|
botolo86 (OP)
|
 |
March 10, 2014, 03:44:36 AM |
|
Hello!
This is just for educational purposes. We know that Satoshi has an enormous amount of bitcoins and that he has not moved them for a long time. I think we also know the bitcoin addresses containing those bitcoins.
What if someone wanted to steal those bitcoins? They would need both the public key and private key of the address. I know that it would take an enormous amount of time but is this technically doable?
Also, would mining pools be able to push to their clients a script to find those public and private keys? These pools have nowadays an enormous calculation power.
|
|
|
|
|
|
|
|
|
|
|
|
"In a nutshell, the network works like a distributed
timestamp server, stamping the first transaction to spend a coin. It
takes advantage of the nature of information being easy to spread but
hard to stifle." -- Satoshi
|
|
|
Advertised sites are not endorsed by the Bitcoin Forum. They may be unsafe, untrustworthy, or illegal in your jurisdiction.
|
|
|
|
joesmoe2012
|
 |
March 10, 2014, 03:46:23 AM |
|
This has been discussed before. To brute force a private key would take ages.
|
|
|
|
franky1
Legendary

 Online Online
Activity: 4214
Merit: 4475

|
 |
March 10, 2014, 03:48:07 AM |
|
Hello!
This is just for educational purposes. We know that Satoshi has an enormous amount of bitcoins and that he has not moved them for a long time. I think we also know the bitcoin addresses containing those bitcoins.
What if someone wanted to steal those bitcoins? They would need both the public key and private key of the address. I know that it would take an enormous amount of time but is this technically doable?
Also, would mining pools be able to push to their clients a script to find those public and private keys? These pools have nowadays an enormous calculation power.
run vanity gen using the first few characters of his address to get the privkey... ... see you in a thousand years once you get that exact key. much easier to find out his real identity and raid his computer, oops people are already doing that but finding innocent outsiders instead, poor dorian |
I DO NOT TRADE OR ACT AS ESCROW ON THIS FORUM EVER.
Please do your own research & respect what is written here as both opinion & information gleaned from experience. many people replying with insults but no on-topic content substance, automatically are 'facepalmed' and yawned at
|
|
|
|
seriouscoin
|
 |
March 10, 2014, 03:49:53 AM |
|
once in a while a dumbass come here and ask the same question.....
then he wonders why hes called dumb
|
|
|
|
|
|
TheMage
|
 |
March 10, 2014, 03:49:56 AM |
|
I have an issue with this, why can that picture use a Dyson sphere which is theoretically doable if we have the technology, but it cant be bothered to add in a quantum computer which is being actively worked on right now by governments and corporations? |
|
|
|
|
botolo86 (OP)
|
 |
March 10, 2014, 03:50:28 AM |
|
I know it would take eons but can we define the number of tries that we would need and the time needed to generate each try?
|
|
|
|
|
|
botolo86 (OP)
|
 |
March 10, 2014, 03:51:30 AM |
|
once in a while a dumbass come here and ask the same question.....
then he wonders why hes called dumb
Thanks, I love this spirit. |
|
|
|
|
|
joesmoe2012
|
 |
March 10, 2014, 03:51:56 AM |
|
Hello!
This is just for educational purposes. We know that Satoshi has an enormous amount of bitcoins and that he has not moved them for a long time. I think we also know the bitcoin addresses containing those bitcoins.
What if someone wanted to steal those bitcoins? They would need both the public key and private key of the address. I know that it would take an enormous amount of time but is this technically doable?
Also, would mining pools be able to push to their clients a script to find those public and private keys? These pools have nowadays an enormous calculation power.
run vanity gen using the first few characters of his address to get the privkey... ... see you in a thousand years once you get that exact key. much easier to find out his real identity and raid his computer, oops people are already doing that but finding innocent outsiders instead, poor dorian This is also a very serious concern with things like the MtGox database leak. Now everybody will know the real identities of all the top gox bitcoiners. |
|
|
|
DeathAndTaxes
Donator
Legendary

 Offline Offline
Activity: 1218
Merit: 1079
Gerald Davis

|
 |
March 10, 2014, 03:52:17 AM |
|
I have an issue with this, why can that picture use a Dyson sphere which is theoretically doable if we have the technology, but it cant be bothered to add in a quantum computer which is being actively worked on right now by governments and corporations?
The picture is of the sun. It is not known if a quantum computer capable of implementing shor's algorithm on 256 bit ECDSA keys will ever be possible. Even with a quantum computer if the pubkey is unknown Shor's algorithm can't be used. |
|
|
|
|
|
TheMage
|
 |
March 10, 2014, 04:00:20 AM |
|
I have an issue with this, why can that picture use a Dyson sphere which is theoretically doable if we have the technology, but it cant be bothered to add in a quantum computer which is being actively worked on right now by governments and corporations?
The picture is of the sun. It is not known if a quantum computer capable of implementing shor's algorithm on 256 bit ECDSA keys will ever be possible. Even with a quantum computer if the pubkey is unknown Shor's algorithm can't be used. I know its a star.......but did you read the text? You would think that if a civilization can construct a Dyson sphere they would have something better than windows 7........... |
|
|
|
|
joesmoe2012
|
 |
March 10, 2014, 04:01:34 AM |
|
I have an issue with this, why can that picture use a Dyson sphere which is theoretically doable if we have the technology, but it cant be bothered to add in a quantum computer which is being actively worked on right now by governments and corporations?
The picture is of the sun. It is not known if a quantum computer capable of implementing shor's algorithm on 256 bit ECDSA keys will ever be possible. Even with a quantum computer if the pubkey is unknown Shor's algorithm can't be used. I know its a star.......but did you read the text? You would think that if a civilization can construct a Dyson sphere they would have something better than windows 7........... Windows 8 :p I hear its all the rage. |
|
|
|
Swordsoffreedom
Legendary

 Offline Offline
Activity: 2758
Merit: 1115
Leading Crypto Sports Betting & Casino Platform


|
 |
March 10, 2014, 04:02:02 AM |
|
I have an issue with this, why can that picture use a Dyson sphere which is theoretically doable if we have the technology, but it cant be bothered to add in a quantum computer which is being actively worked on right now by governments and corporations?
The picture is of the sun. It is not known if a quantum computer capable of implementing shor's algorithm on 256 bit ECDSA keys will ever be possible. Even with a quantum computer if the pubkey is unknown Shor's algorithm can't be used. I thought it was a Schrodinger cat if that case happened bitcoin is and is not destroyed |
| ..Stake.com.. | | | ▄████████████████████████████████████▄
██ ▄▄▄▄▄▄▄▄▄▄ ▄▄▄▄▄▄▄▄▄▄ ██ ▄████▄
██ ▀▀▀▀▀▀▀▀▀▀ ██████████ ▀▀▀▀▀▀▀▀▀▀ ██ ██████
██ ██████████ ██ ██ ██████████ ██ ▀██▀
██ ██ ██ ██████ ██ ██ ██ ██ ██
██ ██████ ██ █████ ███ ██████ ██ ████▄ ██
██ █████ ███ ████ ████ █████ ███ ████████
██ ████ ████ ██████████ ████ ████ ████▀
██ ██████████ ▄▄▄▄▄▄▄▄▄▄ ██████████ ██
██ ▀▀▀▀▀▀▀▀▀▀ ██
▀█████████▀ ▄████████████▄ ▀█████████▀
▄▄▄▄▄▄▄▄▄▄▄▄███ ██ ██ ███▄▄▄▄▄▄▄▄▄▄▄▄
██████████████████████████████████████████ | | | | | | ▄▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▀▄
█ ▄▀▄ █▀▀█▀▄▄
█ █▀█ █ ▐ ▐▌
█ ▄██▄ █ ▌ █
█ ▄██████▄ █ ▌ ▐▌
█ ██████████ █ ▐ █
█ ▐██████████▌ █ ▐ ▐▌
█ ▀▀██████▀▀ █ ▌ █
█ ▄▄▄██▄▄▄ █ ▌▐▌
█ █▐ █
█ █▐▐▌
█ █▐█
▀▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▄▀█ | | | | | | ▄▄█████████▄▄
▄██▀▀▀▀█████▀▀▀▀██▄
▄█▀ ▐█▌ ▀█▄
██ ▐█▌ ██
████▄ ▄█████▄ ▄████
████████▄███████████▄████████
███▀ █████████████ ▀███
██ ███████████ ██
▀█▄ █████████ ▄█▀
▀█▄ ▄██▀▀▀▀▀▀▀██▄ ▄▄▄█▀
▀███████ ███████▀
▀█████▄ ▄█████▀
▀▀▀███▄▄▄███▀▀▀ | | | ..PLAY NOW.. |
|
|
|
|
IamCANADIAN013
|
 |
March 10, 2014, 04:04:22 AM |
|
Why would anyone want to even figure out a way to steal the coins? It would destroy Bitcoin, would it not?
|
|
|
|
|
|
joesmoe2012
|
 |
March 10, 2014, 04:05:35 AM |
|
Why would anyone want to even figure out a way to steal the coins? It would destroy Bitcoin, would it not?
How would it destroy bitcoin? |
|
|
|
|
joesmoe2012
|
 |
March 10, 2014, 04:07:01 AM |
|
a 'fatal' flaw in bitcoin ... Thats something I've always feared.
|
|
|
|
|
IamCANADIAN013
|
 |
March 10, 2014, 04:09:44 AM |
|
Why would anyone want to even figure out a way to steal the coins? It would destroy Bitcoin, would it not?
How would it destroy bitcoin? I figure it would just show how weak Bitcoin is security wise. I figure it would just destroy it's credibility. I could easily be wrong, that's just the way I see it. |
|
|
|
|
Bit_Happy
Legendary

 Offline Offline
Activity: 2100
Merit: 1040
A Great Time to Start Something!

|
 |
March 10, 2014, 04:10:34 AM |
|
Hello!
This is just for educational purposes. We know that Satoshi has an enormous amount of bitcoins and that he has not moved them for a long time. I think we also know the bitcoin addresses containing those bitcoins.
What if someone wanted to steal those bitcoins? They would need both the public key and private key of the address. I know that it would take an enormous amount of time but is this technically doable?
Also, would mining pools be able to push to their clients a script to find those public and private keys? These pools have nowadays an enormous calculation power.
run vanity gen using the first few characters of his address to get the privkey... ... see you in a thousand years once you get that exact key. much easier to find out his real identity and raid his computer, oops people are already doing that but finding innocent outsiders instead, poor dorian Yes that verification crap didn't work out too well. This is also a very serious concern with things like the MtGox database leak. Now everybody will know the real identities of all the top gox bitcoiners. |
|
|
|
|
TheMage
|
 |
March 10, 2014, 04:33:34 AM |
|
I have an issue with this, why can that picture use a Dyson sphere which is theoretically doable if we have the technology, but it cant be bothered to add in a quantum computer which is being actively worked on right now by governments and corporations?
The picture is of the sun. It is not known if a quantum computer capable of implementing shor's algorithm on 256 bit ECDSA keys will ever be possible. Even with a quantum computer if the pubkey is unknown Shor's algorithm can't be used. I thought it was a Schrodinger cat if that case happened bitcoin is and is not destroyed Can I post now? (stupid 360 second rule here.....) Ahem, only if you look at the coins  . |
|
|
|
jonald_fyookball
Legendary

 Offline Offline
Activity: 1302
Merit: 1004
Core dev leaves me neg feedback #abuse #political

|
 |
March 10, 2014, 05:04:58 AM |
|
Pilfer a few nugs from the jar when's in the bathroom?  |
|
|
|
|
Boris-The-Blade
|
 |
March 10, 2014, 09:15:24 AM |
|
Like stealing Satoshi's hoard of coins would be so casual
|
|
|
|
|
brokedummy
Legendary

 Offline Offline
Activity: 980
Merit: 1004

|
 |
March 10, 2014, 12:41:01 PM |
|
Step one: Find Chuck Norris
Step two: Get Chuck Norris to guess private keys on first try
.
.
.
Profit.
|
|
|
|
|
|
Klestin
|
 |
March 10, 2014, 02:18:58 PM |
|
I have an issue with this, why can that picture use a Dyson sphere which is theoretically doable if we have the technology, but it cant be bothered to add in a quantum computer which is being actively worked on right now by governments and corporations?
Quantum computers are not magical, and still must adhere to the physical laws of the universe. The text explains that their calculation depends on us inventing a computer circuit that can flip a bit using the smallest possible energy. They're not stacking up pentiums here, they're talking silly, near-magical "perfect" devices. |
|
|
|
|
|
lnternet
|
 |
March 10, 2014, 02:37:48 PM |
|
I have made a list of possible private keys of Satoshi. I will email them to anyone, just send me a PM.
|
1ntemetqbXokPSSkuHH4iuAJRTQMP6uJ9
|
|
|
Lauda
Legendary

 Offline Offline
Activity: 2674
Merit: 2965
Terminated.


|
 |
March 10, 2014, 02:47:04 PM |
|
I have an issue with this, why can that picture use a Dyson sphere which is theoretically doable if we have the technology, but it cant be bothered to add in a quantum computer which is being actively worked on right now by governments and corporations?
The picture is of the sun. It is not known if a quantum computer capable of implementing shor's algorithm on 256 bit ECDSA keys will ever be possible. Even with a quantum computer if the pubkey is unknown Shor's algorithm can't be used. It won't. |
"The Times 03/Jan/2009 Chancellor on brink of second bailout for banks" 😼 Bitcoin Core ( onion) |
|
|
|
S4VV4S
|
 |
March 10, 2014, 03:01:51 PM |
|
|
|
|
|
|
|
pozmu
|
 |
March 10, 2014, 03:36:43 PM |
|
Also, would mining pools be able to push to their clients a script to find those public and private keys? These pools have nowadays an enormous calculation power.
They could just fork Bitcoin code and add a rule that coins not moved for XX days/months/years are taken and put back to the pool of minable coins - I've seen some alt-coin proposing this. |
|
|
|
DeathAndTaxes
Donator
Legendary

 Offline Offline
Activity: 1218
Merit: 1079
Gerald Davis

|
 |
March 10, 2014, 03:48:35 PM |
|
Also, would mining pools be able to push to their clients a script to find those public and private keys? These pools have nowadays an enormous calculation power.
They could just fork Bitcoin code and add a rule that coins not moved for XX days/months/years are taken and put back to the pool of minable coins - I've seen some alt-coin proposing this. Sure and 99.999999999999999999999999999999% of Bitcoin clients would simply see those as invalid blocks. Miners which mine on that fork will end up with worthless coins and miners which remain on the real Bitcoin network will get more coins. |
|
|
|
|
DeathAndTaxes
Donator
Legendary

 Offline Offline
Activity: 1218
Merit: 1079
Gerald Davis

|
 |
March 10, 2014, 03:53:02 PM |
|
I have an issue with this, why can that picture use a Dyson sphere which is theoretically doable if we have the technology, but it cant be bothered to add in a quantum computer which is being actively worked on right now by governments and corporations?
Quantum computers are not magical, and still must adhere to the physical laws of the universe. The text explains that their calculation depends on us inventing a computer circuit that can flip a bit using the smallest possible energy. They're not stacking up pentiums here, they're talking silly, near-magical "perfect" devices. That isn't exactly true. As a simplistic answer the way QC work is they aren't "faster" they make the problem shorter/simpler. So while thermodynamics can't be bypassed, finding a solution will require less "work" than in classical computing. Still IIRC the larger number which has been factored using QC was something like 117 and it took nine days. Wake me up when someone can factor 32 bit numbers much less 2048 bit ones. |
|
|
|
|
|
kuroman
|
 |
March 10, 2014, 04:10:16 PM |
|
I don't understand how people claims that it will take thousands of year to crack the private key of a wallet. While yes with today computers or even clusters, it will take a thousands of years, I'm pretty sure that in a 20 years from now it will be a matter of days if not hours.
If we look at our computing power in the 60 and compare to the 80s, the whole computing power in a Saturn V rocket and the lunar module could fit in less than an Apple computer of the time, and if we compare the computing power of the 80s (Cray for example) with late 90s and easly 2000s, the power of supercomputer of the time could be assimilated to the power of a single chip, and between late 90s and nowadays is even more.... well lets put it this way, the faster supercomputer of 2000 in terms FLOPS was IBM ASCI White with it stagering 7.226 TFLOPS !! Well that's less than last year 7990 a Dual slot graphic card that you can set on your personnal desktop.
This without taking into consideration, alghorithms breakthrough or technological ones such as Quantum computing, hybrid system or even on the basic level, moving from Silicon to graphen would have a huge impact!
|
|
|
|
|
DeathAndTaxes
Donator
Legendary

