine or using linux/chromebook could possibly test this all out without risk to their main computer? But would there be any danger to their internet though?
Why does it even matter??!?   Just DON'T click on the link... who cares if it's just a website asking for your 24 word seed or malware disguised as wallet software... there is literally ZERO reason (for normal users) to click on the link. Seriously, just delete the emails and move on with your life. |
|
|
|
bob123
Legendary

 Offline Offline
Activity: 1624
Merit: 2481


|
 |
December 29, 2020, 09:46:53 AM |
|
Yea obviously you should not click on whatever link is in the email. But i got to assume it has to be malware/keylogger at least right? I can't imagine a hacker putting a link and you only get screwed if you actually type in your seed. I mean... wouldn't they make it malware/keylogger as well so then they can get into your email or say keepass/lastpass and thus they find your seed somewhere there?
Which do you think is easier and quicker to make (and more likely to success)?  A website that says "hey this is Ledger website, please confirm your 24 word ledger seed here:" and harvests 24 word seeds... or create an installer for malware that goes targeting keepass/lastpass databases on the off chance the victim actually has those installed, and they actually stored their seed there (against all common sense and recommendations of NOT storing your seed digitally)?  To be honestly, both is pretty easy to accomplish. The website obviously is a no-brainer. But the other method wouldn't require too much work either. You wouldn't create a malware which specifically targets the password manager. You would use some generic malware which gives you full access to the victims system. Then you could always load other pieces of malware to search/extract specific kind of information. But the consensus is: Don't click on unknown links. And if you did and it downloaded something, delete it and do not execute or open the file. |
|
|
|
LTU_btc
Legendary

 Offline Offline
Activity: 3052
Merit: 1330
Slava Ukraini!


|
 |
December 30, 2020, 11:06:22 PM
Last edit: September 10, 2023, 10:11:37 PM by LTU_btc |
|
Through all these phishing emails in my spam folder, today I found something new  : 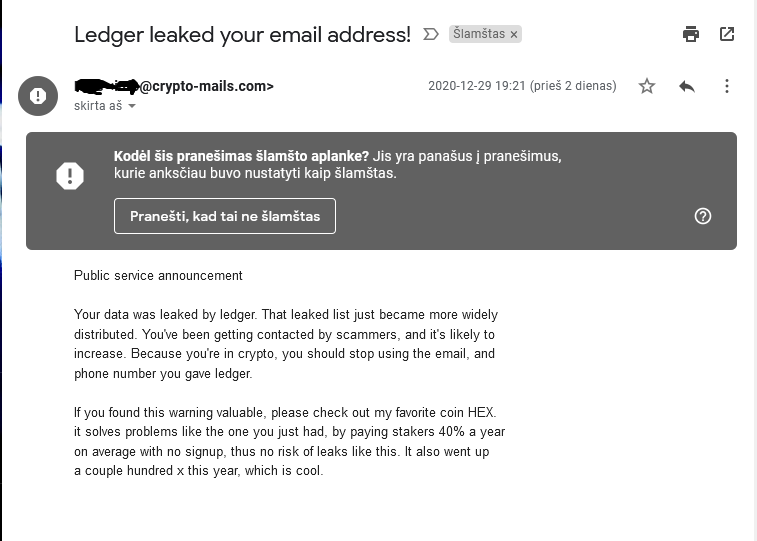 Never heard about website Crypto-mails.com before and I can't even access it. |
|
|
|
Lucius
Legendary

