jonald_fyookball
Legendary

 Offline Offline
Activity: 1302
Merit: 1004
Core dev leaves me neg feedback #abuse #political

|
 |
March 10, 2014, 08:57:37 PM |
|
i think we all agree, best case scenario, we are decades away from even being close
to crack 128 bit security, and by then , bitcoin could be updated... so its completely
unfeasible to steal Satoshi's stash with supercomputers using brute force.
|
|
|
|
|
|
|
|
|
"I'm sure that in 20 years there will either be very large transaction volume or no volume." -- Satoshi
|
|
|
Advertised sites are not endorsed by the Bitcoin Forum. They may be unsafe, untrustworthy, or illegal in your jurisdiction.
|
|
|
|
|
|
|
|
kuroman
|
 |
March 10, 2014, 09:03:16 PM |
|
i think we all agree, best case scenario, we are decades away from even being close
to crack 128 bit security, and by then , bitcoin could be updated... so its completely
unfeasible to steal Satoshi's stash with supercomputers using brute force.
You resume the situation perfectly, unless there is a major flaw or a NSA backdoor and co in the encryption protocol, but that's another story I guess. |
|
|
|
|
jonald_fyookball
Legendary

 Offline Offline
Activity: 1302
Merit: 1004
Core dev leaves me neg feedback #abuse #political

|
 |
March 10, 2014, 09:08:42 PM |
|
|
|
|
|
GreekBitcoin
Legendary

 Offline Offline
Activity: 1428
Merit: 1001
getmonero.org


|
 |
March 10, 2014, 09:19:01 PM |
|
kuroman, Moore's law will not go on much longer the way it has been advancing by smaller hardware. by ~2020 you reach the point where moore's law requires a transistor the size of an atom. (eg http://www.pcworld.com/article/2032913/the-end-of-moores-law-is-on-the-horizon-says-amd.html) There could a major break through elsewhere, but it would be a coincidence if that happens to match with Moore's. Anything is this area is wild speculation and will probably not get us anywhere. Actually I've already answered this question, there are many ways to extend the moors law, such as 3D transistors and nanomaterials breaktrough such as Graphen and these aren't vaporware, they already exist, it's just that the manufacturing process needs to be generalised and it will not happen till we start hitting Silicon/Copper limits (as it will require to review the whole fab industry from technics to equipement which requires $$$$) http://e2e.ti.com/blogs_/b/thinkinnovate/archive/2013/03/01/graphene-s-potential-to-extend-moore-s-law.aspxhttp://phys.org/news/2014-02-team-aims-graphene-nanoribbon-wires.htmlEventually we will reach the point of quantum mechanics interference, and where the lasers won't be able to keep up, but by that time which is at least a couple of decades ahead of us Quantum computer would operational, todays Quantum computer are still far from it jesus m8. you dont get the point.... it has nothing to do with computers. it has to do with physics limitations. you need energy to calculate whatever and even if you had a 100% efficient computer you would need more energy than the sun will give in its lifetime... |
|
|
|
|
|
kuroman
|
 |
March 10, 2014, 10:07:06 PM
Last edit: March 10, 2014, 11:48:05 PM by kuroman |
|
kuroman, Moore's law will not go on much longer the way it has been advancing by smaller hardware. by ~2020 you reach the point where moore's law requires a transistor the size of an atom. (eg http://www.pcworld.com/article/2032913/the-end-of-moores-law-is-on-the-horizon-says-amd.html) There could a major break through elsewhere, but it would be a coincidence if that happens to match with Moore's. Anything is this area is wild speculation and will probably not get us anywhere. Actually I've already answered this question, there are many ways to extend the moors law, such as 3D transistors and nanomaterials breaktrough such as Graphen and these aren't vaporware, they already exist, it's just that the manufacturing process needs to be generalised and it will not happen till we start hitting Silicon/Copper limits (as it will require to review the whole fab industry from technics to equipement which requires $$$$) http://e2e.ti.com/blogs_/b/thinkinnovate/archive/2013/03/01/graphene-s-potential-to-extend-moore-s-law.aspxhttp://phys.org/news/2014-02-team-aims-graphene-nanoribbon-wires.htmlEventually we will reach the point of quantum mechanics interference, and where the lasers won't be able to keep up, but by that time which is at least a couple of decades ahead of us Quantum computer would operational, todays Quantum computer are still far from it jesus m8. you dont get the point.... it has nothing to do with computers. it has to do with physics limitations. you need energy to calculate whatever and even if you had a 100% efficient computer you would need more energy than the sun will give in its lifetime... Jesus m8, you need to read previous comments, point that was previously discussed, if you have a counter argument even if I stated facts and not speculations please feel free to lay it down instead of repeating what you are told or heard without a minimum of thinking. |
|
|
|
|
Remember remember the 5th of November
Legendary