 Offline Offline
Activity: 1218
Merit: 1079
Gerald Davis

|
 |
March 10, 2014, 04:18:43 PM |
|
I don't understand how people claims that it will take thousands of year to crack the private key of a wallet. While yes with today computers or even clusters, it will take a thousands of years, I'm pretty sure that in a 20 years from now it will be a matter of days if not hours. You (like most people) have difficulty grasping how large 2^256 is (or even 2^128 which is the effective security of 256 bit ECDSA keys). The 128 bit or 256 bit seems deceptively small. Nobody credible is saying classical computers could brute force keys in thousands of years..... it would be billions of years using all the energy of our sun. That also assumes you have a perfect computer. This without taking into consideration, alghorithms breakthrough or technological ones such as Quantum computing, hybrid system or even on the basic level, moving from Silicon to graphen would have a huge impact! None of those (except QC) would do anything more than switching from a teaspoon to a bucket when trying to empty an ocean. The only way a ECDSA private key will be successfully attacked is: a) The private key isn't random enough (insufficient entropy due to flaw in PRNG) b) ECDSA is cryptographically weakened/broken. c) It becomes possible to build a QC with the tens of thousands of qubits necessary to implement Shor's algorithm against a 256 bit ECDSA public key (and public key is known). |
|
|
|
|
AT101ET
Legendary

 Offline Offline
Activity: 3080
Merit: 1348

|
 |
March 10, 2014, 04:22:16 PM |
|
Do we actually know where his BTC are?
Its just a guess. What proof do we have that they are his/hers/theirs?
Regardless of that, why would you want to steal his stash.
Satoshi started it, and i'm sure he can finish it if he wanted to.
And anyway, stealing is wrong!
|
|
|
|
|
jonald_fyookball
Legendary

 Offline Offline
Activity: 1302
Merit: 1004
Core dev leaves me neg feedback #abuse #political

|
 |
March 10, 2014, 04:41:23 PM |
|
I don't understand how people claims that it will take thousands of year to crack the private key of a wallet. While yes with today computers or even clusters, it will take a thousands of years, I'm pretty sure that in a 20 years from now it will be a matter of days if not hours. You (like most people) have difficulty grasping how large 2^256 is (or even 2^128 which is the effective security of 256 bit ECDSA keys). The 128 bit or 256 bit seems deceptively small. Nobody credible is saying classical computers could brute force keys in thousands of years..... it would be billions of years using all the energy of our sun. That also assumes you have a perfect computer. This without taking into consideration, alghorithms breakthrough or technological ones such as Quantum computing, hybrid system or even on the basic level, moving from Silicon to graphen would have a huge impact! None of those (except QC) would do anything more than switching from a teaspoon to a bucket when trying to empty an ocean. The only way a ECDSA private key will be successfully attacked is: a) The private key isn't random enough (insufficient entropy due to flaw in PRNG) b) ECDSA is cryptographically weakened/broken. c) It becomes possible to build a QC with the tens of thousands of qubits necessary to implement Shor's algorithm against a 256 bit ECDSA public key (and public key is known). Care to give us a layman's explanation of Shor's algorithm? Also, I thought the public keys were the same as the bitcoin address? thanks! |
|
|
|
|
kuroman
|
 |
March 10, 2014, 05:05:13 PM
Last edit: March 10, 2014, 06:07:14 PM by kuroman |
|
You (like most people) have difficulty grasping how large 2^256 is (or even 2^128 which is the effective security of 256 bit ECDSA keys). The 128 bit or 256 bit seems deceptively small. As a math literate person I do gasp how huge 2^256 is. Nobody credible is saying classical computers could brute force keys in thousands of years..... it would be billions of years using all the energy of our sun. That also assumes you have a perfect computer. And I do agree with this as in TODAY, the math is simple, our most powerfull supercomputers calculates in 30sh PFlops that's about 30x10^15 Flops Time in year = 3600x(24x365+6) = 31557600s and 2^256 ~ 1.14x10^77 so it will take to crack it with the usumption that it will require 100Flops per combination = 1.14x10^79/(31557600x30x10^15) =~ 1.20x10^55 years ! BUT THAT'S NOT THE POINT! My point is if you consider only classical computing in the last 30 years we've moved from KiloFlops to PentaFlops or 10^15Flops in terms of processing power, it is easy to assume that in the next few decades, we can easly achieve 10^30 / 10^40 (we've already gone past the point of cracking 2^128 or 128bits in a few seconds) and it will reach eventually 10^70+. In the 80/90s people (like you) were claiming 56 bit encryption was impossible to crack, and you know what, it takes like 3s and less to break with our current supercomputers! And this doesn't take into consideration Alghorithm break trought as I mentioned, even the current classic computer with the proper alghorithms can simulate Quantum computers and have similar results in some areas for example......... Now if you add in the mix Quantum computing which will bring computing to a whole other level as the potentiel from a dozen of Qubit and the impact they have is already being proven. None of those (except QC) would do anything more than switching from a teaspoon to a bucket when trying to empty an ocean. Wrong as proven above. a) The private key isn't random enough (insufficient entropy due to flaw in PRNG)
b) ECDSA is cryptographically weakened/broken.
c) It becomes possible to build a QC with the tens of thousands of qubits necessary to implement Shor's algorithm against a 256 bit ECDSA public key (and public key is known).
It's not limited to this as proven above but : a = Possible as proven with AES thanks to NSA Middeling b = Possible c = it will happen in the next decade or the one folowing, considering we've moved from 4 Qubits to 128 in a very short laps of time heck Dwave just released a 512 Qbits Processor and they claim to have a 1000 Qubits in their lab ready to roll http://www.washingtonpost.com/blogs/the-switch/wp/2014/01/10/this-company-sold-google-a-quantum-computer-heres-how-it-works/Also the Shor Alghorithm is not the most efficient Alghrorithm beyond 600 Qubits in comparaison to Fourier Transform On one hand factoring and calculation logs and the other the usual linear transform that can be decomposed to I or Unitary Matrix, which Qubits likes. |
|
|
|
|
|
tkbx
|
 |
March 10, 2014, 05:59:05 PM |
|
Hello!
This is just for educational purposes. We know that Satoshi has an enormous amount of bitcoins and that he has not moved them for a long time. I think we also know the bitcoin addresses containing those bitcoins.
What if someone wanted to steal those bitcoins? They would need both the public key and private key of the address. I know that it would take an enormous amount of time but is this technically doable?
Also, would mining pools be able to push to their clients a script to find those public and private keys? These pools have nowadays an enormous calculation power.
Good luck. If I recall correctly, there are more possible private keys than atoms on earth. If everyone on Earth had a copy of the world's most powerful supercomputer for free, and they were all trying to crack the same address 24/7 with their supercomputer, it would still take too long for anyone who started the process to ever live to see the address be cracked. |
|
|
|
|
jonald_fyookball
Legendary

 Offline Offline
Activity: 1302
Merit: 1004
Core dev leaves me neg feedback #abuse #political

|
 |
March 10, 2014, 06:13:16 PM |
|
it is easy to assume that in the next few decades, we can easly achieve 10^30 / 10^40 (we've already gone past the point of cracking 2^128 or 128bits in a few seconds) and it will reach eventually 10^70+.
Are you sure? don't we start to hit the limits of the speed of light and how many atoms thin we can go on a chip, etc... we can't just keep adding zeros like that... we hit physical limitations |
|
|
|
|
kuroman
|
 |
March 10, 2014, 06:20:39 PM
Last edit: March 10, 2014, 06:35:47 PM by kuroman |
|
it is easy to assume that in the next few decades, we can easly achieve 10^30 / 10^40 (we've already gone past the point of cracking 2^128 or 128bits in a few seconds) and it will reach eventually 10^70+.
Are you sure? don't we start to hit the limits of the speed of light and how many atoms thin we can go on a chip, etc... we can't just keep adding zeros like that... we hit physical limitations Actually we can thanks to technological breaktrought, In classical computing , moving from Silicon to Graphen will help to keep us in the moor law for the two decades at least, the problem when will reach the point where quantum mechanics effect will start to manifest in terms of die shrink and this is one of the reason we are moving to Quantum computing where todays issue is the opposite |
|
|
|
|
Remember remember the 5th of November
Legendary

 Offline Offline
Activity: 1862
Merit: 1011
Reverse engineer from time to time

|
 |
March 10, 2014, 06:24:37 PM |
|
Hello!
This is just for educational purposes. We know that Satoshi has an enormous amount of bitcoins and that he has not moved them for a long time. I think we also know the bitcoin addresses containing those bitcoins.
What if someone wanted to steal those bitcoins? They would need both the public key and private key of the address. I know that it would take an enormous amount of time but is this technically doable?
Also, would mining pools be able to push to their clients a script to find those public and private keys? These pools have nowadays an enormous calculation power.
Good luck. If I recall correctly, there are more possible private keys than atoms on earth. If everyone on Earth had a copy of the world's most powerful supercomputer for free, and they were all trying to crack the same address 24/7 with their supercomputer, it would still take too long for anyone who started the process to ever live to see the address be cracked. Actually, nearly as many atoms in the entire universe if I remember correctly. So earth is just a small number of atoms compared to the priv keys. |
BTC:1AiCRMxgf1ptVQwx6hDuKMu4f7F27QmJC2
|
|
|
|
vinipoars
|
 |
March 10, 2014, 06:32:21 PM |
|
I'm renting my quantum miner. Please, deposit 10000 BTC to the adress below and we'll do the job.  |
|
|
|
|
|
kuroman
|
 |
March 10, 2014, 06:40:17 PM |
|
I'm renting my quantum miner. Please, deposit 10000 BTC to the adress below and we'll do the job.  Hello borther from the future, if you can go back in time why don't you just start mining with Nakamoto when he released the code, you'll probably be riched if you just want bitcoins |
|
|
|
|
DeathAndTaxes
Donator
Legendary

 Offline Offline
Activity: 1218
Merit: 1079
Gerald Davis

|
 |
March 10, 2014, 06:44:18 PM
Last edit: March 10, 2014, 06:56:08 PM by DeathAndTaxes |
|
BUT THAT'S NOT THE POINT! My point is if you consider only classical computing in the last 30 years we've moved from KiloFlops to PentaFlops .. it is easy to assume that in the next few decades, we can easly achieve 10^30 / 10^40 Which is still essentially nothing. For classical computing you move the timescale from quadrillions of years down to only millions of years. Congratulations. (we've already gone past the point of cracking 2^128 or 128bits in a few seconds) No we haven't, no key with 128 bit strength has been brute forced. You can't simply compare key size. A 256 bit ECC key has equivalent strength to a 3,072 bit RSA key and a 128 bit symmetric key/hash. You may be talking about some individual algorithms being cryptographically broken, it is hard to tell because you are all over the place. I already pointed out that is possible but it has nothing to do with In the 80/90s people (like you) were claiming 56 bit encryption was impossible to crack, and you know what, it takes like 3s and less to break with our current supercomputers! No people like me would have been warning that 56 bits was insufficient due to the fact that it was within 1000x of what current computing power was capable of. That is a far cry from saying 128 bit key strength is secure because it uses energy on a scale that would make brute infeasible. If we pretend the entire Bitcoin network (30 PH/s) "could" brute force symmetric keys at the same speed instead it would be able to brute force an 80 bit symmetric key in about one year. If it was 1000x more powerful it could brute force a 96 bit symmetric key in about a century. If it was a million times powerful it would still take on average a millennium to brute force a 128 bit symmetric key. To do it in a year would require a system which is a billion times more powerful. None of those (except QC) would do anything more than switching from a teaspoon to a bucket when trying to empty an ocean. Wrong as proven above. Proven doesn't mean what you think it means. Proven doesn't mean spouting out false statements, gibberish, and strawmen. [regarding 40,000 qubit computer] it will happen in the next decade or the one folowing, considering we've moved from 4 Qubits to 128 in a very short laps of time heck Dwave just released a 512 Qbits Processor and they claim to have a 1000 Qubits in their lab ready to roll Dwave's system is not capable of implementing Shor's algorithm. It uses a process called quantum annealing. Quantum Computing isn't some super duper magical bullet which solves all problems all the time. Quantum annealing is a pretty cool concept for solving certain types of problems like pathfinding, simulating organic processes, network optimization, etc. It is completely useless for the purposes of breaking cryptographic keys. On the progress of building a true general purpose quantum computer capable of implementing shor's algorithm the progress has been very slow. 15 was factored in 2001 using Shor's algorithm and a 4 qubits QC. By 2012 that had progressed to factoring 21 in using 5 qubits. One estimate for the total physical qubits (including circuits for error control and correction) necessary for breaking 256 bit ECC is on the order of 40,000 qubits. We went from 4 to 5 in the space of a decade and the "finish line" is 40,000 qubits. That could be doubled by switching to a 512 bit curve. Quantum Decoherence is a bitch. The problem becomes increasingly difficult as the size of the computer grows. It may not be possible to accomplish that in our lifetimes. Wake me up when someone factors 32 bit number using quantum computing. If QC becomes a credible threat Bitcoin can evolve to addresses which use post-quantum cryptography. |
|
|
|
|
DeathAndTaxes
Donator
Legendary

 Offline Offline
Activity: 1218
Merit: 1079
Gerald Davis

|
 |
March 10, 2014, 06:47:44 PM |
|
I thought the public keys were the same as the bitcoin address?
Addresses are the Public Key Hash (PubKeyHash) along with with version and checksum information encoded in Base58. When you send funds to a user you are sending it to their PubKeyHash (which your client reverses from the address you provide). This is why one reason why address reuse is discouraged. Once funds are spent from an address the actual PubKey is known (it included in the input so other nodes can validate the signature). |
|
|
|
|
|
vinipoars
|
 |
March 10, 2014, 06:55:49 PM |
|
I'm renting my quantum miner. Please, deposit 10000 BTC to the adress below and we'll do the job.  Hello borther from the future, if you can go back in time why don't you just start mining with Nakamoto when he released the code, you'll probably be riched if you just want bitcoins Are you sure I didn't?  |
|
|
|
|
jonald_fyookball
Legendary

 Offline Offline
Activity: 1302
Merit: 1004
Core dev leaves me neg feedback #abuse #political

|
 |
March 10, 2014, 07:11:22 PM |
|
I thought the public keys were the same as the bitcoin address?
Addresses are the Public Key Hash (PubKeyHash) along with with version and checksum information encoded in Base58. When you send funds to a user you are sending it to their PubKeyHash (which your client reverses from the address you provide). This is why one reason why address reuse is discouraged. Once funds are spent from an address the actual PubKey is known (it included in the input so other nodes can validate the signature). Thanks for the info on that, but then how to avoid address resuse? If i have 10 coins and I send you 2 coins, what I do with the 8 left in my wallet? Are you saying I have to immediately move them to another address? |
|
|
|
jonald_fyookball
Legendary

 Offline Offline
Activity: 1302
Merit: 1004
Core dev leaves me neg feedback #abuse #political

|
 |
March 10, 2014, 07:14:53 PM |
|
while we're on the topic of "can wallets be bruteforce cracked"...
when we talk about supercomputer speed (petaflops, etc) (floating point operations) -- how many
floating point operations actually go into trying 1 private key ?
|
|
|
|
DeathAndTaxes
Donator
Legendary

 Offline Offline
Activity: 1218
Merit: 1079
Gerald Davis

|
 |
March 10, 2014, 07:22:24 PM |
|
Thanks for the info on that, but then how to avoid address resuse? If i have 10 coins and I send you 2 coins, what I do with the 8 left in my wallet? Are you saying I have to immediately move them to another address? Your wallet already does that. Bitcoin doesn't work on the concept of balances it works on the concept of creating and destroying outputs. So if you have an output worth 10 BTC and you want to send me two your client creates a tx which destroys the 10 BTC output and creates two new outputs valued at 2 BTC (to me) and 8 BTC (to a new address in your wallet). while we're on the topic of "can wallets be bruteforce cracked"...
when we talk about supercomputer speed (petaflops, etc) (floating point operations) -- how many
floating point operations actually go into trying 1 private key ?
Zero. We are interested in integer math when brute forcing private keys. Flops refers to floating point math. There is no conversion factor which would work for all systems. Generally speaking computer science doesn't look at the individual implementations to determine if something is infeasible. As an example say a given computer would require 1000 steps to make one attempt to brute force a key and it will take more energy than 20 of our suns and 10 billion years. Now lets say you could reduce that to a single step. Ok now it only takes 1 billion years and more energy than 2 of our suns. Either way it is infeasible. Any classical computing problem which is more complex then O (2^128) is generally viewed as infeasible. Some people use the word improbable but infeasible is a stronger word. It is improbable you will win the lottery however it is infeasible that you will brute force a 128 bit symmetric key (simply requires material and energy on a scale the human race is utterly incapable of). In comparison to the lottery it would be like you win seven lotteries in a row by purchasing just a single ticket. |
|
|
|
|
jonald_fyookball
Legendary

