Once you have the WIF private key, keep it offline and sign offline. There's no need to risk exposing your private keys to an online computer. Online:Install Electrum on your PC. Import your address to create a watch-only wallet. Preview the transaction, Copy the unsigned transaction. Put it on a USB stick. Offline and running without hard drive storage:Get a Linux LIVE DVD. Use Knoppix or Tails for instance, or any other distribution that comes with Electrum pre-installed. Unplug your internet cable. Close the curtains. Reboot your computer and start up from that DVD. Don't enter any wireless connection password. Keep it offline. Start Electrum. Import your private key. Copy your unsigned transaction from the USB stick, load it into Electrum. CHECK the transaction in Electrum. Check the fees, check the amount, check all destination addresses ( character by character). If all is okay, sign the transaction. Copy it back to your USB stick. Turn off the computer. That wipes the Live LINUX from memory and all traces are gone. Online:Use your normal online Electrum to (check again and) broadcast the transaction. Bonus:After moving all your Bitcoin, and once the transaction confirmed, check if you own Forkcoins. |
|
|
|
Update:New Trust lists created in the last week:
|
|
|
|
While having contact information is essential, adding your email address as plaintext can attract spam to your inbox. It's not as if I use that email for anything else  It's better to display it as an image to prevent bots from reading your email. Bots can read images just as well as humans can. |
|
|
|
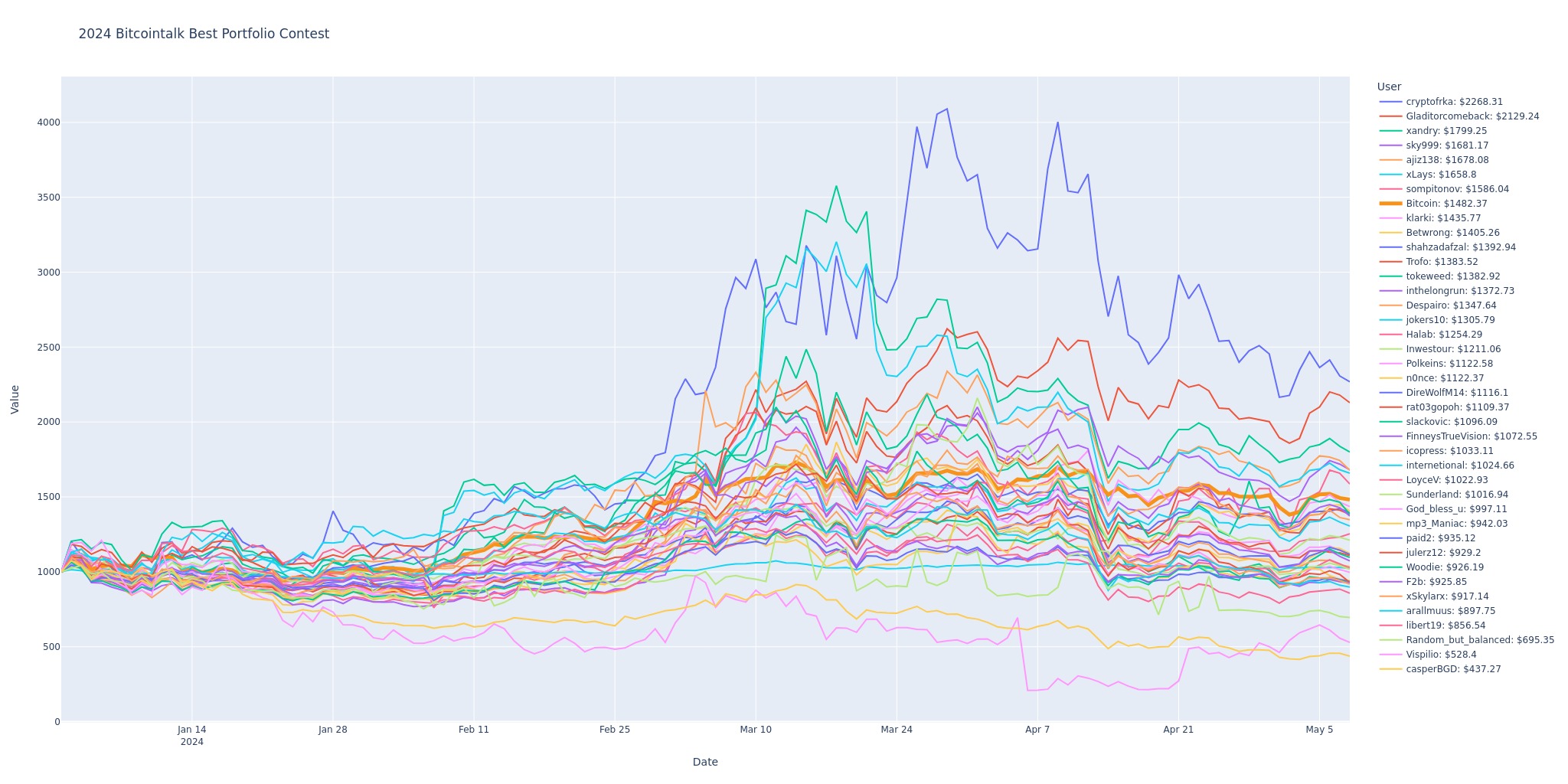
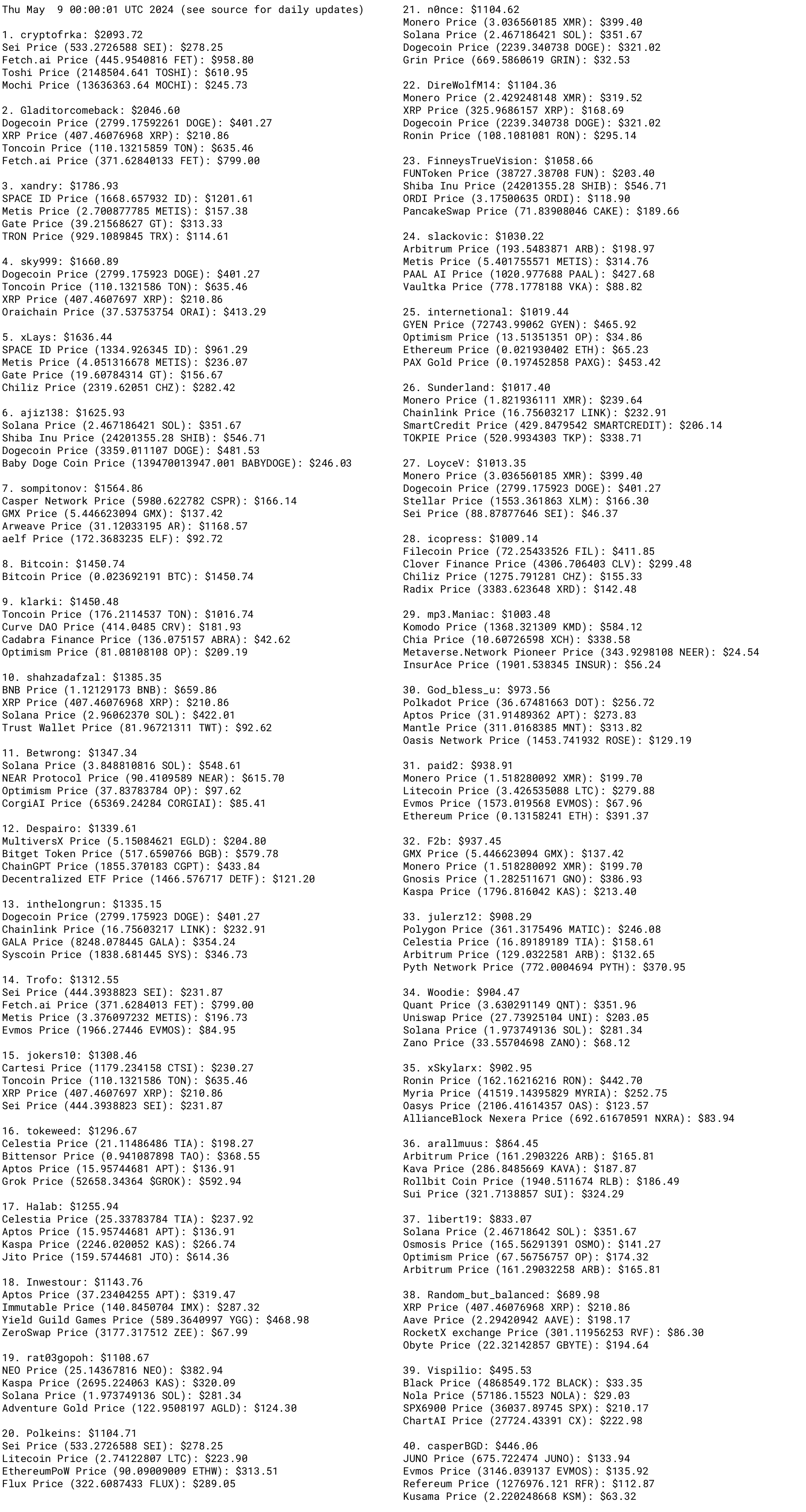
How about running it multiple times until none of the returned $ values are 0? I guess it's not that important for the daily standings / graphics whether it's the 00:00 standing or 01:00, since what really counts will only be the final results, right. That's easy to add indeed. I've changed it like this: 6 seconds between API-requests, but if the API gives me an empty output, I'll wait 1 minute and try again. Let's see if this works tomorrow. Update: this may fail once one of the