 Offline Offline
Activity: 3234
Merit: 5637
Blackjack.fun-Free Raffle-Join&Win $50🎲


|
 |
December 31, 2020, 11:42:03 AM |
|
LTU_btc, that mail is nothing but the promotion of the coin/token mentioned in it, and it is quite expected that the database will be used for such purposes. Since the database became public, the amount of spam in my case has increased at least 4 to 5 times, but thanks to a good spam filter everything ends up in a spam folder, including legitimate emails from Ledger which are obviously marked by many as spam.
Someone has already mentioned that it is not the smartest thing to open such spam e-mails at all, because it is possible that those who send them use some methods to get your IP and some other information. In other words, you are letting the bad guys know that you are active and that it makes sense to keep trying to deceive you in some way.
|
.
.BLACKJACK ♠ FUN. | | | ███▄██████
██████████████▀
████████████
█████████████████
████████████████▄▄
░█████████████▀░▀▀
██████████████████
░██████████████
█████████████████▄
░██████████████▀
████████████
███████████████░██
██████████ | | CRYPTO CASINO &
SPORTS BETTING | | │ | | │ | ▄▄███████▄▄
▄███████████████▄
███████████████████
█████████████████████
███████████████████████
█████████████████████████
█████████████████████████
█████████████████████████
███████████████████████
█████████████████████
███████████████████
▀███████████████▀
███████████████████ | | .
|
|
|
|
The Sceptical Chymist
Legendary

 Offline Offline
Activity: 3332
Merit: 6826
Cashback 15%

|
 |
December 31, 2020, 11:49:44 AM |
|
I stand myself corrected; they sent a second email that did go straight to the spam folder;
For a long time I thought I wasn't getting these phishing e-mails, but I happened to check the spam folder of the e-mail address that I gave Ledger (which is not my primary one by any means), and yep, I've been getting them alright. Luckily they did go to the spam folder immediately, and I hope that's true for most people. Strangely (or not) I've gotten quite a few legitimate e-mails from the Ledger team that haven't gone to the spam folder. I haven't been paying attention to them either, or that e-mail address in general. Meanwhile, I don't have anything on either Ledger I own--not that I'm afraid of getting hacked, just that I don't own a lot of crypto these days. Never heard about website Crypto-mails.com before and I can't even access it.
Nor have I and I wouldn't even try to access it. Is it possible to own a domain name that doesn't have a website, just e-mail hosting? |
.
.HUGE. | | | | | | █▀▀▀▀
█
█
█
█
█
█
█
█
█
█
█
█▄▄▄▄ | ▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀
.
CASINO & SPORTSBOOK
▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄ | ▀▀▀▀█
█
█
█
█
█
█
█
█
█
█
█
▄▄▄▄█ | | |
|
|
|
LTU_btc
Legendary

 Offline Offline
Activity: 3052
Merit: 1330
Slava Ukraini!


|
 |
December 31, 2020, 02:36:09 PM |
|
Someone has already mentioned that it is not the smartest thing to open such spam e-mails at all, because it is possible that those who send them use some methods to get your IP and some other information. In other words, you are letting the bad guys know that you are active and that it makes sense to keep trying to deceive you in some way.
Is it really possible for them to know IP address when you just open email without clicking any links? Because I've never hear about such thing before. If it's really possible, then probably it's not good idea to open these emails. Is it possible to own a domain name that doesn't have a website, just e-mail hosting? [/quote] Yeah, it's possible. |
|
|
|
Stalker22
Legendary

 Offline Offline
Activity: 1498
Merit: 1358

|
 |
December 31, 2020, 03:37:30 PM |
|
Is it really possible for them to know IP address when you just open email without clicking any links? Because I've never hear about such thing before. If it's really possible, then probably it's not good idea to open these emails.
Yeah, it's possible. It's called Pixel-Tracking. In addition to the IP address, they can also know when you opened the email, how many times, the operating system you use, the email client, the device, and a bunch of other things about you. The easiest way to prevent pixel tracking is to block images from being displayed in your emails, but I'm not sure if it's totally effective. |
|
|
|
Lucius
Legendary