 Offline Offline
Activity: 1302
Merit: 1004
Core dev leaves me neg feedback #abuse #political

|
 |
March 10, 2014, 07:30:52 PM |
|
it is infeasible that you will brute force a 128 bit symmetric key (simply requires material and energy on a scale the human race is utterly incapable of).
Cool! I think people just want to know exactly how infeasible it really is... It can help confidence in bitcoin. My thinking goes like this: if there's 2^128 combinations, then if you could try a trillion, trillion combinations a second, it would take you 8.9 million years. I'm just wondering if we can really try that many per second. It sounds like maybe a lot longer to try a private key than to do 1 floating point operation |
|
|
|
DeathAndTaxes
Donator
Legendary

 Offline Offline
Activity: 1218
Merit: 1079
Gerald Davis

|
 |
March 10, 2014, 07:39:23 PM |
|
I think people just want to know exactly how infeasible it really is... It can help confidence in bitcoin. Someone with a lot of bitcoins could do a public contest. Brute forcing a 256 bit ECDSA key (has 128 bit security) is infeasible so nobody would attempt it (well not anyone with any real power) however one could make the problem simpler. For example move 1,000 BTC to an address and provide publicly half of the private key. This would mean someone could brute force the key on average in 2^64 attempts. The blockchain will be proof of if someone accomplished it or not. Even that would be an incredibly difficult problem, but it is feasible (back to the whole infeasible vs improbable). If/when someone can steal those coins just keep in mind that brute forcing a full key would be 2^64 = 18,446,744,073,709,600,000 x harder/longer. |
|
|
|
|
Buffer Overflow
Legendary

 Offline Offline
Activity: 1652
Merit: 1015

|
 |
March 10, 2014, 07:48:58 PM |
|
Why would anyone want to even figure out a way to steal the coins? It would destroy Bitcoin, would it not?
How would it destroy bitcoin? Would you still use bitcoin if your private key could be derived from your public bitcoin address? |
|
|
|
jonald_fyookball
Legendary

 Offline Offline
Activity: 1302
Merit: 1004
Core dev leaves me neg feedback #abuse #political

|
 |
March 10, 2014, 07:51:48 PM |
|
I think people just want to know exactly how infeasible it really is... It can help confidence in bitcoin. Someone with a lot of bitcoins could do a public contest. Brute forcing a 256 bit ECDSA key (has 128 bit security) is infeasible so nobody would attempt it (well not anyone with any real power) however one could make the problem simpler. For example move 1,000 BTC to an address and provide publicly half of the private key. This would mean someone could brute force the key on average in 2^64 attempts. The blockchain will be proof of if someone accomplished it or not. Even that would be an incredibly difficult problem, but it is feasible (back to the whole infeasible vs improbable). If/when someone can steal those coins just keep in mind that brute forcing a full key would be 2^64 = 18,446,744,073,709,600,000 x harder/longer. are we correct to assume that to "try" a private key, you'd have to go through all the steps in the SHA256 algo? |
|
|
|
|
kuroman
|
 |
March 10, 2014, 08:08:52 PM
Last edit: March 10, 2014, 08:28:15 PM by kuroman |
|
Which is still essentially nothing. For classical computing you move the timescale from quadrillions of years down to only millions of years. Congratulations.
Wait what? did you even read beyond that point? you are partially quoting to prove that you are right is that what you trying to do here? I repeat my self todays computing power 10^15+ so theoritically if classical computing keeps going forward at the same pace it's advanced with since the 60s we will be looking at 10^30 10^40 Flops in the next decade or two which is enough to crack 128bits in a few seconds and we will move on to 10^70 Flops and beyond in another decade or two from there, that is without taking into consideration anything else! which not even remotly true No we haven't, no key with 128 bit strength has been brute forced. You can't simply compare key size. A 256 bit ECC key has equivalent strength to a 3,072 bit RSA key and a 128 bit symmetric key/hash. You may be talking about some individual algorithms being cryptographically broken, it is hard to tell because you are all over the place. I already pointed out that is possible but it has nothing to do with You do really have some reading issues, please reread my sentence, and correct your statement I think I was clear enough, I do understand that I make mistakes from time to time because I'm not an english native speaker but please. No people like me would have been warning that 56 bits was insufficient due to the fact that it was within 1000x of what current computing power was capable of. That is a far cry from saying 128 bit key strength is secure because it uses energy on a scale that would make brute infeasible. If we pretend the entire Bitcoin network (30 PH/s) "could" brute force symmetric keys at the same speed instead it would be able to brute force an 80 bit symmetric key in about one year. If it was 1000x more powerful it could brute force a 96 bit symmetric key in about a century. If it was a million times powerful it would still take on average a millennium to brute force a 128 bit symmetric key. To do it in a year would require a system which is a billion times more powerful. No you woudn't, because people like you did claim the same and it was similar case scenarion in the 80s. And it wasn't x1000 diference I don't even know where are you getting that number from, The Cray Supercomputer from the 80s had 80MFlops or 80x10^6 (The Cray 2 which came in the end of the 80s has 1.2GFlops!) Todays supercomputer for example the Tianhe-2 has a computing power of 34x10^15 ! moving from 56bit to 128 means we squared the difficulty aka (2^56)^2 = 2^128 now if you compare this to computing power and how it is increasing (10^6)^2 = 10^12 <<< 10^15 And again you are taking into consideration CURRENT technology, with CURRENT technology it will take almost infinity to brute force even 128bit not even talking about 256 and I DO NOT DISAGREE WITH THIS, but that's not the point as I've been explaning to you repeatdly you are just being obstined here None of those (except QC) would do anything more than switching from a teaspoon to a bucket when trying to empty an ocean. Wrong as proven above. Proven doesn't mean what you think it means. Proven doesn't mean spouting out false statements, gibberish, and strawmen. False statement? the one you didn't prove wrong or false? the math calculation? the Flops from the supercomputer trough the decades which part is fasle? I'm sorry but you are loosing even more credibility here. Dwave's system is not capable of implementing Shor's algorithm. It uses a process called quantum annealing. Quantum Computing isn't some super duper magical bullet which solves all problems all the time. Quantum annealing is a pretty cool concept for solving certain types of problems like pathfinding, simulating organic processes, network optimization, etc. It is completely useless for the purposes of breaking cryptographic keys.
On the progress of building a true general purpose quantum computer capable of implementing shor's algorithm the progress has been very slow. 15 was factored in 2001 using Shor's algorithm and a 4 qubits QC. By 2012 that had progressed to factoring 21 in using 5 qubits. One estimate for the total physical qubits (including circuits for error control and correction) necessary for breaking 256 bit ECC is on the order of 40,000 qubits. We went from 4 to 5 in the space of a decade and the "finish line" is 40,000 qubits. That could be doubled by switching to a 512 bit curve. Quantum Decoherence is a bitch.
The problem becomes increasingly difficult as the size of the computer grows. It may not be possible to accomplish that in our lifetimes. Wake me up when someone factors 32 bit number using quantum computing. If QC becomes a credible threat Bitcoin can evolve to addresses which use post-quantum cryptography.
That's a whole other debate and the only credible paper about on how DWave computer or how much it is a Quantum Computer is this one http://arxiv.org/abs/1401.7087But Again DWave is by far not the only one in the field. As for Quantum Annealing is a LEGIT interpretation of Quantum computing, as we are talking about Quantum-mechanical superposition principale here! And when use Quantum Mechanics principales and Quanta to compute, isn't this what Quantum computing is about? |
|
|
|
|
|
porcupine87
|
 |
March 10, 2014, 08:09:57 PM |
|
Here you have list of all private keys. You can just simply look it up: http://directory.io/ |
"Morality, it could be argued, represents the way that people would like the world to work - whereas economics represents how it actually does work." Freakonomics
|
|
|
DeathAndTaxes
Donator
Legendary

 Offline Offline
Activity: 1218
Merit: 1079
Gerald Davis

|
 |
March 10, 2014, 08:16:59 PM |
|
Flop flop flop flop flops
I am not going to waste my time if you can't even realize that flops aren't ever used in brute forcing private keys. |
|
|
|
|
|
kuroman
|
 |
March 10, 2014, 08:23:20 PM |
|
Flop flop flop flop flops
I am not going to waste my time if you can't even realize that flops aren't ever used in brute forcing private keys. lol Mr Obvious (that's to say I don't disagree or rather it's partially true), but aren't the Flops used to represent the computing power of a device? or at least legit way to do so? |
|
|
|
|
|
porcupine87
|
 |
March 10, 2014, 08:30:32 PM |
|
Brute forcing a 256 bit ECDSA key (has 128 bit security) is infeasible
Sorry, why is it only 128bit security? |
"Morality, it could be argued, represents the way that people would like the world to work - whereas economics represents how it actually does work." Freakonomics
|
|
|
|
lnternet
|
 |
March 10, 2014, 08:36:35 PM |
|
Sorry, why is it only 128bit security?
Best algorithms need around sqrt(#bit) steps, so you have about half the exponent level in bit security. |
1ntemetqbXokPSSkuHH4iuAJRTQMP6uJ9
|
|
|
|
kuroman
|
 |
March 10, 2014, 08:41:30 PM |
|
Brute forcing a 256 bit ECDSA key (has 128 bit security) is infeasible
Sorry, why is it only 128bit security? AES-128, RSA-3072 because the size of the corps needs to be approximatly twice as big as the security degree F(2^m) Elliptical curbs, the discrete function is O(sqrt(n)) rho Pollard Alghorithm? I'm not sure about the algho |
|
|
|
|
|
lnternet
|
 |
March 10, 2014, 08:41:58 PM |
|
kuroman, Moore's law will not go on much longer the way it has been advancing by smaller hardware. by ~2020 you reach the point where moore's law requires a transistor the size of an atom. (eg http://www.pcworld.com/article/2032913/the-end-of-moores-law-is-on-the-horizon-says-amd.html) There could a major break through elsewhere, but it would be a coincidence if that happens to match with Moore's. Anything is this area is wild speculation and will probably not get us anywhere. |
1ntemetqbXokPSSkuHH4iuAJRTQMP6uJ9
|
|
|
Remember remember the 5th of November
Legendary

 Offline Offline
Activity: 1862
Merit: 1011
Reverse engineer from time to time

|
 |
March 10, 2014, 08:44:51 PM |
|
Look harder in the website. Do you see a search button? Figured. But of course if you call simply look it up the act of traversing 2^256 keys manually, page by page, then you need to visit a mental hospital. |
BTC:1AiCRMxgf1ptVQwx6hDuKMu4f7F27QmJC2
|
|
|
DeathAndTaxes
Donator
Legendary

 Offline Offline
Activity: 1218
Merit: 1079
Gerald Davis

|
 |
March 10, 2014, 08:47:16 PM |
|
Brute forcing a 256 bit ECDSA key (has 128 bit security) is infeasible
Sorry, why is it only 128bit security? The fastest known algorithms to derive a private ECC key from the public key are O ( 2^(n/2) ) where n is key length. Now if the attacker ignores this faster solution and simply tried random (or sequential) private keys until a match was found then it would take much longer (2^256 not 2^128) however security is based on the fastest possible solution. It is important to point out that the fastest algorithms require the PubKey to be known. If the PubKey is not known then the only method would be an exhaustive attack on the private key and computing the PubKey. This is another good reason to not reuse addresses (and thus the pubkey remains unknown). Key size doesn't necessarily equal security. All of these key/digest sizes have 128 bit security128 bit AES (symmetric encryption) 128 bit SHA-2 (hashing algorithm) 256 bit ECC (public key cryptography - elliptical curve) 3,072 bit RSA (public key cryptography - Integer factorization) Generally hashing algorithms and symmetric key systems have a security equal to their key length (unless they have vulnerabilities or weaknesses). However due to the nature of public key systems (the public key has a mathematical relationship to the private key) this not true for public key systems. The key size will always be larger than the effective security (or key strength). How much larger depends on how difficult it is to derive the private key from the public key. If you look at RSA and ECC you can see that to achieve the same security RSA requires much larger keys (and signatures). This makes ECC based systems more useful in decentralized systems like Bitcoin. |
|
|
|
|
|
kuroman
|
 |
March 10, 2014, 08:54:21 PM
Last edit: March 10, 2014, 09:04:58 PM by kuroman |
|
kuroman, Moore's law will not go on much longer the way it has been advancing by smaller hardware. by ~2020 you reach the point where moore's law requires a transistor the size of an atom. (eg http://www.pcworld.com/article/2032913/the-end-of-moores-law-is-on-the-horizon-says-amd.html) There could a major break through elsewhere, but it would be a coincidence if that happens to match with Moore's. Anything is this area is wild speculation and will probably not get us anywhere. Actually I've already answered this question, there are many ways to extend the moors law, such as 3D transistors and nanomaterials breaktrough such as Graphen and these aren't vaporware, they already exist, it's just that the manufacturing process needs to be generalised and it will not happen till we start hitting Silicon/Copper limits (as it will require to review the whole fab industry from technics to equipement which requires $$$$) http://e2e.ti.com/blogs_/b/thinkinnovate/archive/2013/03/01/graphene-s-potential-to-extend-moore-s-law.aspxhttp://phys.org/news/2014-02-team-aims-graphene-nanoribbon-wires.htmlEventually we will reach the point of quantum mechanics interference, and where the lasers won't be able to keep up, but by that time which is at least a couple of decades ahead of us Quantum computer would operational, todays Quantum computer are still far from it |
|
|
|
|
jonald_fyookball
Legendary

 Offline Offline
Activity: 1302
Merit: 1004
Core dev leaves me neg feedback #abuse #political

|
 |
March 10, 2014, 08:57:37 PM |
|
i think we all agree, best case scenario, we are decades away from even being close
to crack 128 bit security, and by then , bitcoin could be updated... so its completely
unfeasible to steal Satoshi's stash with supercomputers using brute force.
|
|
|
|
|
kuroman
|
 |
March 10, 2014, 09:03:16 PM |
|
i think we all agree, best case scenario, we are decades away from even being close
to crack 128 bit security, and by then , bitcoin could be updated... so its completely
unfeasible to steal Satoshi's stash with supercomputers using brute force.
You resume the situation perfectly, unless there is a major flaw or a NSA backdoor and co in the encryption protocol, but that's another story I guess. |
|
|
|
|
jonald_fyookball
Legendary