 Offline Offline
Activity: 1862
Merit: 1011
Reverse engineer from time to time

|
 |
March 10, 2014, 10:07:50 PM |
|
I am curious, this doesn't mean I will understand even one word from that paper there. A bit too advanced for me. |
BTC:1AiCRMxgf1ptVQwx6hDuKMu4f7F27QmJC2
|
|
|
jonald_fyookball
Legendary

 Offline Offline
Activity: 1302
Merit: 1004
Core dev leaves me neg feedback #abuse #political

|
 |
March 10, 2014, 10:08:45 PM |
|
if the network hashrate is 30,000,000 Gh/S,
isn't that 30 million billion hashes per second? would be the
same as enough computing power to try 30 million billion private
keys per second?
At that rate, it would only take the entire network 359,676 years,
not the billions of years said...
|
|
|
|
|
lnternet
|
 |
March 10, 2014, 10:13:50 PM |
|
if the network hashrate is 30,000,000 Gh/S,
isn't that 30 million billion hashes per second? would be the
same as enough computing power to try 30 million billion private
keys per second?
YES
At that rate, it would only take the entire network 359,676 years,
not the billions of years said...
NO
30e15 per second
9.5e23 per year
2^256 ~ 1e77
so makes about 1e54 years
|
1ntemetqbXokPSSkuHH4iuAJRTQMP6uJ9
|
|
|
DeathAndTaxes
Donator
Legendary

 Offline Offline
Activity: 1218
Merit: 1079
Gerald Davis

|
 |
March 10, 2014, 10:15:20 PM
Last edit: March 10, 2014, 11:03:07 PM by DeathAndTaxes |
|
if the network hashrate is 30,000,000 Gh/S,
isn't that 30 million billion hashes per second? would be the
same as enough computing power to try 30 million billion private
keys per second?
At that rate, it would only take the entire network 359,676 years,
not the billions of years said...
Good logic, but you have a math error I believe. The network is 30 PH/s which is 30*10^15. Simple trick is to just count the metric prefixes (each one is a factor of 1000). So kilohash, megahash, gigahash, terrahash, petahash is 1,2,3,4,5 so 1000^5. The time required with the assumptions you have would be 359,676,102,360,200 years. If we assume a network one trillion times more powerful it would still be 360 years. However even that is unlikely. A couple points to consider: 1) The network can't do anything but compute hashes but if we assume it could be repurposed to brute force EDSA keys it would take more computing cycles to perform one ECC attempt than it does to perform one SHA-2 hash. It would be something on the order of 80x as long (although that is some crude estimate on my hardware). So 30 PH/s wouldn't be 30 PK/s but maybe 1 PK/s (peta keys attempted per second) but his is minor compared to #2 below. 2) The security of ECDSA is 128 bit if the PubKey is known. If it the PubKey is unknown the only fastest attack is to attempt a preimage of the PubKeyHash. That has a complexity of 2^160 which is 2^32 larger or ~ 4 billion. Even if you could break a known PubKey in one year it would take 4 billion years to break the hash of an unknown pubkey. Keys with 128 bit security are infeasible to break by brute force using classical computing. However this doesn't mean that they can't be broken by cryptanalysis or quantum computing (which "go around" the problem rather than try to beat it by the pure expenditure of computing power). |
|
|
|
|
|
E.exchanger
|
 |
March 10, 2014, 10:42:40 PM |
|
You definitely be kidding wait you are not  then what makes you think anyone will bruteforce the keys or maybe someone will for his 10th generation to enjoy the money makes real sense   |
|
|
|
|
jonald_fyookball
Legendary

