Cablez
Legendary

 Offline Offline
Activity: 1400
Merit: 1000
I owe my soul to the Bitcoin code...

|
 |
February 17, 2015, 10:04:37 PM |
|
Isn't that similar to J Edgar Hoover and the FBI of yore? They supposedly had dirt on everyone of consequence back then. Real easy to turn the power tables.
|
Tired of substandard power distribution in your ASIC setup??? Chris' Custom Cablez will get you sorted out right! No job too hard so PM me for a quote
Check my products or ask a question here: https://bitcointalk.org/index.php?topic=74397.0
|
|
|
|
|
|
|
|
|
|
|
|
If you see garbage posts (off-topic, trolling, spam, no point, etc.), use the "report to moderator" links. All reports are investigated, though you will rarely be contacted about your reports.
|
|
|
Advertised sites are not endorsed by the Bitcoin Forum. They may be unsafe, untrustworthy, or illegal in your jurisdiction.
|
freedomno1
Legendary

 Offline Offline
Activity: 1806
Merit: 1090
Learning the troll avoidance button :)

|
 |
February 18, 2015, 01:07:15 AM |
|
This is very orwellian
Scares the heck out of you when police and spy agencies can target individuals
When non violent peaceful activities get monitored by default that is a threat to all people especially if its in key storage infrastructure.
Recommend the Core Devs get checked as they were on the toplist
Companies developing cryptographic technologies
|
Believing in Bitcoins and it's ability to change the world
|
|
|
BitMos
Full Member
  
 Offline Offline
Activity: 182
Merit: 123
"PLEASE SCULPT YOUR SHIT BEFORE THROWING. Thank U"

|
 |
February 18, 2015, 06:47:53 AM |
|
This is very orwellian
Scares the heck out of you when police and spy agencies can target individuals
When non violent peaceful activities get monitored by default that is a threat to all people especially if its in key storage infrastructure.
Recommend the Core Devs get checked as they were on the toplist
Companies developing cryptographic technologies
then I don't understand why the "billionaires" of America are allowed to do what they want, they are just tools, probes, or test of exploits ?... nothing to be afraid of? Or have gain a domination over the nsa and are using them like their slaves for their needs? Never be scared, who is the Greatest? Who can you Trust? don't get fooled again. It's normal to die. Would you have trusted all along or just before the End? What's your relation with your coming crossing to the other side? Do you know yourself? Do you know your fears? Did you took the time to overcome them? |
money is faster...
|
|
|
AGD
Legendary

 Offline Offline
Activity: 2069
Merit: 1164
Keeper of the Private Key

|
 |
February 18, 2015, 07:49:14 AM |
|
Looks like U.S. goverment lost controll and NSA is now in charge. I am not conspiracy theory fanatic but how to explain all that. Land of the free is becoming land of slaves and drones infecting whole world with their controll freak shit.
US gov + US industry loves the NSA! They have gained huge advantages over the worldwide competitors due to the work of the NSA. |
|
|
|
phelix
Legendary

 Offline Offline
Activity: 1708
Merit: 1020

|
 |
February 18, 2015, 10:10:52 AM |
|
Looks like U.S. goverment lost controll and NSA is now in charge. I am not conspiracy theory fanatic but how to explain all that. Land of the free is becoming land of slaves and drones infecting whole world with their controll freak shit.
this Plenty of people will become pathologically paranoid from all this. I already curse the NSA when one of my systems runs slow   |
|
|
|
|
uki
Legendary

 Offline Offline
Activity: 1358
Merit: 1000
cryptojunk bag holder

|
 |
February 18, 2015, 10:40:20 AM |
|
This is when you start thinking 1984 was a mere fairytale.
|
this space is intentionally left blank
|
|
|
GreekBitcoin
Legendary

 Offline Offline
Activity: 1428
Merit: 1001
getmonero.org


|
 |
February 18, 2015, 10:44:04 AM |
|
 Stasi is bad! China is spying our companies. North Korea is spying their people. Iran censorships the web. etc... West democracy is the only way! oh wait.... |
|
|
|
|
GreekBitcoin
Legendary