 Offline Offline
Activity: 1302
Merit: 1004
Core dev leaves me neg feedback #abuse #political

|
 |
March 10, 2014, 09:08:42 PM |
|
|
|
|
|
GreekBitcoin
Legendary

 Offline Offline
Activity: 1428
Merit: 1001
getmonero.org


|
 |
March 10, 2014, 09:19:01 PM |
|
kuroman, Moore's law will not go on much longer the way it has been advancing by smaller hardware. by ~2020 you reach the point where moore's law requires a transistor the size of an atom. (eg http://www.pcworld.com/article/2032913/the-end-of-moores-law-is-on-the-horizon-says-amd.html) There could a major break through elsewhere, but it would be a coincidence if that happens to match with Moore's. Anything is this area is wild speculation and will probably not get us anywhere. Actually I've already answered this question, there are many ways to extend the moors law, such as 3D transistors and nanomaterials breaktrough such as Graphen and these aren't vaporware, they already exist, it's just that the manufacturing process needs to be generalised and it will not happen till we start hitting Silicon/Copper limits (as it will require to review the whole fab industry from technics to equipement which requires $$$$) http://e2e.ti.com/blogs_/b/thinkinnovate/archive/2013/03/01/graphene-s-potential-to-extend-moore-s-law.aspxhttp://phys.org/news/2014-02-team-aims-graphene-nanoribbon-wires.htmlEventually we will reach the point of quantum mechanics interference, and where the lasers won't be able to keep up, but by that time which is at least a couple of decades ahead of us Quantum computer would operational, todays Quantum computer are still far from it jesus m8. you dont get the point.... it has nothing to do with computers. it has to do with physics limitations. you need energy to calculate whatever and even if you had a 100% efficient computer you would need more energy than the sun will give in its lifetime... |
|
|
|
|
|
kuroman
|
 |
March 10, 2014, 10:07:06 PM
Last edit: March 10, 2014, 11:48:05 PM by kuroman |
|
kuroman, Moore's law will not go on much longer the way it has been advancing by smaller hardware. by ~2020 you reach the point where moore's law requires a transistor the size of an atom. (eg http://www.pcworld.com/article/2032913/the-end-of-moores-law-is-on-the-horizon-says-amd.html) There could a major break through elsewhere, but it would be a coincidence if that happens to match with Moore's. Anything is this area is wild speculation and will probably not get us anywhere. Actually I've already answered this question, there are many ways to extend the moors law, such as 3D transistors and nanomaterials breaktrough such as Graphen and these aren't vaporware, they already exist, it's just that the manufacturing process needs to be generalised and it will not happen till we start hitting Silicon/Copper limits (as it will require to review the whole fab industry from technics to equipement which requires $$$$) http://e2e.ti.com/blogs_/b/thinkinnovate/archive/2013/03/01/graphene-s-potential-to-extend-moore-s-law.aspxhttp://phys.org/news/2014-02-team-aims-graphene-nanoribbon-wires.htmlEventually we will reach the point of quantum mechanics interference, and where the lasers won't be able to keep up, but by that time which is at least a couple of decades ahead of us Quantum computer would operational, todays Quantum computer are still far from it jesus m8. you dont get the point.... it has nothing to do with computers. it has to do with physics limitations. you need energy to calculate whatever and even if you had a 100% efficient computer you would need more energy than the sun will give in its lifetime... Jesus m8, you need to read previous comments, point that was previously discussed, if you have a counter argument even if I stated facts and not speculations please feel free to lay it down instead of repeating what you are told or heard without a minimum of thinking. |
|
|
|
|
Remember remember the 5th of November
Legendary

 Offline Offline
Activity: 1862
Merit: 1011
Reverse engineer from time to time

|
 |
March 10, 2014, 10:07:50 PM |
|
I am curious, this doesn't mean I will understand even one word from that paper there. A bit too advanced for me. |
BTC:1AiCRMxgf1ptVQwx6hDuKMu4f7F27QmJC2
|
|
|
jonald_fyookball
Legendary

 Offline Offline
Activity: 1302
Merit: 1004
Core dev leaves me neg feedback #abuse #political

|
 |
March 10, 2014, 10:08:45 PM |
|
if the network hashrate is 30,000,000 Gh/S,
isn't that 30 million billion hashes per second? would be the
same as enough computing power to try 30 million billion private
keys per second?
At that rate, it would only take the entire network 359,676 years,
not the billions of years said...
|
|
|
|
|
lnternet
|
 |
March 10, 2014, 10:13:50 PM |
|
if the network hashrate is 30,000,000 Gh/S,
isn't that 30 million billion hashes per second? would be the
same as enough computing power to try 30 million billion private
keys per second?
YES
At that rate, it would only take the entire network 359,676 years,
not the billions of years said...
NO
30e15 per second
9.5e23 per year
2^256 ~ 1e77
so makes about 1e54 years
|
1ntemetqbXokPSSkuHH4iuAJRTQMP6uJ9
|
|
|
DeathAndTaxes
Donator
Legendary

 Offline Offline
Activity: 1218
Merit: 1079
Gerald Davis

|
 |
March 10, 2014, 10:15:20 PM
Last edit: March 10, 2014, 11:03:07 PM by DeathAndTaxes |
|
if the network hashrate is 30,000,000 Gh/S,
isn't that 30 million billion hashes per second? would be the
same as enough computing power to try 30 million billion private
keys per second?
At that rate, it would only take the entire network 359,676 years,
not the billions of years said...
Good logic, but you have a math error I believe. The network is 30 PH/s which is 30*10^15. Simple trick is to just count the metric prefixes (each one is a factor of 1000). So kilohash, megahash, gigahash, terrahash, petahash is 1,2,3,4,5 so 1000^5. The time required with the assumptions you have would be 359,676,102,360,200 years. If we assume a network one trillion times more powerful it would still be 360 years. However even that is unlikely. A couple points to consider: 1) The network can't do anything but compute hashes but if we assume it could be repurposed to brute force EDSA keys it would take more computing cycles to perform one ECC attempt than it does to perform one SHA-2 hash. It would be something on the order of 80x as long (although that is some crude estimate on my hardware). So 30 PH/s wouldn't be 30 PK/s but maybe 1 PK/s (peta keys attempted per second) but his is minor compared to #2 below. 2) The security of ECDSA is 128 bit if the PubKey is known. If it the PubKey is unknown the only fastest attack is to attempt a preimage of the PubKeyHash. That has a complexity of 2^160 which is 2^32 larger or ~ 4 billion. Even if you could break a known PubKey in one year it would take 4 billion years to break the hash of an unknown pubkey. Keys with 128 bit security are infeasible to break by brute force using classical computing. However this doesn't mean that they can't be broken by cryptanalysis or quantum computing (which "go around" the problem rather than try to beat it by the pure expenditure of computing power). |
|
|
|
|
|
E.exchanger
|
 |
March 10, 2014, 10:42:40 PM |
|
You definitely be kidding wait you are not  then what makes you think anyone will bruteforce the keys or maybe someone will for his 10th generation to enjoy the money makes real sense   |
|
|
|
|
jonald_fyookball
Legendary

 Offline Offline
Activity: 1302
Merit: 1004
Core dev leaves me neg feedback #abuse #political

|
 |
March 10, 2014, 11:00:13 PM |
|
Good logic, but you have a math error I believe.
oops, yeah i mistook a comma for a period on my calculator. Yes, its 359,676,102,360,200 years with today's entire bitcoin network trying to crack one private key, and that's assuming the network could try a key at the same rate it can try a hash, and also assuming the public key is known.  Brute force, definitely out even with all the fancy lasers and vapors and hexagonal layer thingies. What about breaking the encryption itself... this is a whole new conversation ...how close do you think anyone is to cracking SHA-256 ? FYI, here's a javascript implementation of SHA-256. its more clear than the white paper version if you can read a bit of code. Not suggesting read every line, but you see the overall complexity. http://www.movable-type.co.uk/scripts/sha256.html
|
|
|
|
|
vinipoars
|
 |
March 10, 2014, 11:14:27 PM |
|
Shortcut: solve P = NP and get all the bitcoins you want.  |
|
|
|
|
|
kuroman
|
 |
March 10, 2014, 11:51:56 PM |
|
Shortcut: solve P = NP and get all the bitcoins you want.  well yeah the question in billions of dollars, although I have an idea, but the problem needs to be transformed into a matricial problem or at least Vectorial one, then you can relatively easly solve P = NP with Matrix triangulation or diagonalisation if that works but again meh lol |
|
|
|
|
BADecker
Legendary

 Offline Offline
Activity: 3780
Merit: 1372

|
 |
March 11, 2014, 01:35:31 AM |
|
Hello!
This is just for educational purposes. We know that Satoshi has an enormous amount of bitcoins and that he has not moved them for a long time. I think we also know the bitcoin addresses containing those bitcoins.
What if someone wanted to steal those bitcoins? They would need both the public key and private key of the address. I know that it would take an enormous amount of time but is this technically doable?
Also, would mining pools be able to push to their clients a script to find those public and private keys? These pools have nowadays an enormous calculation power.
The odds are almost infinitely better playing the lottery. But if you can do it, be sure to give them back, so that you can live with yourself.  |
|
|
|
|
Joshuar
|
 |
March 11, 2014, 01:38:40 AM |
|
The easiest way would be to pretend to be Satoshis long lost brother and ask him for a couple quick millions. Should be as simple as that.  |
| ❱❱ | | ██
█║█
║║║
║║║
█║█
██ | | | | |
▄██▄
▄██████▄
▄██████████
▄██████████▀ ▄▄
▄██████████▀ ▄████▄
▄██████████▀ ████████▄
██████████▀ ▀████████
▀███████▀ ▄███▄ ▀████▀ ▄█▄
▄███▄ ▀███▀ ▄███████▄ ▀▀ ▄█████▄
▄███████▄ ▄██████████ ▄█████████
█████████ ▄██████████▀ ▄██████████▀
▀█████▀ ▄██████████▀ ▄██████████▀
▀▀▀ ▄██████████▀ ▄██████████▀
██████████▀ ▄██████████▀
▀███████▀ █████████▀
▀███▀ ▄██▄ ▀█████▀
▄██████▄ ▀▀▀
█████████
▀█████▀
▀▀▀ | | e i d o o
██
| |
▄██▄
▄██████▄
▄██████████
▄██████████▀ ▄▄
▄██████████▀ ▄████▄
▄██████████▀ ████████▄
██████████▀ ▀████████
▀███████▀ ▄███▄ ▀████▀ ▄█▄
▄███▄ ▀███▀ ▄███████▄ ▀▀ ▄█████▄
▄███████▄ ▄██████████ ▄█████████
█████████ ▄██████████▀ ▄██████████▀
▀█████▀ ▄██████████▀ ▄██████████▀
▀▀▀ ▄██████████▀ ▄██████████▀
██████████▀ ▄██████████▀
▀███████▀ █████████▀
▀███▀ ▄██▄ ▀█████▀
▄██████▄ ▀▀▀
█████████
▀█████▀
▀▀▀ | | | | | ██
█║█
║║║
║║║
█║█
██ | | ❰❰ | | |
|
|
|
surfer43
Sr. Member
   
 Offline Offline
Activity: 560
Merit: 250
"Trading Platform of The Future!"

|
 |
March 11, 2014, 02:28:53 AM |
|
[insert infographic here]
Yup. Until we colonize the universe. 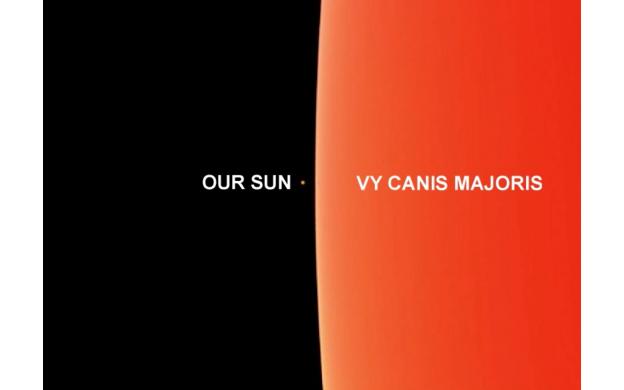 |
|
|
|
|
|
Klestin
|
 |
March 11, 2014, 02:52:58 AM |
|
Wake me up when someone factors 32 bit number using quantum computing. If QC becomes a credible threat Bitcoin can evolve to addresses which use post-quantum cryptography. You. You bring your logic. And your facts. And your basic understanding of cryptography, computing, and the current state of quantum computing development. Did you stop to consider that you were derailing this community's gnashing of teeth over the suuper scaaarey magical quantum computer that's gunna steal all our coins? I'm pretty sure some folks were all ready to set their hair on fire and run around screaming. *Shakes tiny fist* To allay their dismay at the loss of a good panic,  |
|
|
|
|
|
wickedgoodtrader
|
 |
March 11, 2014, 03:01:41 AM |
|
This will just be another thing bitcoin flops on. It's already happened a few times. Everyone says bitcoin is rock solid bullet proof then the next thing ya know the chain is forked and shit is going to hell!
Then transactions are being reversed from gambling sites because a pool has too high % of the network.
Then transactions are being altered so people can rob exchanges all over the place!
Before ya know it there will be some shit with the SHA too. This whole it takes more energy to crack it then exists in the universe or whatever the fuck they are trying to say just ain't gonna fly. I bet Karpales made that picture.
|
|
|
|
|
Syke
Legendary

 Offline Offline
Activity: 3878
Merit: 1193

|
 |
March 11, 2014, 03:04:11 AM |
|
Wait what? did you even read beyond that point? you are partially quoting to prove that you are right is that what you trying to do here? I repeat my self todays computing power 10^15+ so theoritically if classical computing keeps going forward at the same pace it's advanced with since the 60s we will be looking at 10^30 10^40 Flops in the next decade or two which is enough to crack 128bits in a few seconds and we will move on to 10^70 Flops and beyond in another decade or two from there, that is without taking into consideration anything else! which not even remotly true
Obligitory XKCD:  |
Buy & Hold
|
|
|
|
fasmax
|
 |
March 11, 2014, 03:17:15 AM |
|
Is it possible that a backdoor key exists? If a backdoor exists then you could simply compute the private key given the public key and the backdoor key.  |
|
|
|
|
jonald_fyookball
Legendary

 Offline Offline
Activity: 1302
Merit: 1004
Core dev leaves me neg feedback #abuse #political

|
 |
March 11, 2014, 03:35:27 AM |
|
Is it possible that a backdoor key exists? If a backdoor exists then you could simply compute the private key given the public key and the backdoor key.  I think it's possible, but how likely I don't know. Seems unlikely because cryptography experts would have probably tuned the larger bitcoin community into the risk of that, and there would be more chatter of developing alternate hashing algorithms. If there is a backdoor it's a closely guarded secret that no one has seen any evidence of. |
|
|
|
|
kthejung
|
 |
March 11, 2014, 04:32:00 AM |
|
You have all missed the obvious: invent a time machine and go back to 2009, intercept Satoshi's usb drive containing private keys after he mines the genesis blocks, and then steal his Danish butter cookies.  |
|
|
|
|
|
Nathonas
|
 |
March 11, 2014, 04:58:48 AM |
|
|
All we have to decide is what to do with the time that is given us.
|
|
|
Buffer Overflow
Legendary

 Offline Offline
Activity: 1652
Merit: 1015

|
 |
March 11, 2014, 11:26:02 AM |
|
This will just be another thing bitcoin flops on. It's already happened a few times. Everyone says bitcoin is rock solid bullet proof then the next thing ya know the chain is forked and shit is going to hell!
Then transactions are being reversed from gambling sites because a pool has too high % of the network.
Then transactions are being altered so people can rob exchanges all over the place!
Before ya know it there will be some shit with the SHA too. This whole it takes more energy to crack it then exists in the universe or whatever the fuck they are trying to say just ain't gonna fly. I bet Karpales made that picture.
Perhaps crypocurrencies aren't your thing then. Maybe play a different game. |
|
|
|
|
kuroman
|
 |
March 11, 2014, 01:36:23 PM |
|
Wait what? did you even read beyond that point? you are partially quoting to prove that you are right is that what you trying to do here? I repeat my self todays computing power 10^15+ so theoritically if classical computing keeps going forward at the same pace it's advanced with since the 60s we will be looking at 10^30 10^40 Flops in the next decade or two which is enough to crack 128bits in a few seconds and we will move on to 10^70 Flops and beyond in another decade or two from there, that is without taking into consideration anything else! which not even remotly true
Obligitory XKCD:  Yeah lol, people do that mistake alot when extrapolating, but when you have 5-6 decades of data I believe it is safe to make an extention to the next decade or two, considering, that we've already know what's coming up in the next few year (example 2014, Intel moving to 14nm, and the other Fonderies to 20nm and under when it comes to CPU (production has already started), 2016 10nm with prototypes already existing in Intels labs for example and being tuned for production, everything Graphen related and nanotubes is already in labs all over the world being tested, enhanced and more importantly, starting to get an industrial orientation (production unites, process, and what's not) as for Quantum computing we are already doing the first baby steps in this area, commercial availability to develop software and firmware and alghorithms.... |
|
|
|
|
Syke
Legendary

 Offline Offline
Activity: 3878
Merit: 1193

|
 |
March 12, 2014, 06:01:51 PM |
|
Yeah lol, people do that mistake alot when extrapolating, but when you have 5-6 decades of data I believe it is safe to make an extention to the next decade or two
Go ahead. Extrapolate a decade or two. In fact, go ahead and extrapolate to the theoretically limits of the perfect computer harnessing the entire energy of the sun. You still can't even count to 2^256, let alone do the calcuations to brute force a Bitcoin private key. Re-read the graphic in post #2. |
Buy & Hold
|
|
|
Mensa
Newbie

 Offline Offline
Activity: 15
Merit: 0

|
 |
March 12, 2014, 06:36:26 PM |
|
One Does Not Simply Steal Satoshi's Stash.
|
|
|
|
|
bountygiver
Member
 