 Offline Offline
Activity: 3234
Merit: 5637
Blackjack.fun-Free Raffle-Join&Win $50🎲


|
 |
January 01, 2021, 11:13:03 AM |
|
LTU_btc, of course it is possible, with the method described by Stalker22, and there are probably some other tricks used for this purpose. While this may not mean too much for those to whom all data has become public, for those to whom only email addresses have become available it would certainly be a breach of privacy - the address can be linked to the country, and if the ISP does not have adequate protection even locate the user.
After all, all these phishing/advertising emails are more or less the same - when you see one, there is no need to look at the others.
|
.
.BLACKJACK ♠ FUN. | | | ███▄██████
██████████████▀
████████████
█████████████████
████████████████▄▄
░█████████████▀░▀▀
██████████████████
░██████████████
█████████████████▄
░██████████████▀
████████████
███████████████░██
██████████ | | CRYPTO CASINO &
SPORTS BETTING | | │ | | │ | ▄▄███████▄▄
▄███████████████▄
███████████████████
█████████████████████
███████████████████████
█████████████████████████
█████████████████████████
█████████████████████████
███████████████████████
█████████████████████
███████████████████
▀███████████████▀
███████████████████ | | .
|
|
|
|
Pmalek (OP)
Legendary

 Offline Offline
Activity: 2758
Merit: 7132

|
 |
January 01, 2021, 02:56:31 PM |
|
Yeah, it's possible. It's called Pixel-Tracking. The good thing about Pixel-Tracking is that you can probably prevent it from getting to your private data by going into the settings of your email client and turning of the option for showing images from the email. And if the mail ends up in your spam folder, I think clients like Hotmail and Yahoo disable the option to display external images by default. I have read about Pixel-Tracking extensions and add-ons as well, but never tested any personally. |
.
.BLACKJACK ♠ FUN. | | | ███▄██████
██████████████▀
████████████
█████████████████
████████████████▄▄
░█████████████▀░▀▀
██████████████████
░██████████████
█████████████████▄
░██████████████▀
████████████
███████████████░██
██████████ | | CRYPTO CASINO &
SPORTS BETTING | | │ | | │ | ▄▄███████▄▄
▄███████████████▄
███████████████████
█████████████████████
███████████████████████
█████████████████████████
█████████████████████████
█████████████████████████
███████████████████████
█████████████████████
███████████████████
▀███████████████▀
███████████████████ | | .
|
|
|
|
Stalker22
Legendary

 Offline Offline
Activity: 1498
Merit: 1358

|
Yeah, it's possible. It's called Pixel-Tracking. The good thing about Pixel-Tracking is that you can probably prevent it from getting to your private data by going into the settings of your email client and turning of the option for showing images from the email. And if the mail ends up in your spam folder, I think clients like Hotmail and Yahoo disable the option to display external images by default. I have read about Pixel-Tracking extensions and add-ons as well, but never tested any personally. Gmail users are also somewhat protected: Google redirects every image request via its own proxy servers (much like bitcointalk does). Tracking pixels will still know when you read their emails, but they can't sniff your location because they can't see your IP address (they see Google's IP instead). Of course, this doesn't mean I'm in favor of Gmail in terms of privacy.  |
|
|
|
LTU_btc
Legendary

 Offline Offline
Activity: 3052
Merit: 1330
Slava Ukraini!


|
 |
January 02, 2021, 12:05:51 AM |
|
Thanks guys for explaining me. I remember that maybe 10 years I was wondering why images in emails is disabled by default. I didn't understood how it can be privacy issue. So, now it's good to finally know exact answer why it can be dangerous.
@Pmalek, it's not just Hotmail or Yahoo, but also Gmail and probably all others more or less popular email providers by default have disabled images in spam folder.
|
|
|
|
Pmalek (OP)
Legendary