 Offline Offline
Activity: 1428
Merit: 1001
getmonero.org


|
 |
February 18, 2015, 10:52:21 AM |
|
 So by giving CIA, NSA etc ultimate powers at least now the world is a safer place right? No terrorists, no wars, no threats, economic stability... I wonder who is going to save us from them. |
|
|
|
|
BitMos
Full Member
  
 Offline Offline
Activity: 182
Merit: 123
"PLEASE SCULPT YOUR SHIT BEFORE THROWING. Thank U"

|
 |
February 18, 2015, 11:03:12 AM |
|
 So by giving CIA, NSA etc ultimate powers at least now the world is a safer place right? No terrorists, no wars, no threats, economic stability... I wonder who is going to save us from them. that's my fav part, forget everything you saw, it's THE SHOW OF THE SWARM (). |
money is faster...
|
|
|
|
tss
|
 |
February 18, 2015, 12:49:11 PM |
|
CRAP! they got me! that's pretty slick though, hardware built in rats, glad it's public now.
how do i check if my drives are affected?
|
|
|
|
|
|
|
TippingPoint
Legendary

 Offline Offline
Activity: 905
Merit: 1000

|
 |
February 18, 2015, 03:59:40 PM |
|
It might be worth mentioning that the story, at least at this point, is that the altered hard drive firmware is not being installed on drives before they leave the factory. The story is that the altered firmware is later installed on targeted computers, sometimes by individually-prepared installation CDs, and sometimes by NSAs Office of Tailored Access Operations. During the middle part of the last decade, the special unit (TAO) succeeded in gaining access to 258 targets in 89 countries -- nearly everywhere in the world. In 2010, it conducted 279 operations worldwide. According to details in Washington's current budget plan for the US intelligence services, around 85,000 computers worldwide are projected to be infiltrated by the NSA specialists by the end of this year. By far the majority of these "implants" are conducted by TAO teams via the Internet. http://www.spiegel.de/international/world/the-nsa-uses-powerful-toolbox-in-effort-to-spy-on-global-networks-a-940969-druck.html |
|
|
|
|
uki
Legendary

 Offline Offline
Activity: 1358
Merit: 1000
cryptojunk bag holder

|
 |
February 18, 2015, 04:27:57 PM |
|
It might be worth mentioning that the story, at least at this point, is that the altered hard drive firmware is not being installed on drives before they leave the factory. The story is that the altered firmware is later installed on targeted computers, sometimes by individually-prepared installation CDs, and sometimes by NSAs Office of Tailored Access Operations. During the middle part of the last decade, the special unit (TAO) succeeded in gaining access to 258 targets in 89 countries -- nearly everywhere in the world. In 2010, it conducted 279 operations worldwide. According to details in Washington's current budget plan for the US intelligence services, around 85,000 computers worldwide are projected to be infiltrated by the NSA specialists by the end of this year. By far the majority of these "implants" are conducted by TAO teams via the Internet. http://www.spiegel.de/international/world/the-nsa-uses-powerful-toolbox-in-effort-to-spy-on-global-networks-a-940969-druck.htmlThat changes the scale of the whole story quite drastically. Media love to alarm people as they will gladly read such stories. There is of course an immediate question popping up: what if someone used that kind of weapon against the 'average Joe' and for what reason? |
this space is intentionally left blank
|
|
|
BitMos
Full Member
  
 Offline Offline
Activity: 182
Merit: 123
"PLEASE SCULPT YOUR SHIT BEFORE THROWING. Thank U"