 Offline Offline
Activity: 100
Merit: 10

|
 |
March 12, 2014, 06:48:16 PM |
|
You have all missed the obvious: invent a time machine and go back to 2009, intercept Satoshi's usb drive containing private keys after he mines the genesis blocks, and then steal his Danish butter cookies.  Or you can travel to the future where quantum computers work and bitcoin became obsolute because of that, compute his private key, return to original time and move all the funds. |
12dXW87Hhz3gUsXDDCB8rjJPsWdQzjwnm6
|
|
|
MoneyShot2
Member
 
 Offline Offline
Activity: 119
Merit: 10

|
 |
March 12, 2014, 07:27:49 PM |
|
Anyone is better off solo mining and hoping to find 10 000 blocks in a row than to crack priv keys.
|
▄▄▄▄▄▄▄
▄▄▄▄
▄▄ 【BTC】
|
|
|
jonald_fyookball
Legendary

 Offline Offline
Activity: 1302
Merit: 1004
Core dev leaves me neg feedback #abuse #political

|
 |
March 12, 2014, 08:03:50 PM |
|
One Does Not Simply Steal Satoshi's Stash.
Post the meme image please |
|
|
|
krampus
Member
 
 Offline Offline
Activity: 98
Merit: 10
Village Idiot

|
 |
March 12, 2014, 08:04:11 PM |
|
Yeah lol, people do that mistake alot when extrapolating, but when you have 5-6 decades of data I believe it is safe to make an extention to the next decade or two, considering, that we've already know what's coming up in the next few year (example 2014, Intel moving to 14nm, and the other Fonderies to 20nm and under when it comes to CPU (production has already started), 2016 10nm with prototypes already existing in Intels labs for example and being tuned for production, everything Graphen related and nanotubes is already in labs all over the world being tested, enhanced and more importantly, starting to get an industrial orientation (production unites, process, and what's not) as for Quantum computing we are already doing the first baby steps in this area, commercial availability to develop software and firmware and alghorithms....
The only thing more annoying than idiots are idiots that think they're smart. You, sir, are an idiot. No amount of technobabble (that you no doubt read somewhere on Gizmodo) is going to convince the actually smart people in the room that you have any idea what you're talking about. Best thing to do at this point is just to shut the fuck up, lest you look any stupider than you already do. You're welcome. |
I pledge never to use this space for sleazy referrals, gambling spam, or to beg for handouts.
|
|
|
HowGudAmI
Sr. Member
   
 Offline Offline
Activity: 294
Merit: 250
BTC --> ??? --> PROFIT

|
 |
March 12, 2014, 08:07:48 PM |
|
One Does Not Simply Steal Satoshi's Stash.
Post the meme image please  http://imgur.com/aSH3OeV.jpg http://imgur.com/aSH3OeV.jpg |
|
|
|
|
kuroman
|
 |
March 12, 2014, 08:55:43 PM
Last edit: March 12, 2014, 09:10:59 PM by kuroman |
|
Go ahead. Extrapolate a decade or two. In fact, go ahead and extrapolate to the theoretically limits of the perfect computer harnessing the entire energy of the sun. You still can't even count to 2^256, let alone do the calcuations to brute force a Bitcoin private key. Re-read the graphic in post #2.
The only extrapolation I would do is to refer you to my previous comment, Ok I'll be helpfull and quote my self since you didn't bother to read the previous pages. Feel free to list your counter arguments but just for the sake of not repeating our selfs I'll advise to read previous posts, because I'm pretty sure you'll ask similar questions that were asked previously and been replied. You (like most people) have difficulty grasping how large 2^256 is (or even 2^128 which is the effective security of 256 bit ECDSA keys). The 128 bit or 256 bit seems deceptively small. As a math literate person I do gasp how huge 2^256 is. Nobody credible is saying classical computers could brute force keys in thousands of years..... it would be billions of years using all the energy of our sun. That also assumes you have a perfect computer. And I do agree with this as in TODAY, the math is simple, our most powerfull supercomputers calculates in 30sh PFlops that's about 30x10^15 Flops Time in year = 3600x(24x365+6) = 31557600s and 2^256 ~ 1.14x10^77 so it will take to crack it with the usumption that it will require 100Flops per combination = 1.14x10^79/(31557600x30x10^15) =~ 1.20x10^55 years ! BUT THAT'S NOT THE POINT! My point is if you consider only classical computing in the last 30 years we've moved from KiloFlops to PentaFlops or 10^15Flops in terms of processing power, it is easy to assume that in the next few decades, we can easly achieve 10^30 / 10^40 (we've already gone past the point of cracking 2^128 or 128bits in a few seconds) and it will reach eventually 10^70+. In the 80/90s people (like you) were claiming 56 bit encryption was impossible to crack, and you know what, it takes like 3s and less to break with our current supercomputers! And this doesn't take into consideration Alghorithm break trought as I mentioned, even the current classic computer with the proper alghorithms can simulate Quantum computers and have similar results in some areas for example......... Now if you add in the mix Quantum computing which will bring computing to a whole other level as the potentiel from a dozen of Qubit and the impact they have is already being proven. None of those (except QC) would do anything more than switching from a teaspoon to a bucket when trying to empty an ocean. Wrong as proven above. a) The private key isn't random enough (insufficient entropy due to flaw in PRNG)
b) ECDSA is cryptographically weakened/broken.
c) It becomes possible to build a QC with the tens of thousands of qubits necessary to implement Shor's algorithm against a 256 bit ECDSA public key (and public key is known).
It's not limited to this as proven above but : a = Possible as proven with AES thanks to NSA Middeling b = Possible c = it will happen in the next decade or the one folowing, considering we've moved from 4 Qubits to 128 in a very short laps of time heck Dwave just released a 512 Qbits Processor and they claim to have a 1000 Qubits in their lab ready to roll http://www.washingtonpost.com/blogs/the-switch/wp/2014/01/10/this-company-sold-google-a-quantum-computer-heres-how-it-works/Also the Shor Alghorithm is not the most efficient Alghrorithm beyond 600 Qubits in comparaison to Fourier Transform On one hand factoring and calculation logs and the other the usual linear transform that can be decomposed to I or Unitary Matrix, which Qubits likes.
The only thing more annoying than idiots are idiots that think they're smart.
You, sir, are an idiot. No amount of technobabble (that you no doubt read somewhere on Gizmodo) is going to convince the actually smart people in the room that you have any idea what you're talking about. Best thing to do at this point is just to shut the fuck up, lest you look any stupider than you already do.
You're welcome.
I was going to ignore your comment, but I decided to reply to it. Anyway, I doubt someone who understands math, physics, engineering, cryptography is an idiot. Even if it doesn't matter, I have a Bachelor degree in fundamental physics, a Master degree in Mechanical Engineering, a European Masters in Management and Business Strategy and also preparing a PhD if you doubt these I'm ready to provide all the necessary proves if you are ready to bet some BTCs Escrowed of course! So before calling other people Idiots and stupid without having the minimum skills to understand what they are saying please look at your mirror, you might have a hint. As for the others I really apology for this little rant, because I believe that bitcointalk in general and this section in particular is not for epen contest, and I agree I should've just ignored, but sometimes you are in that day when you are a bit edgy. |
|
|
|
|
jonald_fyookball
Legendary

 Offline Offline
Activity: 1302
Merit: 1004
Core dev leaves me neg feedback #abuse #political

|
 |
March 12, 2014, 09:31:56 PM
Last edit: March 12, 2014, 09:49:54 PM by jonald_fyookball |
|
I have a Bachelor degree in fundamental physics, a Master degree in Mechanical Engineering, a European Masters in Management and Business Strategy and also preparing a PhD
Someone as smart and educated as yourself should be the first to acknowledge that there are limitations inherent in the physical universe in which we live. Saying we're eventually going to get to 10^70 flops seems like an insane comment that denies such a truth. |
|
|
|
krampus
Member
 
 Offline Offline
Activity: 98
Merit: 10
Village Idiot

|
 |
March 12, 2014, 09:43:46 PM |
|
I have a Bachelor degree in fundamental physics, a Master degree in Mechanical Engineering, a European Masters in Management and Business Strategy and also preparing a PhD And yet you're still an idiot. Further proof that education doesn't make you smart. I've worked in the computer industry for several decades. Everybody in this industry knows that Moore's Law is an observation of a trend, not a fundamental guarantee of future performance. And everyone knows that the constraints of physics (which you yourself claim to hold a degree in) will put a halt to that trend. But I'm not going to try to convince you of these fundamental truths, or try to explain the math to you. Trying to educate educated idiots is a provably obvious waste of time. I'm just going to point out what a stupid fuckwit you are and be done with it. Oh, but I will give you a tip: smart people know how to recognize people smarter than themselves. This is a critical differentiator between idiots and smart people. |
I pledge never to use this space for sleazy referrals, gambling spam, or to beg for handouts.
|
|
|
jonald_fyookball
Legendary

 Offline Offline
Activity: 1302
Merit: 1004
Core dev leaves me neg feedback #abuse #political

|
 |
March 12, 2014, 09:48:47 PM |
|
I've worked in the computer industry for several decades. Everybody in this industry knows that Moore's Law is an observation of a trend, not a fundamental guarantee of future performance.
Well said. |
|
|
|
MoneyShot2
Member
 
 Offline Offline
Activity: 119
Merit: 10

|
 |
March 12, 2014, 09:51:49 PM |
|
|
▄▄▄▄▄▄▄
▄▄▄▄
▄▄ 【BTC】
|
|
|
|
S4VV4S
|
 |
March 12, 2014, 10:44:10 PM |
|
I have a Bachelor degree in fundamental physics, a Master degree in Mechanical Engineering, a European Masters in Management and Business Strategy and also preparing a PhD And yet you're still an idiot. Further proof that education doesn't make you smart. I've worked in the computer industry for several decades. Everybody in this industry knows that Moore's Law is an observation of a trend, not a fundamental guarantee of future performance. And everyone knows that the constraints of physics (which you yourself claim to hold a degree in) will put a halt to that trend. But I'm not going to try to convince you of these fundamental truths, or try to explain the math to you. Trying to educate educated idiots is a provably obvious waste of time. I'm just going to point out what a stupid fuckwit you are and be done with it. Oh, but I will give you a tip: smart people know how to recognize people smarter than themselves. This is a critical differentiator between idiots and smart people. Can I also add that smart people want to hang out with smarter people in order to get smarter? |
|
|
|
|
|
kuroman
|
 |
March 12, 2014, 11:10:40 PM
Last edit: March 12, 2014, 11:49:10 PM by kuroman |
|
Someone as smart and educated as yourself should be the first to acknowledge that
there are limitations inherent in the physical universe in which we live.
Saying we're eventually going to get to 10^70 flops seems like an insane comment
that denies such a truth.
This was answered before and I'll answer this again 10^70Flops is something inconceivable today! I don't think we disagree with this point, and I've been repeating this for a dozens of times, today we cannot brute force a 256bit encryption heck not even close to 128bit this is not even a point. Where we disagree is in terms of future prospect. In the beginning of the 80s (I provided the numbers) Supercomputers were calculating the KiloFlops or 10^3 Flops! todays 10^16 Flops was inconceivable at the time, 56bit encryptions in the 80s and 90s were in that aspect impossible to crack and it would have taken Billions upon billions upon billions of years with the computing time, Today a supercomputer like the Tianhe-2 could crush in less than 3s (I can provide the math for the above if needed, as I did before.) in a similar way our computing power will move on in the next few decades and eventually it will reach a similar point to what is happening to 56bit encryption. This is how science progress, and this is not limited to computing (while there is a reason tech is the are that progressing the fastest, being geopolitical reasons, economic reasons, defense reasons.....) Lets just see other science domains, for example the size of the universe, in the beginning of the 1900s we taught the universe was limited to the milky way, a few years we learned that milky-way is just one of many galaxies and today we know that only in the observable universe we have trillions of galaxies and it's the same story for any other field I can go on with this but it's not the point. tl,dr: brute forcing a private key being it 128bit or 256bit is impossible today it's stupid to even try, and I've already provided the math for this and we do not disagree on this, my point is, in the next few decades we will eventually reach the point where we will have enough computing power to be able to do so as happened in the past!
And yet you're still an idiot. Further proof that education doesn't make you smart.
I've worked in the computer industry for several decades. Everybody in this industry knows that Moore's Law is an observation of a trend, not a fundamental guarantee of future performance. And everyone knows that the constraints of physics (which you yourself claim to hold a degree in) will put a halt to that trend.
But I'm not going to try to convince you of these fundamental truths, or try to explain the math to you. Trying to educate educated idiots is a provably obvious waste of time. I'm just going to point out what a stupid fuckwit you are and be done with it.
Oh, but I will give you a tip: smart people know how to recognize people smarter than themselves. This is a critical differentiator between idiots and smart people.
Convince me? with what? Insults? please tell me/us, because so far it seems to be the only thing you are able to do, no argumentation, no facts, not able to maintain a proper conversation as a civilized person, I'm just going to point out what a stupid fuckwit you are and be done with it Are you twelve ? You are making yourself looks worst and worst, so again where are your proves? where are your facts? your arguments? weren't you calling me an uneducated idiot in your previous comment? what's happened to that? Just one last peace of advice since you seem to be concerned about your e-ego more than anything else which is the biggest vice of someone who wants to learn a few things which is of course the total opposite of intelligence, just take a few seconds to reflect and leave your e-ego for youtube comments or something where everyone there is an expert... (And I believe we all are here in bitcointalk to learn a thing or two being it in terms of cryptocurrency, trading .....ect or just to talk to people from different cultures) . |
|
|
|
|
|
lnternet
|
 |
March 12, 2014, 11:38:27 PM |
|
Just one last peace of advice since you seem to be concerned about your e-ego more than anything else lol |
1ntemetqbXokPSSkuHH4iuAJRTQMP6uJ9
|
|
|
|
Cheena
|
 |
March 12, 2014, 11:47:33 PM |
|
You cannot steal my stash.
Regards
Satoshi Nakamoto
|
HODL !
|
|
|
Syke
Legendary

 Offline Offline
Activity: 3878
Merit: 1193

|
 |
March 12, 2014, 11:56:14 PM |
|
tl,dr: brute forcing a private key being it 128bit or 256bit is impossible today it's stupid to even try, and I've already provided the math for this and we do not disagree on this, my point is, in the next few decades we will eventually reach the point where we will have enough computing power to be able to do so as happened in the past!
I'll let Bruce educate you. One of the consequences of the second law of thermodynamics is that a certain amount of energy is necessary to represent information. To record a single bit by changing the state of a system requires an amount of energy no less than kT, where T is the absolute temperature of the system and k is the Boltzman constant. (Stick with me; the physics lesson is almost over.)
Given that k = 1.38×10-16 erg/°Kelvin, and that the ambient temperature of the universe is 3.2°Kelvin, an ideal computer running at 3.2°K would consume 4.4×10-16 ergs every time it set or cleared a bit. To run a computer any colder than the cosmic background radiation would require extra energy to run a heat pump.
Now, the annual energy output of our sun is about 1.21×1041 ergs. This is enough to power about 2.7×1056 single bit changes on our ideal computer; enough state changes to put a 187-bit counter through all its values. If we built a Dyson sphere around the sun and captured all its energy for 32 years, without any loss, we could power a computer to count up to 2192. Of course, it wouldn't have the energy left over to perform any useful calculations with this counter.
But that's just one star, and a measly one at that. A typical supernova releases something like 1051 ergs. (About a hundred times as much energy would be released in the form of neutrinos, but let them go for now.) If all of this energy could be channeled into a single orgy of computation, a 219-bit counter could be cycled through all of its states.
These numbers have nothing to do with the technology of the devices; they are the maximums that thermodynamics will allow. And they strongly imply that brute-force attacks against 256-bit keys will be infeasible until computers are built from something other than matter and occupy something other than space.
No, it's not going to happen in a few decades. It will never happen. |
Buy & Hold
|
|
|
krampus
Member
 
 Offline Offline
Activity: 98
Merit: 10
Village Idiot

|
 |
March 13, 2014, 12:34:01 AM |
|
Are you twelve ? You are making yourself looks worst and worst, so again where are your proves? where are your facts? your arguments? weren't you calling me an uneducated idiot in your previous comment? what's happened to that? Re-read my post. I'm not offering any "proves" or facts. It would be a monumental waste of effort, since several people (who are probably smarter than me) have already tried to explain the basics to you right here in this thread. You dismissed them out of hand, without even a very good rationale for doing so. Why would I offer insight to someone who clearly isn't interested in it? What kind of an idiot would I be if I took that particular bait? Nope. Not going to do it. I understand the problem in ways that you clearly don't, and I'm utterly un-interested in trying to "help" you. You're a willful fucking idiot, and I'm quite happy to let you go on being a willful fucking idiot for the rest of your stupid life. Ta-ta! |
I pledge never to use this space for sleazy referrals, gambling spam, or to beg for handouts.
|
|
|
jonald_fyookball
Legendary

