|
Any hardware wallet that works with PSBT / BIP-174 will work.
But, is it really worth it to just though all the hoops to get it to work.
There are other easier ways to do it. Better ways? Tough call. Easier ways? Yes.
-Dave
|
|
|
|
|
IMO it's a who cares. What you, or someone pretending to be you, at ANY other forum does not matter.
Here regulates here and there regulates there. Lets assume I setup an account someplace else and I teleport my account there.
And never use it. And then for whatever reason it gets compromised. That account then does bad things.
But...I never used it and I don't care. Why should that matter to me here. If I then go in and remove the proof here that it was me there what does it matter?
Because:
1) The account was compromised and is was not me so who cares.
2) It was not compromised and it WAS me, but you can't prove it.
Either way, it's a there problem not a here problem.
-Dave
|
|
|
|
Since the cost does not include enough space for a full node how much does it cost to go to 1TB for storage? It's not much work to do a quick pre-install of BTC and then bill you at a profit for bandwidth overages and storage overages. Remember, most if not all hosts give you X bandwidth and even if you are doing your initial sync from a local node to your local node and never touching the internet that bandwidth still counts against your monthly total. If you have the bandwidth at home or wherever, I have been doing these for people: https://www.amazon.com/dp/B0C7GKG3PZ/ref=syn_sd_onsite_desktop_0?ie=UTF8&pd_rd_plhdr=t&aref=akpWrBFv5f&th=1take out the 512GB drive that comes with it and put in a 1TB. For under $250 you have a NEW machine that does not pull too much power that can more then then run a node + electrum server and a LN server if you want. -Dave |
|
|
|
for those that dont know traincarwreck. ill translate
nashy nash, nash, Nash!...Nash?
Odd, I got blah, blah, blah, blah, blah when I ran it though my translator. What's funny is that it's posted on github so you can open issues on it, but I don't want to use my main git account and am too lazy to crate another one just to do it. Either way, does not matter, it's just junk. -Dave |
|
|
|
The main question is what is going to be different then all the other open source block explorers out there that you can just run quite easily yourself? https://github.com/janoside/btc-rpc-explorerHas a good API and does a lot in a VERY small footprint. Not the fastest but for doing it yourself for your own private use or small business it's fine. -Dave |
|
|
|
Just to tag on, there are some ONLINE CUSTODIAL services THAT YOU SHOULD NOT BE USING that only allow 1 transaction per address. If you (or anyone) send anything else to that address then they keep it. Full stop. Just a heads up on that. Not your keys, not your coins. Never ever give out addresses that you do not have the private keys to. Paying 100 extra TX fess because all coins come into your control before you send them elsewhere is better then loosing that 1 TX because oops, that address is no longer valid. Same with you sending out of exchanges to someplace else. Exchange -> you -> wherever. Or you can wind up having this happen to you: https://bitcointalk.org/index.php?topic=5476264.0-Dave |
|
|
|
They self sybil and fill Wasabi with fake volume. Very easy for them to link inputs and outputs.
Just to keep fair criticism here, sybil attacks in coinjoins are easily detectable, in order for the attack to work efficiently in deanonymizing a certain input -- the coordinator needs to refuse connection confirmations from all other participants, so if your input has not been spent before and the coordinator rejects your connection it's safe to assume that it's preparing for a Sybil attack on an input it identified earlier in the current round. Obviously, at this stage, it's hard to tell if enough adequate users still use Wasabi to spot sybil attacks. In *theory* couldn't all their transactions be sybil attacks. All inputs except 1 for each mix come from them / known source. Every time the coodinator sees something coming in it has local wallets fill the rest of the space so to speak. Yes there is a large cost and complexity. But we are talking millions of dollars at most, not an unobtainable amount of money for a business. -Dave |
|
|
|
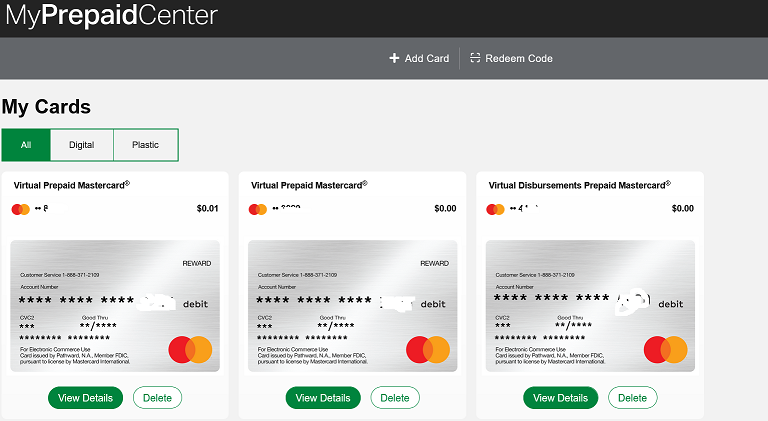
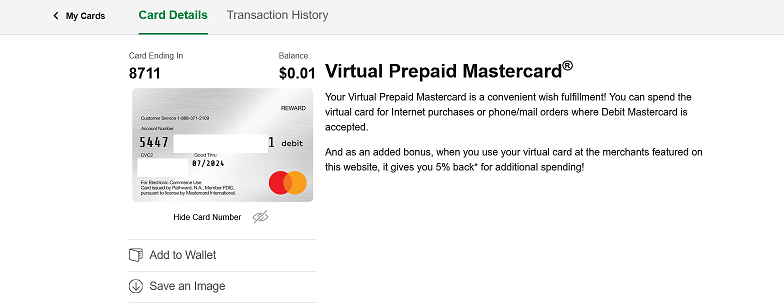