|
 |
February 18, 2015, 04:33:53 PM |
|
It might be worth mentioning that the story, at least at this point, is that the altered hard drive firmware is not being installed on drives before they leave the factory. The story is that the altered firmware is later installed on targeted computers, sometimes by individually-prepared installation CDs, and sometimes by NSAs Office of Tailored Access Operations. During the middle part of the last decade, the special unit (TAO) succeeded in gaining access to 258 targets in 89 countries -- nearly everywhere in the world. In 2010, it conducted 279 operations worldwide. According to details in Washington's current budget plan for the US intelligence services, around 85,000 computers worldwide are projected to be infiltrated by the NSA specialists by the end of this year. By far the majority of these "implants" are conducted by TAO teams via the Internet. http://www.spiegel.de/international/world/the-nsa-uses-powerful-toolbox-in-effort-to-spy-on-global-networks-a-940969-druck.htmlThat changes the scale of the whole story quite drastically. Media love to alarm people as they will gladly read such stories. There is of course an immediate question popping up: what if someone used that kind of weapon against the 'average Joe' and for what reason? ukie boy they fucking don't care of average joe, they want his wife and his daughter... the rest is pure BS, they are primates. |
money is faster...
|
|
|
uki
Legendary

 Offline Offline
Activity: 1358
Merit: 1000
cryptojunk bag holder

|
 |
February 18, 2015, 04:40:33 PM |
|
That changes the scale of the whole story quite drastically. Media love to alarm people as they will gladly read such stories. There is of course an immediate question popping up: what if someone used that kind of weapon against the 'average Joe' and for what reason?
ukie boy they fucking don't care of average joe, they want his wife and his daughter... the rest is pure BS, they are primates. BitMos, just read my post again. I wrote that such story sells very well in the media, as people tend to think 'what if they used it against my computer?' Of course they don't care about the average Joe like you or me (as of today), but who knows if one day you become important guy, you may want to check your hard drive. |
this space is intentionally left blank
|
|
|
BitMos
Full Member
  
 Offline Offline
Activity: 182
Merit: 123
"PLEASE SCULPT YOUR SHIT BEFORE THROWING. Thank U"

|
 |
February 18, 2015, 04:55:18 PM |
|
That changes the scale of the whole story quite drastically. Media love to alarm people as they will gladly read such stories. There is of course an immediate question popping up: what if someone used that kind of weapon against the 'average Joe' and for what reason?
ukie boy they fucking don't care of average joe, they want his wife and his daughter... the rest is pure BS, they are primates. BitMos, just read my post again. I wrote that such story sells very well in the media, as people tend to think 'what if they used it against my computer?' Of course they don't care about the average Joe like you or me (as of today), but who knows if one day you become important guy, you may want to check your hard drive. that's why PLAoC and Russia have no others choices... I know that for American controllers every girls born on earth is a future hole they will fuck (they are worth it remember, they are the chosen ones)... And what do you think the Germans think about a foreign nations having access to all the data of their Nation? ahaha... amerikis, betrayal&deceit incorporated. |
money is faster...
|
|
|
Balthazar
Legendary