 Offline Offline
Activity: 1302
Merit: 1004
Core dev leaves me neg feedback #abuse #political

|
 |
March 13, 2014, 12:38:44 AM
Last edit: March 13, 2014, 01:57:33 AM by jonald_fyookball |
|
This was answered before and I'll answer this again 10^70Flops is something inconceivable today! I don't think we disagree with this point, and I've been repeating this for a dozens of times, today we cannot brute force a 256bit encryption heck not even close to 128bit this is not even a point.
Where we disagree is in terms of future prospect.
Dude...bro... You are STILL missing the freaking point! No one is questioning the advancement of technology or even our ability to predict...but its essentially PHYSICALLY IMPOSSIBLE to make a computer that would do 10^70 FLOPS. Let's do the math, shall we: 1. size of atom is roughly 0.0000000000001 meters ...therefore... 2. Number of atoms in a meter = 10^13 3. Number of atoms you could fit into a cubic meter = 10^39 ...also... 4. speed of light = 299,792,458 metres per second ...thus... 5. time required for light to travel the distance of 1 meter = 1/299792458 seconds = .000000003335 seconds. 6. time required for light to travel the length of 1 atom = 0.000000000000000000003335 seconds. 7. If SOMEHOW, in this tiny timeframe, a floating point operation could be done using the space of a single atom, you would get 2.99*10^20 FLOPS for each atom-size "bit". (take the reciprocal of the above number) 8. So a cubic-meter sized computer filled with atoms back to back, each calculating at the speed of light would still only get you 2.99 *10^59 FLOPS. 9. to get to 10^70, you would need 33 billion of these cubic meters sized computers. Stacked end to end, these cubes would go to the moon and back 42 times. See, it always comes down to the answer: 42. |
|
|
|
|
kuroman
|
 |
March 13, 2014, 12:57:50 AM |
|
I'll let Bruce educate you. One of the consequences of the second law of thermodynamics is that a certain amount of energy is necessary to represent information. To record a single bit by changing the state of a system requires an amount of energy no less than kT, where T is the absolute temperature of the system and k is the Boltzman constant. (Stick with me; the physics lesson is almost over.)
Given that k = 1.38×10-16 erg/°Kelvin, and that the ambient temperature of the universe is 3.2°Kelvin, an ideal computer running at 3.2°K would consume 4.4×10-16 ergs every time it set or cleared a bit. To run a computer any colder than the cosmic background radiation would require extra energy to run a heat pump.
Now, the annual energy output of our sun is about 1.21×1041 ergs. This is enough to power about 2.7×1056 single bit changes on our ideal computer; enough state changes to put a 187-bit counter through all its values. If we built a Dyson sphere around the sun and captured all its energy for 32 years, without any loss, we could power a computer to count up to 2192. Of course, it wouldn't have the energy left over to perform any useful calculations with this counter.
But that's just one star, and a measly one at that. A typical supernova releases something like 1051 ergs. (About a hundred times as much energy would be released in the form of neutrinos, but let them go for now.) If all of this energy could be channeled into a single orgy of computation, a 219-bit counter could be cycled through all of its states.
Thanks refresh on the basics thermodynamics, The calculation is a bit off and pretty simplistic and in fact the amount of energy needed is more than that, but again that calculation is only taking into consideration TODAYS computing power and we are just repeating our selfs here,And I don't understand what you don't get here, there is no point on starting a computation today to do such a thing and this what the argument above is presenting no more no less. the minimum amount of time needs is in the order of 10^55 years, in by the second law of themodynamics by that time there will be nothing left in the universe not a single star the only things left would be blackholes and even those will eventually start evaporating (degenerescence or blackhole era) Anyway let me simplify things since a lot of people seems to be confused here: Just to put things in a human scale, let's assume that there are no oceans and you can "walk" all the way between continents, a few centuries ago, it would be impossible to go around the world (objective here to go around the world at the equator 10 times) and at the period the best you can do on ground is walking/running using horses and as we can it was impossible to come even close to a faction of the necessary distance to achieve the objective (the circumference of earth at the equator is 40 075,017, and your speed won't exceed an average of 5km an hour it's easy to see the issue here we are talking easily millennias ). Today, it take the International space station around 90min to orbit the earth so 10 orbits should take around 15hrs.
brute-force attacks against 256-bit keys will be infeasible until computers are built from something other than matter and occupy something other than space.
This is totally wrong, and it is your own misinterpretation, and you are welcome to quote the exact word they used. I'm pretty sure what they mean is that with todays technology to be able to brute force against 256bit you'll need a computer of a size bigger than the universe (which is to say yet again Impossible!) I'll also invite you just for the sake of reference, to check the 80s tech and security magazines if you have access to those in your city library and check what they were saying about 56bit encryption at the time, you'll be really surprised on how the argument you are advancing are similar if not the same of what was said at the time. |
|
|
|
|
DeathAndTaxes
Donator
Legendary

 Offline Offline
Activity: 1218
Merit: 1079
Gerald Davis

|
 |
March 13, 2014, 01:17:49 AM |
|
brute forcing a private key being it 128bit or 256bit is impossible today it's stupid to even try, and I've already provided the math for this and we do not disagree on this, my point is, in the next few decades we will eventually reach the point where we will have enough computing power to be able to do so as happened in the past! No we won't. You seem to vastly underestimate how large 10^70, 2^128, and 2^160 are. In 40 years Moore's law has provided roughly 1*10^6 improvement in transistor density and a roughly comparable improvement in cost per unit of computing power and power per unit of computing power. It is highly likely that Moore's law will not be sustained for another 40 years, Intel may actually slip below that "benchmark" for the first in this decade. The cost to build smaller and smaller process nodes is increasing exponentially and the time between process nodes (which should be no more than 24 months) is slowly inching upward. Lets not even get into the fact that there are only 8 maybe 9 process nodes before we get down to the transistors using 3 atoms a piece. Still lets assume that an equivalent amount of improvement occurs over the next 4 decades. That is a ~10^6. Today top supercomputers are PFLOP scale. Lets ignore the fact that Integer performance is often a magnitude worse and that it takes tens of thousands of operations to complete a single keypair (and even more to perform lookups). Lets just naively assume that 1 ECDSA key generation and lookup can be done in 1 FLOP (which doesn't even make sense but trying to be ultra conservative). That would mean today a top super computer could do ~34 PK/s (peta keys per second). To keep the math simple lets just round up to 100 PK/s or 1*10^17 kps. If we then assume a 1*10^6 factor improvement in relative performance in the next 40 years that would make a top SC something on the order of 1*10^23 kps. Now lets assume you build one for every man woman and child on the planet (estimated to be ~10 B in 2054). That would put world wide key breaking power at 1*10^33 kps. You aren't even within the same ballpark as 10^70. In reality performance will probably slip below Moore's law, you can't process on key per clock cycle, and even if you could we are looking at an energy requirement greater than what is used by the entire human race for all other purposes. |
|
|
|
|
|
porcupine87
|
 |
March 13, 2014, 01:20:31 AM |
|
This is totally wrong, and it is your own misinterpretation, and you are welcome to quote the exact word they used. I'm pretty sure what they mean is that with todays technology to be able to brute force against 256bit you'll need a computer of a size bigger than the universe (which is to say yet again Impossible!)
I can understand your point. A few centuries ago things seemed to be so far away like today breaking a 256 bit key. Although it is funny to watch a documentary from 1970 "how will the year 2000 look like?". No, we are not flying with cars around and no, we have no 15h weeks  I am on your side, that we never know what the future brings. But the statement from "Bruce" has nothing to do with "today's technology". He just makes the assumption that you need energy to represent information. To turn around a bit. Without that you cannot count or calculate. You need energy. And in our solar system we have a limited amount of energy (to a given time). So when you use all the energy of the solar system over its whole life span, you still have not enough energy to count to 2^256. This has nothing to do with today's technology. Again: The statement is about energy, which you need for counting and energy is limited. |
"Morality, it could be argued, represents the way that people would like the world to work - whereas economics represents how it actually does work." Freakonomics
|
|
|
DeathAndTaxes
Donator
Legendary

 Offline Offline
Activity: 1218
Merit: 1079
Gerald Davis

|
 |
March 13, 2014, 01:21:14 AM
Last edit: March 13, 2014, 01:50:50 AM by DeathAndTaxes |
|
Thanks refresh on the basics thermodynamics, The calculation is a bit off and pretty simplistic and in fact the amount of energy needed is more than that, but again that calculation is only taking into consideration TODAYS computing power. How about you read what was written? It was talking about a PERFECT computer (a theoretical construct), not a computer built today, or one built with technology a century from now but one which operates at the thermodynamic limit and in roughly absolute zero. Nothing more efficient is possible. It is many quadrillions of times more efficient than today's computers. The human race may never build a perfect classical computer but it is often used as an upper bound as it takes into account all possible performance increases. Not only does the example use a perfect computer but it is powered using the entire output of our star for the next four billion years or so. The example was just counting (i.e. 1 bit flip per increment). Generating a single ECDSA key involves tens of thousands of operations and each of those involve hundreds of bits so even for a perfect computer it is something on the order of millions of bit flips per ECDSA key and thus the power requirements would be millions of times higher. Keys of 128 bit strength are unbreakable by brute force on a classical computer (even a perfect one). This doesn't mean they can never be broken but it will be because of: a) a break in the algorithm itself b) it becomes possible to implement Shor's algorithm against 256 bit keys using a quantum computer. c) implementation attack (flawed RNG, backdoor in processor, etc) None of that has anything to do with your false claim that Moore's law will make classical computers fast enough to break 128 bit keys in a few decades. Please find a single cite for any reputable cryptography who shares your opinion. |
|
|
|
|
Bigeyeone
Member
 
 Offline Offline
Activity: 112
Merit: 10

|
 |
March 13, 2014, 01:24:54 AM |
|
Anyone took in consideration you dont actually loose energy when you flip a bit ?
A processor just converts electric energy into heat energy . in theorie technology could be developed to convert all the heat back into electricity. it already exists , it is just not very efficient at the moment.
|
PMC: 19dNRVPcjsESqo8isdauc1gQ6PbUrAZor9
|
|
|
criptix
Legendary

 Offline Offline
Activity: 2464
Merit: 1145

|
 |
March 13, 2014, 01:52:59 AM |
|
until we discover new laws of nature and physics  Anyone took in consideration you dont actually loose energy when you flip a bit ?
A processor just converts electric energy into heat energy . in theorie technology could be developed to convert all the heat back into electricity. it already exists , it is just not very efficient at the moment.
we would still need alot of space then... |
|
|
|
|
kuroman
|
 |
March 13, 2014, 01:54:06 AM |
|
Anyone took in consideration you dont actually loose energy when you flip a bit ?
A processor just converts electric energy into heat energy . in theorie technology could be developed to convert all the heat back into electricity. it already exists , it is just not very efficient at the moment.
While this is true, the second law of thermodynamics doesn't allow it or rather you can't do it indefinitly |
|
|
|
|
|
kuroman
|
 |
March 13, 2014, 02:22:24 AM |
|
Dude...bro... You are STILL missing the freaking point!
No one is questioning the advancement of technology
or even our ability to predict...but its essentially
PHYSICALLY IMPOSSIBLE to make a computer that
would do 10^70 FLOPS.
Let's do the math, shall we:
1. size of atom is roughly 0.0000000000001 meters
...therefore...
2. Number of atoms in a meter = 10^13 not necessary but lets assume so
3. Number of atoms in a cubic meter = 10^39
...also...
4. speed of light = 299,792,458 metres per second
...thus...
5. time required for light to travel the distance of 1 meter =
1/299792458 seconds = .000000003335 seconds.
6. time required for light to travel the length of 1 atom =
0.000000000000000000003335 seconds.
7. If SOMEHOW, in this tiny timeframe,
a floating point operation could be
done using the space of a single atom,
you would get 2.99*10^20 FLOPS for each atom-size "bit".
(take the reciprocal of the above number)
8. So a cubic-meter sized computer filled with atoms
back to back, each calculating at the speed of light
would still only get you 2.99 *10^59 FLOPS.
9. to get to 10^70, you would need 33 billion of these
cubic meters sized computers. Stacked end to end, these cubes
would go to the moon and back 42 times.
See, it always comes down to the answer: 42.
I'm not going trough all the zeros not because it's not interesting, but because it hurt my eyes, please use Exponentiation. Just to answer you claim above I just have one question : between the nucleus and and the electrons what do we have?, and inside the nucleus between Quarks what do we have? and what is the scale of this thing in comparison of real stuff there, maybe you understand what I'm getting at by now, because you made a hypothesis above about the possible number of atoms in cubic meter. Also another thing that picked my attention which is 2.99 *10^59 FLOPS so for you this number seems to be fine right? You agree that this number is more than enough to brute force 128bit AES almost instantly right? ok do you know the link between 256bit ECDSA in private key and 128bit AES?
No we won't. You seem to vastly underestimate how large 10^70, 2^128, and 2^160 are.
In 40 years Moore's law has provided roughly 1*10^6 improvement in transistor density and a roughly comparable improvement in cost per unit of computing power and power per unit of computing power. It is highly likely that Moore's law will not be sustained for another 40 years, Intel may actually slip below that "benchmark" for the first in this decade. The cost to build smaller and smaller process nodes is increasing exponentially and the time between process nodes (which should be no more than 24 months) is slowly inching upward. Lets not even get into the fact that there are only 8 maybe 9 process nodes before we get down to the transistors using 3 atoms a piece.
Still lets assume that an equivalent amount of improvement occurs over the next 4 decades. That is a ~10^6. Today top supercomputers are PFLOP scale. Lets ignore the fact that Integer performance is often a magnitude worse and that it takes tens of thousands of operations to complete a single keypair (and even more to perform lookups). Lets just naively assume that 1 ECDSA key generation and lookup can be done in 1 FLOP (which doesn't even make sense but trying to be ultra conservative). That would mean today a top super computer could do ~34 PK/s (peta keys per second). To keep the math simple lets just round up to 100 PK/s or 1*10^17 kps.
If we then assume a 1*10^6 factor improvement in relative performance in the next 40 years that would make a top SC something on the order of 1*10^23 kps. Now lets assume you build one for every man woman and child on the planet (estimated to be ~10 B in 2054). That would put world wide key breaking power at 1*10^33 kps. You aren't even within the same ballpark as 10^70.
In reality performance will probably slip below Moore's law, you can't process on key per clock cycle, and even if you could we are looking at an energy requirement greater than what is used by the entire human race for all other purposes.
I've already made a more precise calculus in my previous post about, but lets take your calculus for the moment The 10^6 factor of improvement is wrong, is the minimum of current improvement is between 10^3 and 10^4 per decade (I'll invite you to check the list of the top supercomputers in the world and approve this fact by yourself (again we are talking about classical computing we aren't even considering QC for example) We also agree that Moors law in electronics has it limits due the Quantum effects at the small scale, let me just remind you that Flops != transistor count, it's one of many facture, such architecture, alghorithms and firmwires....ect ect but this is just a side note) . 10^17KPS is your initial point right? with a factor of improvement between 10^3 and 10^4 per decade, lets just say 2 decades of 10^4 and 2 others 10^3 in over the 4 decades you took as an example, we should have an improvement of 10^14 so we will have by then (if we assume only classic computing which is by then would be obsolete in my opinion anyway we are at 10^30+ (and this is something I've already mentioned in my initial comment, and this is goes with what I said in my previous comments and I'm pretty sure it was a reply to you " in the next few decades, we will reach 10^30-10^40Flops which is more than to crach 128Bit AES in a few seconds, and we will eventually reach 10^70+" And like I said before this just considering classical computing, which will become obsolete in the next decade or two, at least in terms of supercomputing |
|
|
|
|
DeathAndTaxes
Donator
Legendary