 Offline Offline
Activity: 1302
Merit: 1004
Core dev leaves me neg feedback #abuse #political

|
 |
March 10, 2014, 11:00:13 PM |
|
Good logic, but you have a math error I believe.
oops, yeah i mistook a comma for a period on my calculator. Yes, its 359,676,102,360,200 years with today's entire bitcoin network trying to crack one private key, and that's assuming the network could try a key at the same rate it can try a hash, and also assuming the public key is known.  Brute force, definitely out even with all the fancy lasers and vapors and hexagonal layer thingies. What about breaking the encryption itself... this is a whole new conversation ...how close do you think anyone is to cracking SHA-256 ? FYI, here's a javascript implementation of SHA-256. its more clear than the white paper version if you can read a bit of code. Not suggesting read every line, but you see the overall complexity. http://www.movable-type.co.uk/scripts/sha256.html
|
|
|
|
|
vinipoars
|
 |
March 10, 2014, 11:14:27 PM |
|
Shortcut: solve P = NP and get all the bitcoins you want.  |
|
|
|
|
|
kuroman
|
 |
March 10, 2014, 11:51:56 PM |
|
Shortcut: solve P = NP and get all the bitcoins you want.  well yeah the question in billions of dollars, although I have an idea, but the problem needs to be transformed into a matricial problem or at least Vectorial one, then you can relatively easly solve P = NP with Matrix triangulation or diagonalisation if that works but again meh lol |
|
|
|
|
BADecker
Legendary

 Offline Offline
Activity: 3780
Merit: 1372

|
 |
March 11, 2014, 01:35:31 AM |
|
Hello!
This is just for educational purposes. We know that Satoshi has an enormous amount of bitcoins and that he has not moved them for a long time. I think we also know the bitcoin addresses containing those bitcoins.
What if someone wanted to steal those bitcoins? They would need both the public key and private key of the address. I know that it would take an enormous amount of time but is this technically doable?
Also, would mining pools be able to push to their clients a script to find those public and private keys? These pools have nowadays an enormous calculation power.
The odds are almost infinitely better playing the lottery. But if you can do it, be sure to give them back, so that you can live with yourself.  |
|
|
|
|
Joshuar
|
 |
March 11, 2014, 01:38:40 AM |
|
The easiest way would be to pretend to be Satoshis long lost brother and ask him for a couple quick millions. Should be as simple as that.  |
| ❱❱ | | ██
█║█
║║║
║║║
█║█
██ | | | | |
▄██▄
▄██████▄
▄██████████
▄██████████▀ ▄▄
▄██████████▀ ▄████▄
▄██████████▀ ████████▄
██████████▀ ▀████████
▀███████▀ ▄███▄ ▀████▀ ▄█▄
▄███▄ ▀███▀ ▄███████▄ ▀▀ ▄█████▄
▄███████▄ ▄██████████ ▄█████████
█████████ ▄██████████▀ ▄██████████▀
▀█████▀ ▄██████████▀ ▄██████████▀
▀▀▀ ▄██████████▀ ▄██████████▀
██████████▀ ▄██████████▀
▀███████▀ █████████▀
▀███▀ ▄██▄ ▀█████▀
▄██████▄ ▀▀▀
█████████
▀█████▀
▀▀▀ | | e i d o o
██
| |
▄██▄
▄██████▄
▄██████████
▄██████████▀ ▄▄
▄██████████▀ ▄████▄
▄██████████▀ ████████▄
██████████▀ ▀████████
▀███████▀ ▄███▄ ▀████▀ ▄█▄
▄███▄ ▀███▀ ▄███████▄ ▀▀ ▄█████▄
▄███████▄ ▄██████████ ▄█████████
█████████ ▄██████████▀ ▄██████████▀
▀█████▀ ▄██████████▀ ▄██████████▀
▀▀▀ ▄██████████▀ ▄██████████▀
██████████▀ ▄██████████▀
▀███████▀ █████████▀
▀███▀ ▄██▄ ▀█████▀
▄██████▄ ▀▀▀
█████████
▀█████▀
▀▀▀ | | | | | ██
█║█
║║║
║║║
█║█
██ | | ❰❰ | | |
|
|
|
surfer43
Sr. Member
   