What kind of a site only has tolled (paid) numbers for customer support and no email? Obviously a scam site that knows that most people will not bother to spend money to make an international call when only 5-10 dollars have been stolen from them. You have 1000s of posts here and you're VOUCHING for an obvious scam site? I just don't understand it. VPN session or no VPN session, why would they display a blank card with no numbers? The attitude of the support email person at support@coinsbee.com has proven beyond doubt that it is a scam operation. This VPN excuse is the same one he kept repeating. I've never heard of a site working this way under VPN. I'll wait for someone else to respond before saying anything else. Edit: I added a review on TrustPilot and now Coinsbee.com is trying to give an excuse that i purchased from some other site not Coinsbee. I have also emailed the actual company known as Pathward N.A. and we will soon know if myprepaidcenter.com is related to them or not. Obviously it is not and it is a scam. coinsbee is also on the forum https://bitcointalk.org/index.php?action=profile;u=2667213They (myprepaidcenter.com) have plenty of toll free numbers in the US. They are a public US / North American company and for the most part only deal with people in the US / North America. Most, perhaps all, of my US issued credit cards don't have toll free numbers out of the US so that is not unusual. As for the VPN, since they are a financial services company they have to abide by KYC / AML rules. $1 or $5 or $1000 or $5000 or $100,000 it's all the same in the eyes of KYC / AML rules. This is what I see when I 1st log in. [I blanked some info]  Once I click on view details I see the full info [I blanked some info]  What do you get when you click view details? Pathward has nothing to do with coinsbee all coinsbee is doing is reselling their cards as do hundreds of other services. With all the above being said, they are very very twitchy when it comes to security. https://www.reddit.com/r/SwagBucks/comments/150olvk/stay_away_from_getting_myprepaidcenter_mastercard/You see it as a $5 gift card I see it as a $5 card they (my prepaid / blackhawk / Pathward) *have* to see it as the potential to get 1000 x $1000 gift cards and move a $1,000,000 in less time then it took me to type this. https://financialcrimeacademy.org/the-essential-guide-to-prepaid-card-money-laundering/-Dave |
|
|
|
....
Nope, it's something on your side. Bitrefill and many other places use myprepaidcenter.com for their mastercard prepaid cards. Try a different browser. Also, they are US (possibly North America) only for some services. And they do block VPNs https://bitcointalk.org/index.php?topic=5208530.msg61853963#msg61853963Log out, log back in, try using a private browser window. Heck, even a MC I got from a class action lawsuit was run through the myprepaidcenter.com site. I also don't see that 866 number you gave on their site: https://myprepaidcenter.com/contactus-Dave |
|
|
|
I think you've misread something. First things first, the links you've mentioned talk about the exit nodes (which are your "way out" to the clearnet). Wasabi utilizes hidden services, that means, no exit nodes intervene.
Yes, I grabbed the wrong links I'm mobile / remote at the moment. But you are still passing information to hidden services in clear text. The links I wanted to grab discussed that sending things in the clear was now creating a need to trust the person getting the data (in this case wasabi but they were discussing ahem...other things) and the person running the last hop that service was connecting to which 99% of the time was the service itself. Might not be making myself 100% clear here but the best way to say it is that since the wasabi coordinator itself is getting the info in cleartext unless they are running their onion services on the same server then somewhere even if it's just between Virtual Machine 1 and Virtual Machine 2 on the same physical hardware blade there is still data being unencrypted data being passed. Is it a 'real' threat? Depends on how they are doing things. In the end, probably not important since you are trusting them to do things they way they say they are doing them anyway. -Dave |
|
|
|
You are going to have to jump thought a bunch of hoops to get there but you can get old / unsafe / you should not be running them versions of nodejs here: https://nodejs.org/dist/You are then going to have to go through and install any dependency it needs one at a time. archive.org is your friend for this it may not get you everything but it should get you a lot. The other way to go is Yiimp there are a few installer scrips for that out there. -Dave |
|
|
|
Isn't it the other way around: SSL stripping doesn't reduce your privacy, but it makes you send Bitcoin to the wrong address. The point I was making is that if you are either a motivated criminal or a business or a government spinning up a ton of exit nodes and other services is not difficult. And it makes people using 'many different exit nodes' for privacy loose a lot of it. The tor cannot be tracked is bogus considering the number of tor sites that have been traced / seized over the years. -Dave |
|
|
|
Wouldn't it be more likely for all privacy minded users to abandon Wasabi entirely? Even if the current bad reputation isn't enough, that will end the moment it's bought by a blockchain analysis company.