 Offline Offline
Activity: 2758
Merit: 7132

|
 |
January 14, 2021, 05:57:44 PM
Last edit: November 12, 2023, 10:04:39 AM by Pmalek |
|
My friend just sent me the new email he received. I am laughing about it, but I can understand how some people might find this frightening. The email begins by stating his name, address and phone number. The image below shows the beautifully crafted content that comes after. For some reason I can't copy/paste the email here. The pasted content becomes some gibberish. Pasting it into Word and changing the font doesn't work either. 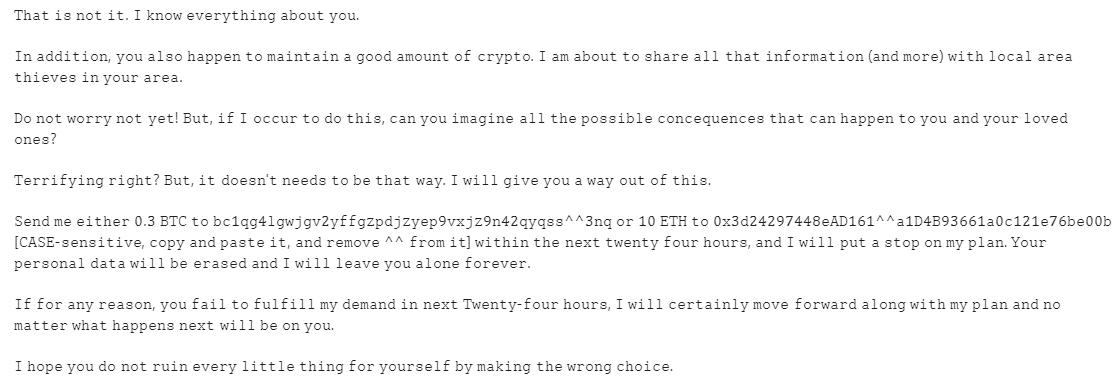 What is not it? How do you know how much crypto I have. You should have included my addresses to be more convincing. Does anyone know what kind of font/formatting this is and why can't it be copy-pasted in a post on Bitcointalk? I tried to look up those addresses on a block explorer, but they either don't exist or whatever font/formatting/encoding he used messed it all up. Neither of the two addresses can be copy/pasted into a block explorer after removing the special characters. |
.
.BLACKJACK ♠ FUN. | | | ███▄██████
██████████████▀
████████████
█████████████████
████████████████▄▄
░█████████████▀░▀▀
██████████████████
░██████████████
█████████████████▄
░██████████████▀
████████████
███████████████░██
██████████ | | CRYPTO CASINO &
SPORTS BETTING | | │ | | │ | ▄▄███████▄▄
▄███████████████▄
███████████████████
█████████████████████
███████████████████████
█████████████████████████
█████████████████████████
█████████████████████████
███████████████████████
█████████████████████
███████████████████
▀███████████████▀
███████████████████ | | .
|
|
|
|
FatFork
Legendary

 Offline Offline
Activity: 1596
Merit: 2588
Top Crypto Casino


|
 |
January 14, 2021, 07:46:38 PM |
|
Does anyone know what kind of font/formatting this is and why can't it be copy-pasted in a post on Bitcointalk?
I tried to look up those addresses on a block explorer, but they either don't exist or whatever font/formatting/encoding he used messed it all up. Neither of the two addresses can be copy/pasted into a block explorer after removing the special characters.
It is difficult (if not impossible) to determine the encoding based only on a screenshot. Have you tried copy/paste on pastebin or put in [ code ] tags? |
|
|
|
Pmalek (OP)
Legendary