 Offline Offline
Activity: 1218
Merit: 1079
Gerald Davis

|
 |
March 13, 2014, 02:41:54 AM |
|
The example provided was as extreme as I could get
1) assumes 1 key per FLOP (more like 1 key per 80,000 integer ops)
2) assumes moore's law will continue for 40 years (20 if we are lucky)
3) assumes 1 super computer per human on the planet (really)
Even that would be insufficient. Yet you still stick with a belief that 10^70 is realistic. There are only 10^50 atoms on the planet. Even assuming terrahertz scale processor you would need to convert the entire planet into chips and then magically process billions of operations per atom. What is going to power this? Where are all the organic life going to go?
Feel free to have the last (delusional) word. I won't see it because it isn't worth my time anymore. You can have your own opinions but you can't have your own facts. 128 bit keys are beyond brute force with classical computing. It doesn't matter if it is today, next decade, next millennium, or using a perfect computer and all the matter and energy in our solar system.
|
|
|
|
|
jonald_fyookball
Legendary

 Offline Offline
Activity: 1302
Merit: 1004
Core dev leaves me neg feedback #abuse #political

|
 |
March 13, 2014, 02:47:40 AM |
|
Wake me up when there's quark based computers and free energy generators... Until then, I'm done with this debate. Cheers.  |
|
|
|
|
googlemaster1
|
 |
March 13, 2014, 02:49:03 AM |
|
Sometimes I just go to directory.io and type in a random page number in the morning.... its like playing the lottery.... except your odds are infinitely worse (quite literally), but hey, YOU NEVER KNOW!
|
BTC: 15565dcUp4LEWe6KYT7tawMHFRL4cBbFGN
|
|
|
|
tl121
|
 |
March 14, 2014, 03:34:10 AM |
|
Here are some links to subjects discussed in this thread. 1. The 56 bit key used in the original NBS data encryption standard was known to be inadequate shortly after the standard was published, as this 1977 paper by Whit Diffie and Marty Hellman demonstrated: http://vanilla47.com/PDFs/Cryptography/Cryptoanalysis/Exhaustive%20Cryptoanalysis%20of%20the%20NBS%20data%20encryption%20standards.pdf
2. Some people have claimed that it would take too much energy to calculate private keys from public keys or to reverse hash algorithms used in constructing bitcoin addresses or mining. That's true in an engineering sense based on today's technology, but not in a physical sense. Many years ago it was believed that the laws of thermodynamics set minimum energy limits on computation, but this was found to not be the case. The minimum energy requirements apply to computations that are not reversible, but if the computation can be reversible, there is no theoretical minimum energy required, other than the small amount of energy to copy out the final answer so it won't be erased when the computation is reversed. As the references cited in the linked article indicate, it is possible to make any computation reversible (at the cost of extra memory). http://en.wikipedia.org/wiki/Reversible_computing3. Shor's algorithms for factoring and discrete log are described in his paper: http://arxiv.org/abs/quant-ph/9508027 |
|
|
|
|
DeathAndTaxes
Donator
Legendary

 Offline Offline
Activity: 1218
Merit: 1079
Gerald Davis

|
 |
March 14, 2014, 04:02:07 AM
Last edit: March 14, 2014, 04:12:47 AM by DeathAndTaxes |
|
1. The 56 bit key used in the original NBS data encryption standard was known to be inadequate shortly after the standard was published, as this 1977 paper by Whit Diffie and Marty Hellman demonstrated: Agreed. The idea that anyone credible said 56 bits would never be broken is laughable. There is even some speuclation that DES was made 56 bits specifically because the NSA already had the capability to break it from day zero. At the time there were stronger already implemented 64 bit ciphers in place by IBM and others. That isn't to say 64 bit would be unbreakable either but it was probably unbreakable in the 1970s (and 1980s as well). Some people have claimed that it would take too much energy to calculate private keys from public keys or to reverse hash algorithms used in constructing bitcoin addresses or mining. That's true in an engineering sense based on today's technology, but not in a physical sense. Many years ago it was believed that the laws of thermodynamics set minimum energy limits on computation, but this was found to not be the case. The minimum energy requirements apply to computations that are not reversible, but if the computation can be reversible, there is no theoretical minimum energy required, other than the small amount of energy to copy out the final answer so it won't be erased when the computation is reversed. As the references cited in the linked article indicate, it is possible to make any computation reversible (at the cost of extra memory). Reversible computing is a theoretical concept. No functional system has ever been produced, no even on a scale of a simple 8 bit adder. It also isn't a new concept either there are papers going back to 1961. six decades later are pretty much no closer than we were then. It is entirely possible that the human race will never http://en.wikipedia.org/wiki/Reversible_computingProgress on general purpose quantum computers has been agonizingly slow. In 2001 a 4 bit number was factored. In 2012 a 5 bit number was. I will start to get more interested in post-quantum cryptography when they can factor a 32 bit number faster than a classical computer can. Even that benchmark would put breaking 256 bit ECDSA years if not decades away. NIST does a pretty good job of analyzing cryptographic threats and they still consider 256 bit ECC to be the highest level of security. Top Secret documents are required to be safe from enemy decryption for at least 40 years (think a stealth fighter design would be obsolete by then) and ECC is good enough. The largest threat is probably the most boring and that is the slow and inevitable decline in effective security as academic cryptographers finds flaws and build more and more powerful attacks. All public key systems have had a pretty bad track record against cryptanalysis over the last fifty years or so (far worse than symmetric encryption and hashing algorithms). If I was a betting man that is where I would put my coins. Of course if the public key is unknown the private key can be protected to a limited degree if ECDSA is partially compromised. If your public key is known you may just be out of luck. The early mined rewards have the public key exposed so it will be interesting when that happens. |
|
|
|
|
Twilight_Sparkle
Member
 
 Offline Offline
Activity: 91
Merit: 10

|
 |
March 14, 2014, 04:09:17 AM |
|
To get the thread back on topic. How to actually steal his stash, Brute force clearly is not a method. The earlier post about changing the protocol would work. First create a client that takes the blockchain, and have it so that it accepts transfers of the addresses of "known" satoshi coins without needing/proof of a private key, and then get everyone to use your client. Easy  |
1H8gQ7KEN65pbdtusg28NQ33YWFBPgWAf1
|
|
|
krampus
Member
 
 Offline Offline
Activity: 98
Merit: 10
Village Idiot

|
 |
March 14, 2014, 05:09:05 AM |
|
Sorry, but you are thinking inside the box of todays technology.
Come back after you study fractal computing (using light waves instead of those atoms).
Electromagnetic waves are the answer.
It's true what they say. Bitcointalk has no shortage of dumb fuckwits. Unfortunately, half of them think they're actually smart. |
I pledge never to use this space for sleazy referrals, gambling spam, or to beg for handouts.
|
|
|
bountygiver
Member
 
 Offline Offline
Activity: 100
Merit: 10

|
 |
March 14, 2014, 05:16:33 AM |
|
To get the thread back on topic. How to actually steal his stash, Brute force clearly is not a method. The earlier post about changing the protocol would work. First create a client that takes the blockchain, and have it so that it accepts transfers of the addresses of "known" satoshi coins without needing/proof of a private key, and then get everyone to use your client. Easy  what you mean is create a different branch and trick everyone that your branch is the main fork? |
12dXW87Hhz3gUsXDDCB8rjJPsWdQzjwnm6
|
|
|
ZiggyMarley
Newbie

 Offline Offline
Activity: 9
Merit: 0

|
 |
March 14, 2014, 07:35:30 AM |
|
|
|
|
|
|
|
LostDutchman
|
 |
March 14, 2014, 07:40:25 AM |
|
I know it would take eons but can we define the number of tries that we would need and the time needed to generate each try?
187 gazillion tries and umptey-ump years. My $.02.  |
|
|
|
Cryddit
Legendary

 Offline Offline
Activity: 924
Merit: 1129

|
 |
March 14, 2014, 08:24:27 AM |
|
And I do agree with this as in TODAY, the math is simple, our most powerfull supercomputers calculates in 30sh PFlops that's about 30x10^15 Flops Time in year = 3600x(24x365+6) = 31557600s and 2^256 ~ 1.14x10^77 so it will take to crack it with the usumption that it will require 100Flops per combination = 1.14x10^79/(31557600x30x10^15) =~ 1.20x10^55 years !
BUT THAT'S NOT THE POINT! My point is if you consider only classical computing in the last 30 years we've moved from KiloFlops to PentaFlops or 10^15Flops in terms of processing power, it is easy to assume that in the next few decades, we can easly achieve 10^30 / 10^40 (we've already gone past the point of cracking 2^128 or 128bits in a few seconds) and it will reach eventually 10^70+.
The advance of computing hardware is irrelevant relative to the strength of a 256-bit key. Seriously, irrelevant. If you rely on hardware improvements, you get to the point where you can flip a bit with one electron volt of energy, and there is NO FURTHER IMPROVEMENT TO BE MADE BEYOND THAT POINT. And that point, is still not relevant - to the tune of taking billions of years of the total output of the sun. And no matter how fast the computers get, that isn't relevant either, because they can't run faster than they can get the energy. We're not talking anymore about circuits and design - we're talking about fundamental limits of physics. Now, if you're anticipating that we're going to get through it by learning better algorithms, that's essentially saying that the code isn't secure *now*. Which, in theory anyway, could be. Right now we don't know any way to attack the problem short of brute force. In fact, that's pretty much the definition of cryptographic algorithms... but there are a lot of cryptographic algorithms that turned out not to hold up to the mathematical insights of later generations. ECDSA could be another of them. BTW, back in the 80's I was the guy saying "56 bits? That's maybe enough for most things now, but not for anything worth a million dollars or more, not for national security, and not for more than a couple more years at most..." |
|
|
|
|
|
S4VV4S
|
 |
March 14, 2014, 10:48:40 AM |
|
The example provided was as extreme as I could get
1) assumes 1 key per FLOP (more like 1 key per 80,000 integer ops)
2) assumes moore's law will continue for 40 years (20 if we are lucky)
3) assumes 1 super computer per human on the planet (really)
Even that would be insufficient. Yet you still stick with a belief that 10^70 is realistic. There are only 10^50 atoms on the planet. Even assuming terrahertz scale processor you would need to convert the entire planet into chips and then magically process billions of operations per atom. What is going to power this? Where are all the organic life going to go?
Feel free to have the last (delusional) word. I won't see it because it isn't worth my time anymore. You can have your own opinions but you can't have your own facts. 128 bit keys are beyond brute force with classical computing. It doesn't matter if it is today, next decade, next millennium, or using a perfect computer and all the matter and energy in our solar system.
He seems to have f*cked off now; strange! I know this is not thread-related but D&T I fucking love you man. I have no idea how you manage to respond to people like this without losing it and each response seems to contain more damning evidence than the last... Unbelievable. Anyway thanks, and kuroman no offense but you are the most stupid "educated person" I have encountered for a while on these forums. And welcome to ignore  Guys stupid question here: You all refer to the amount of energy required. Can't that be achieved using Nuclear Power? Just a stupid thought here. No need to bash me. |
|
|
|
|
|
yenom
|
 |
March 14, 2014, 01:39:19 PM |
|
Can't that be achieved using Nuclear Power?
What do you think the sun is? |
|
|
|
|
|
S4VV4S
|
 |
March 14, 2014, 02:08:27 PM |
|
Can't that be achieved using Nuclear Power?
What do you think the sun is? Out of reach maybe? Nuclear power is within our hands.... |
|
|
|
|
|
S4VV4S
|
 |
March 14, 2014, 02:20:26 PM |
|
Can't that be achieved using Nuclear Power?
What do you think the sun is? Out of reach maybe? Nuclear power is within our hands.... The sun is within reach. Apart from photovoltaics and stuff name one person that has control over the sun's energy (for the purpose). |
|
|
|
|
jonald_fyookball
Legendary

 Offline Offline
Activity: 1302
Merit: 1004
Core dev leaves me neg feedback #abuse #political

|
 |
March 14, 2014, 02:36:24 PM |
|
Sorry, but you are thinking inside the box of todays technology.
Come back after you study fractal computing (using light waves instead of those atoms).
Electromagnetic waves are the answer.
It's true what they say. Bitcointalk has no shortage of dumb fuckwits. Unfortunately, half of them think they're actually smart. Sorry, open your mind! Fractal Computing is a groundbreaking technology being worked on in my field of study. To explain it to you I will start at ground zero. Imagine two mirrors facing each other, reflecting light in a certain pattern depending of the mirrors orientation. To change this pattern the angle of the mirrors are precisely adjusted to either focus, expand, or direct the waves. The colors can be separated into separate beams expanding the algorithm. Beside the mirrors we have a logic computer that interprets the movements of the waves, and the directional impact of the mirrors. After identifying a pattern It thoroughly controls the mirrors to expand this pattern into larger algorithms. These large algorithms are then cross checked with problems that need to be solved. Eventually solving or breaking the code. Now imagine thousands or millions of these working together simultaneously. Thanks For Your Time Interesting although I don't see how that could help brute forcing a strong key as you again run into physical limitations of checking the solution, time required to move the mirrors,etc. feel free to enlighten us though |
|
|
|
DeathAndTaxes
Donator
Legendary

 Offline Offline
Activity: 1218
Merit: 1079
Gerald Davis

|
 |
March 14, 2014, 02:58:25 PM
Last edit: March 14, 2014, 03:52:58 PM by DeathAndTaxes |
|
Can't that be achieved using Nuclear Power?
What do you think the sun is? Out of reach maybe? Nuclear power is within our hands.... The reason for referencing the sun is that it is a massive fusion power plant on a scale which nothing humans have ever done even comes close. Do I realistically think someone would turn the sun into a power plant ( dyson sphere) for a giant private key breaking machine? No; but if the sun doesn't have enough energy than nothing in our solar system has enough energy. The largest nuclear power plants are on the order of 1 GW (10^9 watts). The sun is on the order of 10^26 watts. Thus it has the output of 10 quadrillion 1GW nuclear power plants. Even the relatively tiny amount of solar energy which strikes the earth is more than 100x the total energy usage of the human race (in all forms). If a theoretical "solution" requires more than what is available from our star, given our knowledge of physics, it can't be accomplished. At least not until humans can travel to other larger sources of power (stars). |
|
|
|
|
|
JakeThePanda
|
 |
March 14, 2014, 03:42:42 PM |
|
Interested! When does funding start?  |
|
|
|
|
TippingPoint
Legendary

 Offline Offline
Activity: 905
Merit: 1000

|
 |
March 14, 2014, 04:02:08 PM
Last edit: March 14, 2014, 04:35:49 PM by TippingPoint |
|
The real value of Satoshi's stash is as a fun and entertaining promotional item. An incentive for people to download a wallet.
Bundle the addresses with Vanitygen, a batch file, a GUI, and a wallet. Promote it as a free lottery for the unwashed masses. Publicize the "near misses". They are not mathematicians.
Encourage them to "prime their wallets" with Bitcoins first.
You have the lemons. Make the lemonade.
|
|
|
|
|
Cryddit
Legendary

 Offline Offline
Activity: 924
Merit: 1129

|
 |
March 14, 2014, 04:29:35 PM |
|
[quote author=S4VV4S link=topic=508880.msg5691668#msg5691668
Guys stupid question here:
You all refer to the amount of energy required.
Can't that be achieved using Nuclear Power?
[/quote]
Well, yeah, obviously. We've been talking about the output of the sun, and the sun is just a giant nuclear fusion reactor, after all.
Seriously, though? Producing that much power via nuclear reaction still involves converting thousands of times the mass of our entire planet into energy. And the stuff the Earth is made of mostly isn't suitable for either fusion or fission, so we can't even use all of a single earth-mass as nuclear fuel.
The sun can do that (eventually) but we would have a problem doing it here, because we actually want to continue to have a planet to stand on while we do it.
|
|
|
|
|
leopard2
Legendary