The "privacy minded users" are not their target. Instead their target is the majority who don't really understand how to improve their privacy and are too lazy to do any research so they end up in a honeypot like Wasabi wallet..... I posted it earlier someplace but we are not their target audience for the most part. It's businesses that want 'privacy theater' so you can have peoples coins and put on a nice show that due to the fact that they are using this wallet with this feature that people can have privacy. And look we will never send you 'tainted' coins because these nice people are checking them for you. Much like people buying bitcoin ETFs instead of just buying coin. ...Tor ...
Tor is pointless, no you can't steal funds with this attack using Tor but to think it provides privacy is weak at best. https://therecord.media/thousands-of-tor-exit-nodes-attacked-cryptocurrency-users-over-the-past-year-Dave |
|
|
|
...But if you want to stack coins with no kyc and have a need for heat a modded m50 or s19 is viable....
Even with the mods, unless you know something I don't, you still have to get 220V to wherever you want the heat. I am using a modded S9 for heat in the back room of the condo at the moment, would love to do something faster / more efficient but it's all 120V without doing a bunch of work. -Dave |
|
|
|
Ordinals has absolutely nothing to do with coinjoins.
This is my last post to you since you don't seem to care and I am tired of wasting my time. You are 100% correct ordinals has absolutely nothing to do with coinjoins. Ordinals are filling blocks with transactions that are obviously not coinjoins. And the rest is Crateology. https://en.wikipedia.org/wiki/CrateologyAs I said take out ordinals, take out known TXs, take out what else they know from other services and you have a very small pool of txs moving at the moment. Keeping an eye on all of them and figuring out what is going on where is a lot less difficult then if all the txs in blocks were 'real' transactions. Could 1 person do it looking at a list? Probably not. Can a lot of people with a lot of computing power and resources following all transactions do it. Probably yes. You also seem to think that there are not a ton of tor nodes that are not run by and fully monitored by the government too. -Dave |
|
|
|
There are probably more then a few people on this board sitting with 50+BTC from the early days who could setup a coordinator Setting up a coordinator doesn't cost any BTC, a coordinator just sends messages back and forth to coinjoin participants. Once again, if I setup a CoinJoin Coordinator for Wasabi users with a bit of tweaking it's not impossible. Getting people to use it would be the issue. But if I am charging no fees I can see where every TX came from and where they went. How would you be able to see where every tx came from or where they went? Did you read gmaxwell's explanation about Chaumian blind signatures? Don't the users learn which inputs match up to which outputs?
In the simplest possible implementation where users meet up on IRC over tor or the like, yes they do. The next simplest implementation is where the users send their input and output information to some meeting point server, and the server creates the transaction and asks people to sign it. The server learns the mapping, but no one else does, and the server still can't steal the coins.
More complicated implementations are possible where even the server doesn't learn the mapping.
E.g. Using chaum blind signatures: The users connect and provide inputs (and change addresses) and a cryptographically-blinded version of the address they want their private coins to go to; the server signs the tokens and returns them. The users anonymously reconnect, unblind their output addresses, and return them to the server. The server can see that all the outputs were signed by it and so all the outputs had to come from valid participants. Later people reconnect and sign. 1) Because all the other coins in the coinjoin would be that persons. That is the point. 2) Later people reconnect and sign is the problem. It's usually (not always) not later, it's then and there. a->b->c tend to happen in somewhat real time. So now I know what to look for. And with blocks being full with ordinals at the moment you can probably eliminate 80+% of the TX, take out what are other known addresses and transactions. And the few dozen or hundred at the most can be sorted through at the governments leisure. -Dave |
|
|
|
If a Fed was running a Whirlpool coordinator, they could perform a targeted attack where they only choose you to mix in rounds with 4 decoys so you gain a false sense of privacy. Or, they could just rug pull you by not mixing your funds after you pay the coordinator fee.
Should read: ANYONE can run a Whirlpool coordinator, and they CAN perform a targeted attack where they only choose you to mix in rounds with 4 (or more) decoys so you gain a false sense of privacy. Or, they could just rug pull you by not mixing your funds after you pay the coordinator fee. There are probably more then a few people on this board sitting with 50+ BTC from the early days who could setup a coordinator
- Can WabiSabi be traced?
Not unless you are the biggest whale in a coinjoin round with insufficient liquidity. Even outputs that do not have matching amounts cannot be traced to an owner on the input side - its even possible that the output changed hands as a payment to someone who did not own any funds on the input side at all:
Once again, if I setup a CoinJoin Coordinator for Wasabi users with a bit of tweaking it's not impossible. Getting people to use it would be the issue. But if I am charging no fees I can see where every TX came from and where they went.
The right tool for the right job. Hammering together something to make your BTC private will always have flaws / vulnerabilities. It was not made to be private. Same way a VW Bug was not made to haul lumber. You can do it but why. Rent a pickup truck or a van. Same here, want more private BTC there are enough BTC -> XRM or other privacy coins -> BTC and done.
Not kicking any of the people working hard to do this, but it really seems to be more effort then it's worth. -Dave |
|
|
|
|