coins gets delisted, but it worked last night. The volatility in less than a week is amazing: Graphs provided by n0nce : 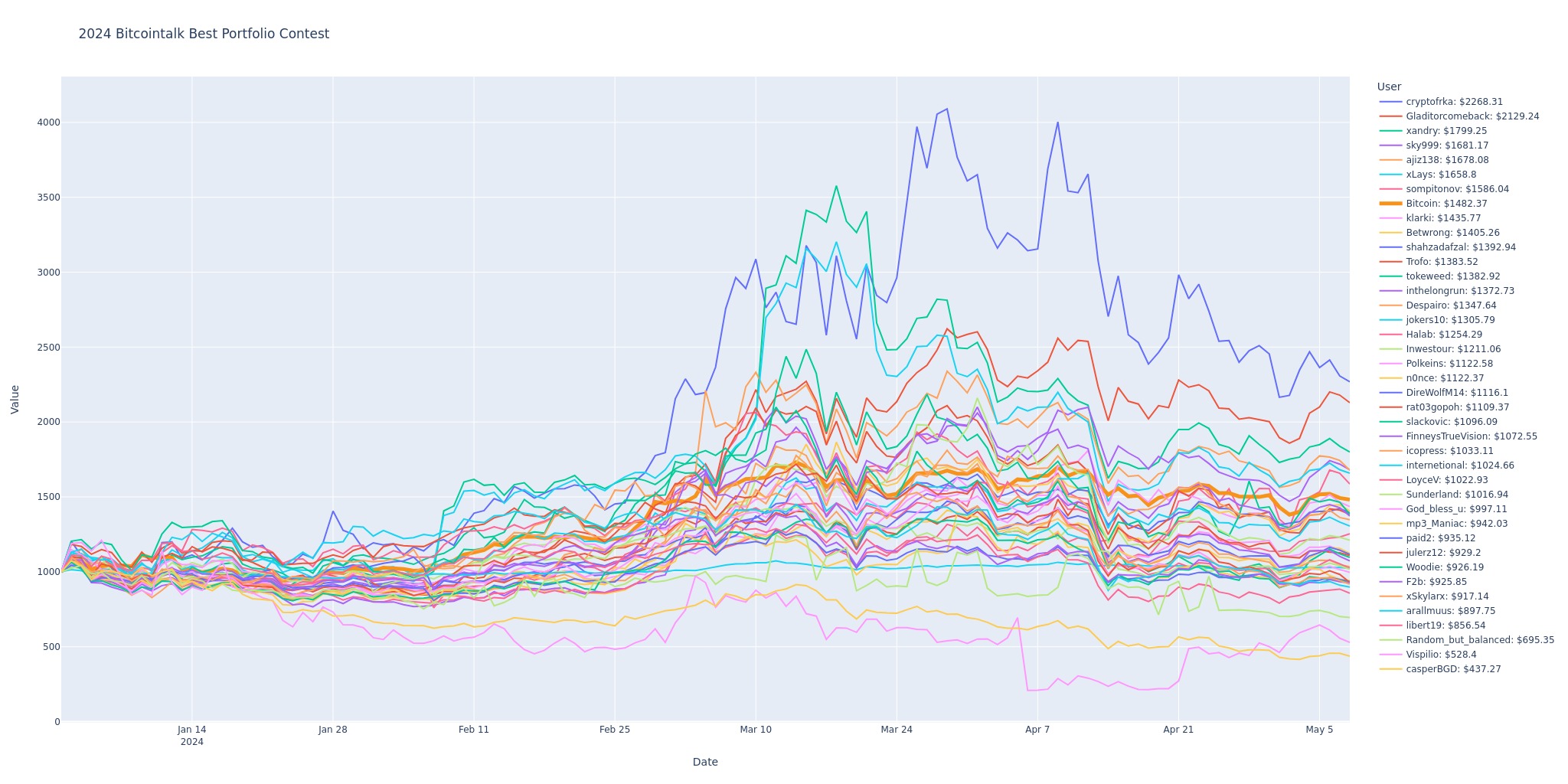 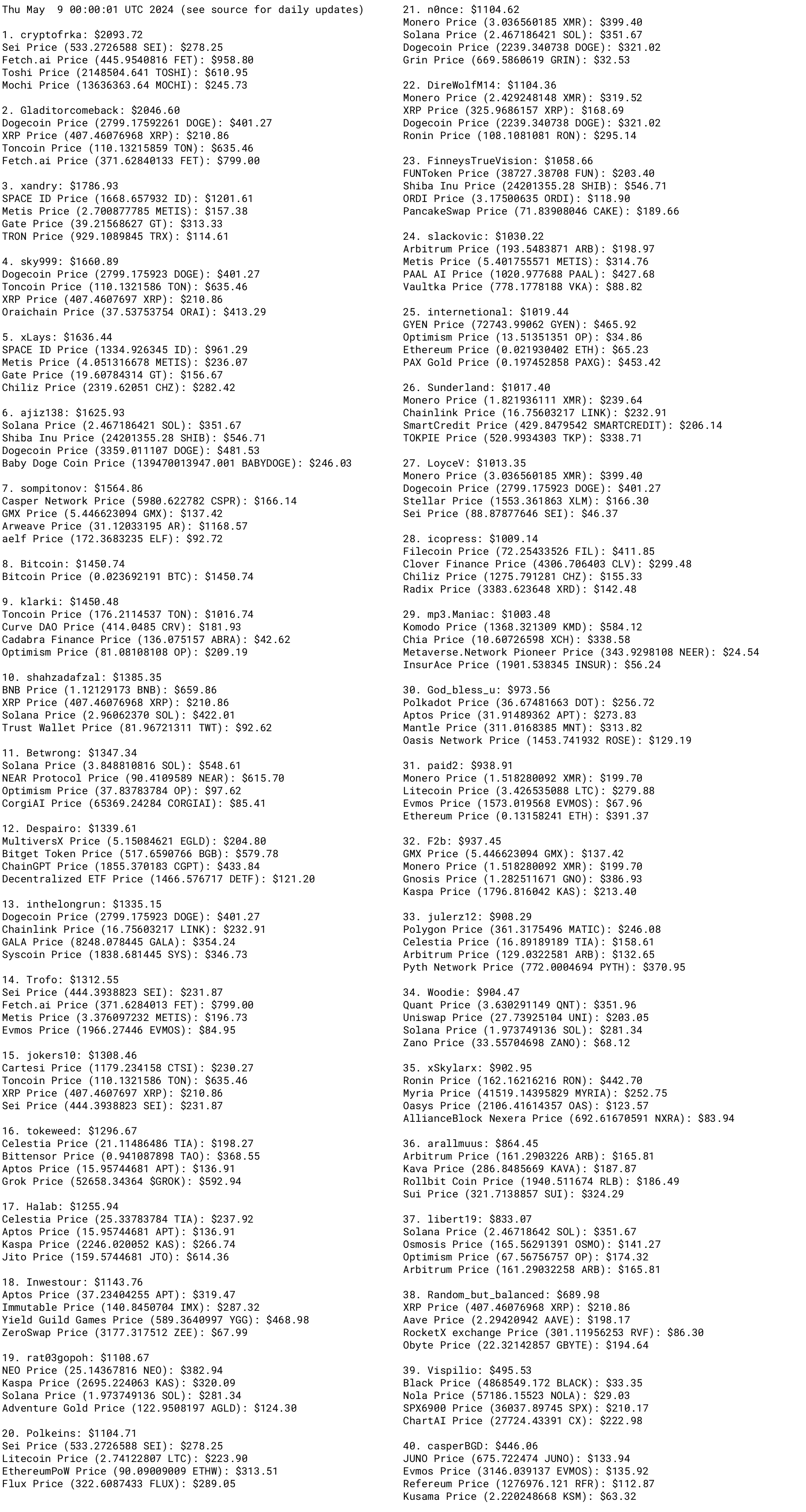 |
|
|
|
Logically, if a DMCA notice was sent to Bitcointalk, they likely sent a similar notice to Loyce.club. However, I believe LoyceV doesn't have any contact info except for the PM option. Good point, I've added my email address. I've censored archived posts before. |
|
|
|
How about running them a few times e.g. at 00:00, 01:00, 02:00? I ran the whole script again. Sometimes the API just blocks me, despite having a 16 seconds delay between scraping. |
|
|
|
It's not getting confirmed at all though, is it? Since I can see nothing but growth there. About 10 hours ago, it flatlined, and at the same time, the lighter green area started to grow. If I'd have to guess, that's because ViaBTC reduced their free accelerators from 100 to 20 per hour. So the spammers changed strategy. |
|
|
|