 Offline Offline
Activity: 3108
Merit: 1358

|
 |
February 18, 2015, 05:01:33 PM
Last edit: February 18, 2015, 09:18:25 PM by Balthazar |
|
The U.S. National Security Agency has figured out how to hide spying software deep within hard drives made by Western Digital, Seagate, Toshiba and other top manufacturers, giving the agency the means to eavesdrop on the majority of the world's computers, according to cyber researchers and former operatives. STORY: http://www.cbc.ca/news/technology/nsa-hid-spying-software-in-hard-drive-firmware-report-says-1.2959252KASPERSKY super technical PDF REPORT: http://25zbkz3k00wn2tp5092n6di7b5k.wpengine.netdna-cdn.com/files/2015/02/Equation_group_questions_and_answers.pdf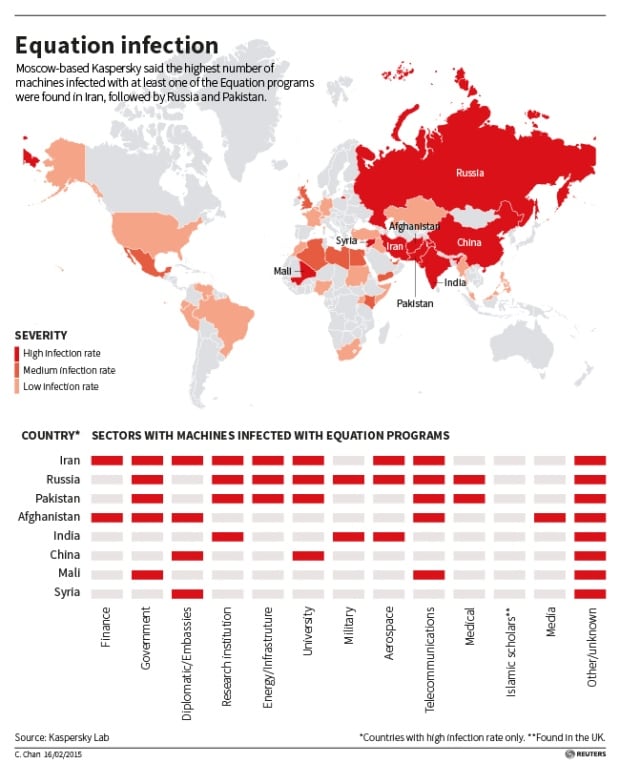 Kaspersky said it found personal computers in 30 countries infected with one or more of the spying programs, with the most infections seen in Iran, followed by Russia, Pakistan, Afghanistan, China, Mali, Syria, Yemen and Algeria. (Kaspersky Lab/Reuters) This feature will be helpful only if it's targeted against the regular user, because any government has a special policy for ssecret/private information. If we're talking about Russia then there are serious requirements to hardware and software if you wish to work with sensitive data, such as secret documentation. Here are some of those requirements: - FSB approved SATA/SAS controller with runtime encryption and separate flash memory for the boot loader, kernel image and device drivers. 1;
- Approved operation system2;
- All system modules should be digitally signed, it's prohibited to execute any unsigned software;
- Isolated network or no networking at all;
- Mandatory access control (MAC) for file system and database records.
If somebody would work with secret data while his system doesn't match those requirements, he'll get few years in the jail for simply doing that.  1. I.e. so-called APMDZ aka "hardware-software module for trusted boot", our company provides Maxim-M1 for that purpose. 1. I.e. so-called APMDZ aka "hardware-software module for trusted boot", our company provides Maxim-M1 for that purpose.
2. Current preference is our debian-based Linux distro, AstraLinux SE. It's currently used by the most of government institutions to work with sensitive data. |
|
|
|
|
BitMos
Full Member
  
 Offline Offline
Activity: 182
Merit: 123
"PLEASE SCULPT YOUR SHIT BEFORE THROWING. Thank U"

|
 |
February 18, 2015, 05:08:05 PM |
|
If somebody would work with secret data while his system doesn't match those requirements, he'll get few years in the jail for simply doing that.  I hope so, otherwise it would allow a plausible deniability way for the traitors... and who does want to see the Motherland fall in the Hands of the controllers of America (biden, his son, or the worst they hide under praise and glory). |
money is faster...
|
|
|
|
98problems
|
 |
February 18, 2015, 11:19:45 PM |
|
It might be worth mentioning that the story, at least at this point, is that the altered hard drive firmware is not being installed on drives before they leave the factory. The story is that the altered firmware is later installed on targeted computers, sometimes by individually-prepared installation CDs, and sometimes by NSAs Office of Tailored Access Operations. During the middle part of the last decade, the special unit (TAO) succeeded in gaining access to 258 targets in 89 countries -- nearly everywhere in the world. In 2010, it conducted 279 operations worldwide. According to details in Washington's current budget plan for the US intelligence services, around 85,000 computers worldwide are projected to be infiltrated by the NSA specialists by the end of this year. By far the majority of these "implants" are conducted by TAO teams via the Internet. http://www.spiegel.de/international/world/the-nsa-uses-powerful-toolbox-in-effort-to-spy-on-global-networks-a-940969-druck.htmlThat changes the scale of the whole story quite drastically. Media love to alarm people as they will gladly read such stories. There is of course an immediate question popping up: what if someone used that kind of weapon against the 'average Joe' and for what reason? I wouldn't be surprised if the 'average person' were targeted by some program similar to this. They already are targeted by a number of other NSA spying programs so I don't see why this would be any different |
|
|
|
|
jt byte
|
 |
February 19, 2015, 02:36:53 AM |
|
The US has control of the internet, communications satellites, and everything else we use to communicate electronically
|
|
|
|
|
|