 Offline Offline
Activity: 560
Merit: 250
"Trading Platform of The Future!"

|
 |
March 11, 2014, 02:28:53 AM |
|
[insert infographic here]
Yup. Until we colonize the universe. 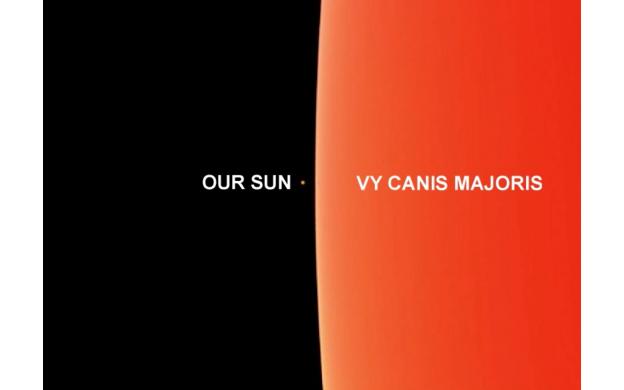 |
|
|
|
|
|
Klestin
|
 |
March 11, 2014, 02:52:58 AM |
|
Wake me up when someone factors 32 bit number using quantum computing. If QC becomes a credible threat Bitcoin can evolve to addresses which use post-quantum cryptography. You. You bring your logic. And your facts. And your basic understanding of cryptography, computing, and the current state of quantum computing development. Did you stop to consider that you were derailing this community's gnashing of teeth over the suuper scaaarey magical quantum computer that's gunna steal all our coins? I'm pretty sure some folks were all ready to set their hair on fire and run around screaming. *Shakes tiny fist* To allay their dismay at the loss of a good panic,  |
|
|
|
|
|
wickedgoodtrader
|
 |
March 11, 2014, 03:01:41 AM |
|
This will just be another thing bitcoin flops on. It's already happened a few times. Everyone says bitcoin is rock solid bullet proof then the next thing ya know the chain is forked and shit is going to hell!
Then transactions are being reversed from gambling sites because a pool has too high % of the network.
Then transactions are being altered so people can rob exchanges all over the place!
Before ya know it there will be some shit with the SHA too. This whole it takes more energy to crack it then exists in the universe or whatever the fuck they are trying to say just ain't gonna fly. I bet Karpales made that picture.
|
|
|
|
|
Syke
Legendary

 Offline Offline
Activity: 3878
Merit: 1193

|
 |
March 11, 2014, 03:04:11 AM |
|
Wait what? did you even read beyond that point? you are partially quoting to prove that you are right is that what you trying to do here? I repeat my self todays computing power 10^15+ so theoritically if classical computing keeps going forward at the same pace it's advanced with since the 60s we will be looking at 10^30 10^40 Flops in the next decade or two which is enough to crack 128bits in a few seconds and we will move on to 10^70 Flops and beyond in another decade or two from there, that is without taking into consideration anything else! which not even remotly true
Obligitory XKCD:  |
Buy & Hold
|
|
|
|
fasmax
|
 |
March 11, 2014, 03:17:15 AM |
|
Is it possible that a backdoor key exists? If a backdoor exists then you could simply compute the private key given the public key and the backdoor key.  |
|
|
|
|
|