Ratters has made a total number of 507 posts, but according to archive, There are only 472 archived posts. Could this be a case of some posts not getting archived? Good find! I don't have this post for example. Even worse: I only have the first 20 posts from this topic with 6448 posts. I guess my scraping didn't catch the second page, my "page detection" had some flaws sometimes. Considering this shitcoin topic was abandoned in 2014, I won't update my scraping. I think the archival only archives posts after a given period of time. Those none archived posts were from before the archived date. I also scraped older posts. |
|
|
|
Quoting as Reference link for neutral feedback. Do not trade with me [BitcoinGirl.Club - 662330] unless a signed message is provided in a conversation using the following bitcoin address: bc1ql847ly3a0kaw6zhscc686a3lv7ve98qgay8422 My account can be hacked, stolen or anything that can happen which may not be in my hand. Anyone who will have a financial exchange without receiving a message which is signed by above address and without verifying it, is not going to demand any return from me. Fuck excuses! If you can not provide a signed message by me as a proof then I have not done any business with you. 05/01/2024
bc1ql847ly3a0kaw6zhscc686a3lv7ve98qgay8422
IBfqNQgdqx7qtOPu+EmNW0QpXc0eVNBJMILG6q3vut3bQ44LAgdf01hgeSemMopCMHVJ5N+L0HQhJw7qR3EpGaA= |
|
|
|
You locked it, so I'll reply here: anyone with access to your account can edit that post, and any potential trade partner won't easily find it back. If you unlock it, I can quote you there, and link my quote in neutral feedback. |
|
|
|
If anything happen to an account and the account takes any loan then the original account holder is responsible for it. I prefer a combination of common sense and signed messages: Watch for loan requests from users you wouldn't expect it from. If, for example, I would ask for a large loan, don't jump at the opportunity! I've never asked for a loan before, and this should be treated as a big red flag. |
|
|
|
|
My guess: accounts getting compromised is nothing new. But since you (OP) have handed out loans before without asking for a signed message, I guess the attacker just tries his luck with you again.