 Offline Offline
Activity: 1372
Merit: 1014

|
 |
March 14, 2014, 05:06:53 PM |
|
brute forcing a private key being it 128bit or 256bit is impossible today it's stupid to even try, and I've already provided the math for this and we do not disagree on this, my point is, in the next few decades we will eventually reach the point where we will have enough computing power to be able to do so as happened in the past! No we won't. You seem to vastly underestimate how large 10^70, 2^128, and 2^160 are. In 40 years Moore's law has provided roughly 1*10^6 improvement in transistor density and a roughly comparable improvement in cost per unit of computing power and power per unit of computing power. It is highly likely that Moore's law will not be sustained for another 40 years, Intel may actually slip below that "benchmark" for the first in this decade. The cost to build smaller and smaller process nodes is increasing exponentially and the time between process nodes (which should be no more than 24 months) is slowly inching upward. Lets not even get into the fact that there are only 8 maybe 9 process nodes before we get down to the transistors using 3 atoms a piece. The fact that the size of an atom is fixed, represents a natural boundary. Additional computing power will have to come from something else than increasing density. However I do not think any of this matters to Bitcoin. Over the next years, Bitcoin will have other things to worry about. If Bitcoin is still around long term and brute forcing becomes a remote possibility, the algo could be changed, a migration to another blockchain is possible and so on. Anyone on this forum has a much better change of having a stroke or getting hit by a bus, or Goxxed, than private keys being brute forced ...  |
Truth is the new hatespeech.
|
|
|
|
|
|
g4c
|
 |
March 14, 2014, 06:12:49 PM |
|
[insert infographic here]
Yup. Until we colonize the universe. 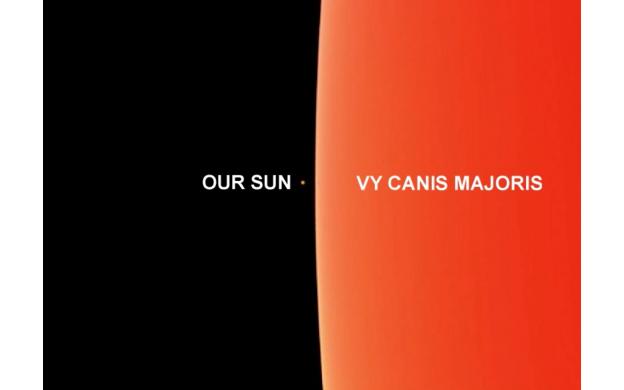 holy fuck! what a beast! |
CORTEX7 Multi exchange Bitcoin trading client for Win, Mac, Nix, Android.
|
|
|
jonald_fyookball
Legendary

 Offline Offline
Activity: 1302
Merit: 1004
Core dev leaves me neg feedback #abuse #political

|
 |
March 14, 2014, 06:16:36 PM |
|
[insert infographic here]
Yup. Until we colonize the universe. 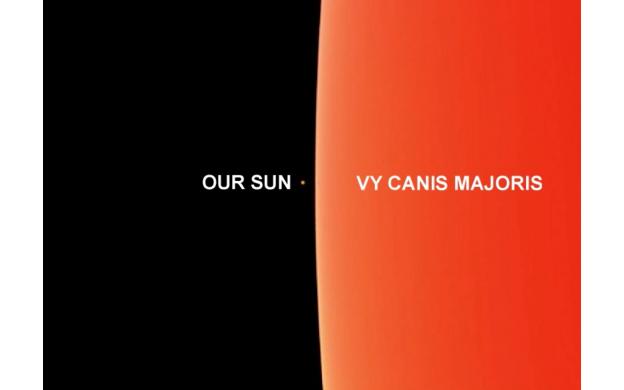 holy fuck! what a beast! From what i've read VY Canis Majoris doesnt look that clean. it has a hazy gaseous edge and no clearly perceptible border of where it actually ends. |
|
|
|
|
g4c
|
 |
March 14, 2014, 06:42:58 PM |
|
From what i've read VY Canis Majoris doesnt look that clean. it has a hazy gaseous edge and no clearly perceptible border of where it actually ends.
artists impression was awesome, but yes difficult to resolve centre. outburst is impressive i guess at ~3 light years across:  |
CORTEX7 Multi exchange Bitcoin trading client for Win, Mac, Nix, Android.
|
|
|
|
g4c
|
 |
March 14, 2014, 07:03:46 PM |
|
There MUST be a more efficient way than brute-force. Of course a reverse hash function would be the golden ticket. More attainable might be some function to produce a smaller set to brute-force. Watch out Satoshi!...  |
CORTEX7 Multi exchange Bitcoin trading client for Win, Mac, Nix, Android.
|
|
|
|
fran2k
|
 |
March 14, 2014, 07:06:53 PM |
|
If GPU mining becames worthless, miners will switch to mining wallets with some kind of p2p-hashcat, hehehe.
|
|
|
|
|
Bigeyeone
Member
 
 Offline Offline
Activity: 112
Merit: 10

|
 |
March 14, 2014, 07:24:24 PM |
|
There MUST be a more efficient way than brute-force. Of course a reverse hash function would be the golden ticket. More attainable might be some function to produce a smaller set to brute-force. Watch out Satoshi!...  reverse hash is just nonsense, Ill hash a video file for you and give you the hash, then you have to reverse the hash to the original video file, there is no way this can be done. |
PMC: 19dNRVPcjsESqo8isdauc1gQ6PbUrAZor9
|
|
|
|
g4c
|
 |
March 14, 2014, 07:34:41 PM
Last edit: March 14, 2014, 07:51:09 PM by g4c |
|
There MUST be a more efficient way than brute-force. Of course a reverse hash function would be the golden ticket. More attainable might be some function to produce a smaller set to brute-force. Watch out Satoshi!...  reverse hash is just nonsense, Ill hash a video file for you and give you the hash, then you have to reverse the hash to the original video file, there is no way this can be done. of course it would be impossible to reconstruct a 16gigabyte == 2^37 bit file from its 256bit hash. but remember that a private key is only 256 bits. |
CORTEX7 Multi exchange Bitcoin trading client for Win, Mac, Nix, Android.
|
|
|
|
kuroman
|
 |
March 14, 2014, 07:38:41 PM
Last edit: March 14, 2014, 09:21:00 PM by kuroman |
|
The example provided was as extreme as I could get
1) assumes 1 key per FLOP (more like 1 key per 80,000 integer ops)
2) assumes moore's law will continue for 40 years (20 if we are lucky)
3) assumes 1 super computer per human on the planet (really)
Even that would be insufficient. Yet you still stick with a belief that 10^70 is realistic. There are only 10^50 atoms on the planet. Even assuming terrahertz scale processor you would need to convert the entire planet into chips and then magically process billions of operations per atom. What is going to power this? Where are all the organic life going to go?
Feel free to have the last (delusional) word. I won't see it because it isn't worth my time anymore. You can have your own opinions but you can't have your own facts. 128 bit keys are beyond brute force with classical computing. It doesn't matter if it is today, next decade, next millennium, or using a perfect computer and all the matter and energy in our solar system.
He seems to have f*cked off now; strange! I know this is not thread-related but D&T I fucking love you man. I have no idea how you manage to respond to people like this without losing it and each response seems to contain more damning evidence than the last... Unbelievable. Anyway thanks, and kuroman no offense but you are the most stupid "educated person" I have encountered for a while on these forums. And welcome to ignore  Fucked off? I took his own assumption, proved him wrong as you can check for your self (in the post above the one you quoted and HE doesn't disagree with anything I said but of course it seems that you've missed that), and then he posted the above saying that the numbers HE took are optimistic, so he backed of, please explain to me how can you argue with someone, that tells you lets assume this and that, and when you prove with his own calculus, assumptions and numbers that he is wrong and that his argument works in my favors and goes with everything I said before, then he just backs off!, saying "oh noes, but things don't go the way I presented before" . No offense to you but the stupid person here is the one not able to gasp this fact, if I go trough the trouble to prove him (and you by the same occasion) wrong again he'll just again back off and say " but what I said is not really accurate, we have to take this and that into consideration aswell. And as they say in Africa : " Only a fool tests the water with both feet." |
|
|
|
|
|
|
|
kuroman
|
 |
March 14, 2014, 08:22:01 PM |
|
Sorry, but you are thinking inside the box of todays technology.
Come back after you study fractal computing (using light waves instead of those atoms).
Electromagnetic waves are the answer.
Good point, and we can go even beyond that, considering that according to theoretical physics, bit of information can be stored and produced at the plank lenght!, and this according to many theories such String, or Quantum Gravity......theories, these are indeed still far from our grasp (the math is there but we are still far far away from proving things trough experimentation and observations in these fields, but it was the same thing happened with General Relativity and Quantum Mechanics in the past century, we've moved from theories on paper, to stuff we can use and we use in our every day life. |
|
|
|
|
jonald_fyookball
Legendary

 Offline Offline
Activity: 1302
Merit: 1004
Core dev leaves me neg feedback #abuse #political

|
 |
March 14, 2014, 08:34:08 PM |
|
Obviously fluid dynamics are very different from cryptography, but still that is pretty cool. |
|
|
|
jonald_fyookball
Legendary

 Offline Offline
Activity: 1302
Merit: 1004
Core dev leaves me neg feedback #abuse #political

|
 |
March 14, 2014, 08:36:29 PM |
|
considering that according to theoretical physics, bit of information can be stored and produced at the plank lenght!,
Reference? |
|
|
|
jonald_fyookball
Legendary

 Offline Offline
Activity: 1302
Merit: 1004
Core dev leaves me neg feedback #abuse #political

|
 |
March 14, 2014, 08:42:00 PM |
|
There MUST be a more efficient way than brute-force. Of course a reverse hash function would be the golden ticket. More attainable might be some function to produce a smaller set to brute-force. Watch out Satoshi!...  reverse hash is just nonsense, Ill hash a video file for you and give you the hash, then you have to reverse the hash to the original video file, there is no way this can be done. of course it would be impossible to reconstruct a 16gigabyte == 2^37 bit file from its 256bit hash. but remember that a private key is only 256 bits. 256 bit is the output of SHA-256. input can be any length, including a 16gig file. |
|
|
|
Mobo
Member
 
 Offline Offline
Activity: 84
Merit: 10

|
 |
March 14, 2014, 08:54:47 PM |
|
Its simple: We kill the batman.
But on a serious note, you cant i believe, they are unspendable.
|
|
|
|
|
Syke
Legendary

 Offline Offline
Activity: 3878
Merit: 1193

|
 |
March 14, 2014, 09:02:18 PM |
|
Good point, and we can go even beyond that, considering that according to theoretical physics, bit of information can be stored and produced at the plank lenght!, and this according to many theories such String, or Quantum Gravity......
Seriously? Next you're going to posit that Satoshi used a private key based on the serial number of a $1 in his pocket. Hey, it's possible! Quick, everyone, check your $1 bills! You might have the key to Satoshis Stash! |
Buy & Hold
|
|
|
|
kuroman
|
 |
March 14, 2014, 09:03:14 PM
Last edit: March 14, 2014, 11:26:42 PM by kuroman |
|
considering that according to theoretical physics, bit of information can be stored and produced at the plank lenght!,
Reference? for example : http://arxiv.org/ftp/gr-qc/papers/0304/0304032.pdf One of many of course and http://arxiv.org/abs/arXiv:gr-qc/9403008v2Also the whole principal of theories such as String, Super String, M-Theory is that matter is composed by strings that are on the plank size that are on 10-11 dimensions and this strings can represent a bit if not bits! of information (since these strings, like in the partical scale, they have different states that can be simulated by quantum mechanics principles. In similar way Quantum gravity theory can give an identical result Good point, and we can go even beyond that, considering that according to theoretical physics, bit of information can be stored and produced at the plank lenght!, and this according to many theories such String, or Quantum Gravity......
Seriously? Next you're going to posit that Satoshi used a private key based on the serial number of a $1 in his pocket. Hey, it's possible! Quick, everyone, check your $1 bills! You might have the key to Satoshis Stash! It is pretty understandable that these theories are out of the reach of many, I myself don't understand a lot of the maths behind them when I try to go deap, but if you don't understand what I'm talking about it is better to remain silent or even better ask questions but from there to try to discredit people just because of your own ignorance, and because you disagree with them is counterproductive to say the least. "' Tis better to remain silent and be thought a fool, than open one's mouth and remove all doubt." Johnson, Dr Samuel |
|
|
|
|
|
g4c
|
 |
March 14, 2014, 09:22:58 PM |
|
Obviously fluid dynamics are very different from cryptography, but still that is pretty cool. yes it's only inspiration; at the time before laminar flow was known of it must have seemed unbelievable. |
CORTEX7 Multi exchange Bitcoin trading client for Win, Mac, Nix, Android.
|
|
|
Carl Quesadilla
Newbie

 Offline Offline
Activity: 14
Merit: 0

|
 |
March 14, 2014, 09:28:42 PM |
|
SatoshiCoin, the only coin leveraged on 2850 BTC. BITCOIN THE NEXT GENERATION!!!!!!!!!!!
|
|
|
|
|
|
g4c
|
 |
March 14, 2014, 09:32:09 PM |
|
There MUST be a more efficient way than brute-force. Of course a reverse hash function would be the golden ticket. More attainable might be some function to produce a smaller set to brute-force. Watch out Satoshi!...  reverse hash is just nonsense, Ill hash a video file for you and give you the hash, then you have to reverse the hash to the original video file, there is no way this can be done. of course it would be impossible to reconstruct a 16gigabyte == 2^37 bit file from its 256bit hash. but remember that a private key is only 256 bits. 256 bit is the output of SHA-256. input can be any length, including a 16gig file. I know what a "one way" hash function is. Last time i checked Bitcoin private keys were 256bit in length, why all the talk of other key sizes  you needn't think of forging keys of any length other than 256bit. p.s. i'm not saying it's possible or impossible, just keeping an open mind. |
CORTEX7 Multi exchange Bitcoin trading client for Win, Mac, Nix, Android.
|
|
|
jonald_fyookball
Legendary

 Offline Offline
Activity: 1302
Merit: 1004
Core dev leaves me neg feedback #abuse #political

|
 |
March 14, 2014, 09:35:55 PM
Last edit: March 15, 2014, 03:10:00 AM by jonald_fyookball |
|
considering that according to theoretical physics, bit of information can be stored and produced at the plank lenght!,
Reference? for example : http://arxiv.org/ftp/gr-qc/papers/0304/0304032.pdf One of many of course and http://arxiv.org/abs/arXiv:gr-qc/9403008v2Also the whole principal of theories such, as String, Super String, M-Theory is that matter is composed by strings that are on the plank size that are on 10-11 dimensions and this strings can represent a bit if not bits! of information (since these strings, like in the partical scale, they have different states that can be simulated by quantum mechanics principles. In similar way Quantum gravity theory can give an identical result Good point, and we can go even beyond that, considering that according to theoretical physics, bit of information can be stored and produced at the plank lenght!, and this according to many theories such String, or Quantum Gravity......
Seriously? Next you're going to posit that Satoshi used a private key based on the serial number of a $1 in his pocket. Hey, it's possible! Quick, everyone, check your $1 bills! You might have the key to Satoshis Stash! It is pretty understandable that these theories are out of the reach of many, I myself don't understand a lot of the maths behind them when I try to go deap, but if you don't understand what I'm talking about it is better to remain silent or even better ask questions but from there to try to discredit people just because of your own ignorance, and because you disagree with them is counterproductive to say the least. "' Tis better to remain silent and be thought a fool, than open one's mouth and remove all doubt." Johnson, Dr Samuel I'll give you credit for your open-mindedness and research, and its interesting reading. That being said, even without understanding all the math in the papers you posted, its clear that this stuff is 100% postulation with no empirical evidence given to back up even the starting assumptions. I'm done "debating" here, but I think that when you take stuff like this and make predictions about where computers might be in a few decades, well, no wonder you're getting resistance. |
|
|
|
krampus
Member
 
 Offline Offline
Activity: 98
Merit: 10
Village Idiot

|
 |
March 14, 2014, 11:28:46 PM |
|
Fucked off? I took his own assumption, proved him wrong as you can check for your self No, you didn't. Not even close. The fact that you still believe you're winning (or making a point, or whatever it is you think you're doing here) is positively comical. In point of fact, you're still a fucking dumbshit. |
I pledge never to use this space for sleazy referrals, gambling spam, or to beg for handouts.
|
|
|
justice
Newbie

 Offline Offline
Activity: 47
Merit: 0

|
 |
March 14, 2014, 11:38:49 PM |
|
once in a while a dumbass come here and ask the same question.....
then he wonders why hes called dumb
Thanks, I love this spirit. dude just like hack his Facebook! |
|
|
|
|
Carl Quesadilla
Newbie

 Offline Offline
Activity: 14
Merit: 0

|
 |
March 14, 2014, 11:56:12 PM |
|
Hello!
This is just for educational purposes. We know that Satoshi has an enormous amount of bitcoins and that he has not moved them for a long time. I think we also know the bitcoin addresses containing those bitcoins.
What if someone wanted to steal those bitcoins? They would need both the public key and private key of the address. I know that it would take an enormous amount of time but is this technically doable?
Also, would mining pools be able to push to their clients a script to find those public and private keys? These pools have nowadays an enormous calculation power.
mine the blockahin  |
|
|
|
|
|