 Offline Offline
Activity: 2758
Merit: 7132

|
 |
January 15, 2021, 01:32:29 PM
Last edit: November 12, 2023, 10:04:33 AM by Pmalek |
|
I have tried both. The message can be pasted on pastebin, but if you try to copy it from there to paste on the forum, it doesn't work. I have put the addresses in quote and code tags. Take a look. It stays completely blank. ððð·ðððºððð ðððð¸ð¢ðððð£ðððð£ð¢ððð¿ðð¡ðð£ð¿ððºð¸ðð¢ðððð¹ðð ððð·ðððºððð ðððð¸ð¢ðððð£ðððð£ð¢ððð¿ðð¡ðð£ð¿ððºð¸ðð¢ðððð¹ðð And here is how it looks when you copy/paste the message in a post: ðððð ðð ððð ðð. ð¸ ðððð ððððð¢ððððð ððððð ð¢ðð.
ð¸ð ðððððððð, ð¢ðð ðððð ðððððð ðð ðððððððð ð ðððð ðððððð ðð ððð¢ððð. ð¸ ðð ððððð ðð ððððð ððð ðððð ððððððððððð (ððð ðððð) ð ððð ððððð ðððð ððððððð ðð ð¢ððð ðððð.
ð³ð ððð ð ðððð¢ ððð ð¢ðð! ð±ðð, ðð ð¸ ððððð ðð ðð ðððð, ððð ð¢ðð ððððððð ððð ððð ðððððððð ðððððððððððð ðððð ððð ðððððð ðð ð¢ðð ððð ð¢ððð ððððð ðððð?
ððððððð¢ððð ððððð? ð±ðð, ðð ððððð'ð ððððð ðð ðð ðððð ð ðð¢. ð¸ ð ððð ðððð ð¢ðð ð ð ðð¢ ððð ðð ðððð.
ðððð ðð ðððððð ð¶.ð¹ ð±ðð² ðð ððð·ðððºððð ðððð¸ð¢ðððð£ðððð£ð¢ððð¿ðð¡ðð£ð¿ððºð¸ðð¢ððð^^ð¹ðð ðð ð·ð¶ ð´ðð· ðð ð¶ð¡ð¹ðð¸ðºð¸ð¿ð½ðºðºð¾ðð°ð³ð·ð¼ð·^^ðð·ð³ðºð±ð¿ð¹ð¼ð¼ð·ðð¶ðð·ð¸ð·ðð½ð¼ððð¶ð¶ð [ð²ð°ðð´-ððððððððð, ðððð¢ ððð ððððð ðð, ððð ðððððð ^^ ðððð ðð] ð ððððð ððð ððð¡ð ðð ðððð¢ ðððð ððððð, ððð ð¸ ð ððð ððð ð ðððð ðð ðð¢ ðððð. ðððð ðððððððð ðððð ð ððð ðð ðððððð ððð ð¸ ð ððð ððððð ð¢ðð ððððð ððððððð.
ð¸ð ððð ððð¢ ðððððð, ð¢ðð ðððð ðð ððððððð ðð¢ ðððððð ðð ððð¡ð ðð ðððð¢-ðððð ððððð, ð¸ ð ððð ððððððððð¢ ðððð ðððð ððð ððððð ð ððð ðð¢ ðððð ððð ðð ðððððð ð ððð ððððððð ððð¡ð ð ððð ðð ðð ð¢ðð.
ð¸ ðððð ð¢ðð ðð ððð ðððð ððððð¢ ðððððð ððððð ððð ð¢ððððððð ðð¢ ðððððð ððð ð ðððð ðððððð.
Edit: Wow, that's freaky. The message actually displays just fine. But clicking on the preview button doesn't work. This is what I get when previewing the message before posting it.  |
.
.BLACKJACK ♠ FUN. | | | ███▄██████
██████████████▀
████████████
█████████████████
████████████████▄▄
░█████████████▀░▀▀
██████████████████
░██████████████
█████████████████▄
░██████████████▀
████████████
███████████████░██
██████████ | | CRYPTO CASINO &
SPORTS BETTING | | │ | | │ | ▄▄███████▄▄
▄███████████████▄
███████████████████
█████████████████████
███████████████████████
█████████████████████████
█████████████████████████
█████████████████████████
███████████████████████
█████████████████████
███████████████████
▀███████████████▀
███████████████████ | | .
|
|
|
|
o_e_l_e_o
In memoriam
Legendary

 Offline Offline
Activity: 2268
Merit: 18510

|
 |
January 15, 2021, 01:50:44 PM |
|
Those characters are unicode, which is why they don't show up in preview. The same is true of any unicode, such as custom emojis like this one - 😀
|
|
|
|
|
|