|
|
|
|
The way I do it is as soon as I write down the Seed, I close the Wallet, then re launch it and use the Restore option. Enter the Seed from the paper I just wrote and go from there. This isn't even enough: you should check if the seed creates the same address again. I prefer to test the seed with a different application. So when I setup a hardware wallet, I import the seed into Ian Coleman's software (of course running offline, air-gapped, running a Live Linux DVD from RAM, with the curtains closed on a computer that I'll burn in holy fire afterwards), and see if I can reproduce the same address by different means. It's a lot of work, but being thorough gives peace of mind. What I normally do whenever I create a new seed is to snap it with another phone This turns a hot wallet into an even hotter wallet. You're basically doubling the malware risk. |
|
|
|
|
Of course high fees affect adoption! We're basically back to the problem we had in 2017. I'd love to make ten times more Bitcoin transactions than I'm currently doing, but it's simply not possible. And even if I'd pay the very high fees, it means I'm pushing someone else's transaction out. Bitcoin can't have more active users without more transactions.
|
|
|
|
So, like I say Coca-Cola, I don't generate any traffic for that company. But, if I say Coca-Cola, I will generate traffic for that company. (I'm not trying to advertise)  But if it's a less well known brand, and Google pops up cocac0la.com, you'll end up on a phishing site. They (people) will know how to not fall in a phishing site. Phishing sites wouldn't exist without people falling for them. |
|
|
|
I refreshed the page and after the second refresh, I got the following message from cloudflare. The owner of this website ( www.viabtc.com) has banned you temporarily from accessing this website. I've seen that too, it only took a few refreshes. But somehow it's not stopping the bots. For now, it looks like the spammers all go for 23 sat/vbyte, and anything above 30 sat/vbyte has a reasonsable chance to get confirmed. Anything under 23 sat/vbyte is futile, and will very soon be low enough to be dropped out of (most) mempools. |
|
|
|
|
Last night, my data scraping resulted in some failures again. The API is clearly not up for it, and I don't really want to keep checking this daily for the rest of the year. If it keeps failing, I'll have to give up.
I'm re-scraping it now.
|
|
|
|
I have the client running, go to CMD to run the command "bitcoin-cli getblockchaininfo" that Tether has mentioned in the original post, but receive this error.  You have the GUI-client running, not the daemon. So click Window > Console, and enter getblockchaininfo there. Don't use bitcoin-cli with the GUI. Supposedly, it'll only take 3 more days. In my experience, it gets slower once blocks get larger. I have 8GB RAM. How much dbcache should I choose then? I would set it to 4096. But if the rest of your system needs RAM too, it's going to slow down everything with active swapping. So is there any risk of damaging hardware/device? It could be a problem wasn't noticed before until the system was under heavy load. |
|
|
|
What about this oneShould it be locked or I can keep going on it? As you can notice, I removed any URL, I only mention the names and it has been say we can still discuss mixers. Searching for the mixer's names will pop up countless phishing sites, so I don't think there's a point to continue this without URLs. |
|
|
|
|